Mitigate threats with the new threat matrix for Kubernetes
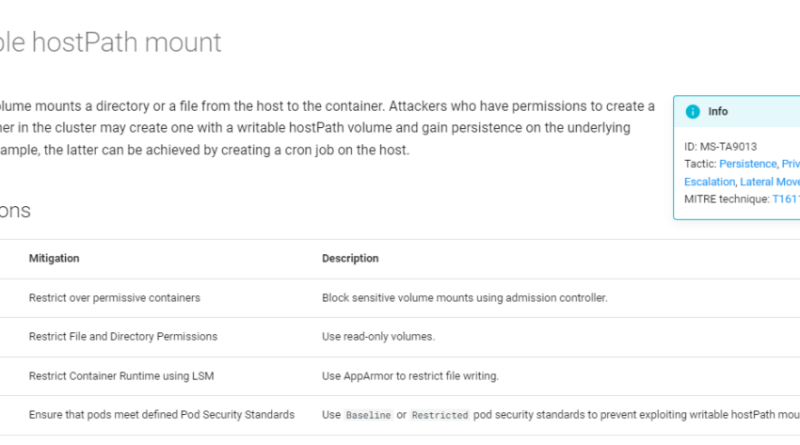
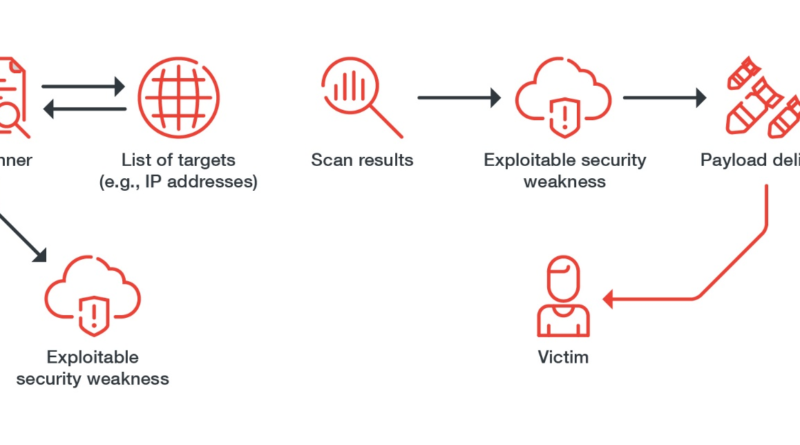
The updated threat matrix for Kubernetes comes in a new format that simplifies usage of the knowledge base and with new content to help mitigate threats.
The post Mitigate threats with the new threat matrix for Kubernetes appeared first on Microsoft Security Blog. READ MORE HERE…