New “Prestige” ransomware impacts organizations in Ukraine and Poland
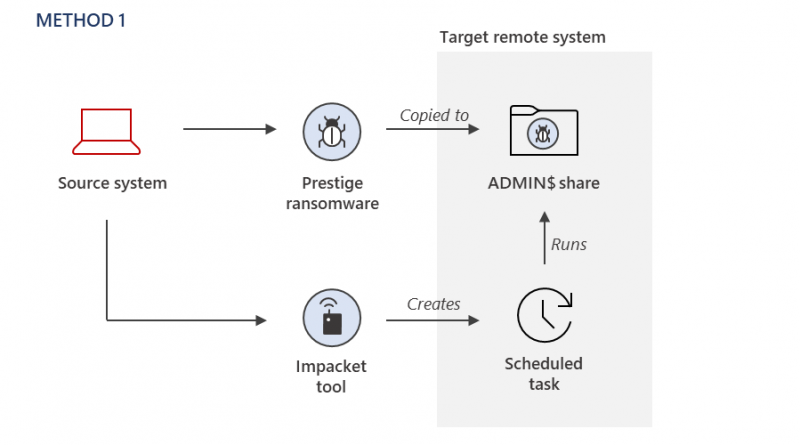
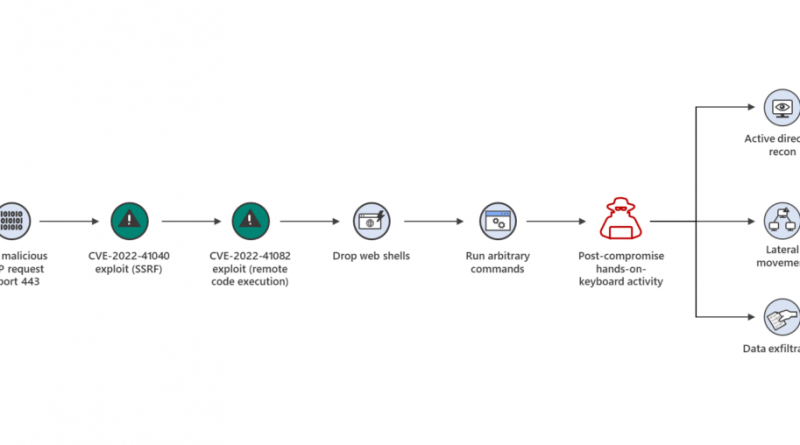
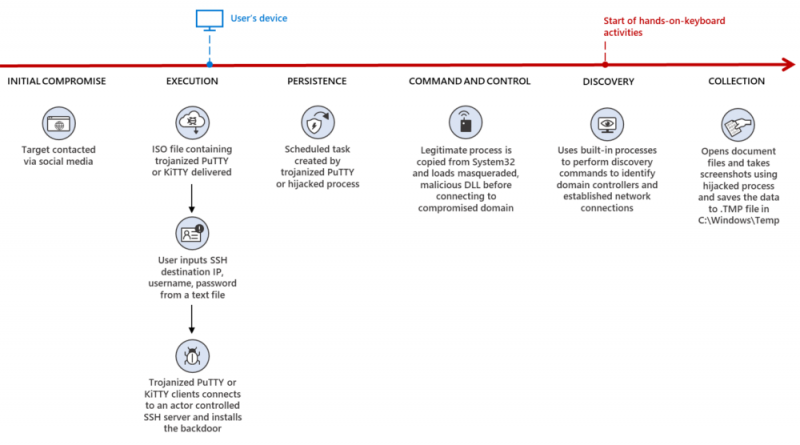
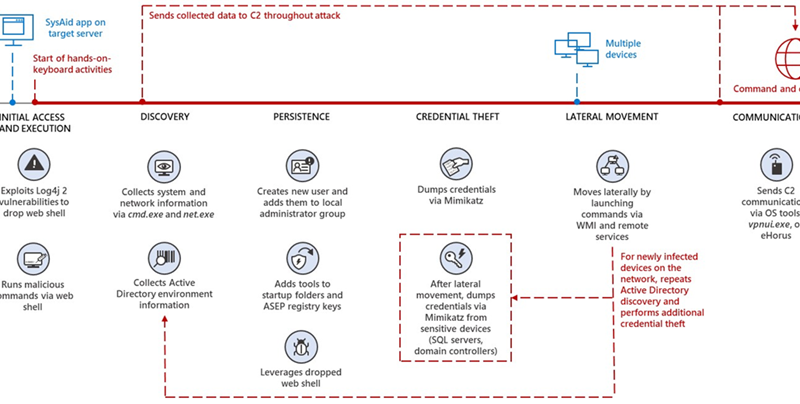
The Microsoft Threat Intelligence Center (MSTIC) has identified evidence of a novel ransomware campaign targeting organizations in the logistics and transportation industry in Ukraine and Poland utilizing a previously unidentified ransomware payload.
The post New “Prestige” ransomware impacts organizations in Ukraine and Poland appeared first on Microsoft Security Blog. READ MORE HERE…