Automatic on-premises Exchange Server mitigation now in Microsoft Defender Antivirus
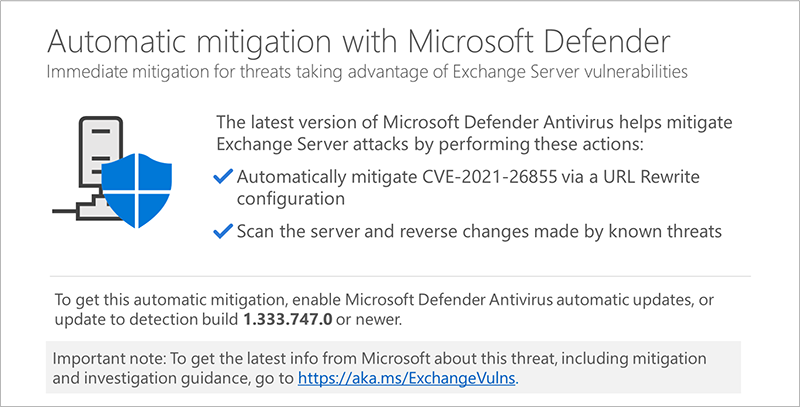
Microsoft Defender Antivirus and System Center Endpoint Protection will automatically mitigate CVE-2021-26855 on any vulnerable Exchange Server on which it is deployed. We have taken this additional step to further support our customers who are still vulnerable and have not yet implemented the complete security update.
The post Automatic on-premises Exchange Server mitigation now in Microsoft Defender Antivirus appeared first on Microsoft Security. READ MORE HERE…