ZINC weaponizing open-source software
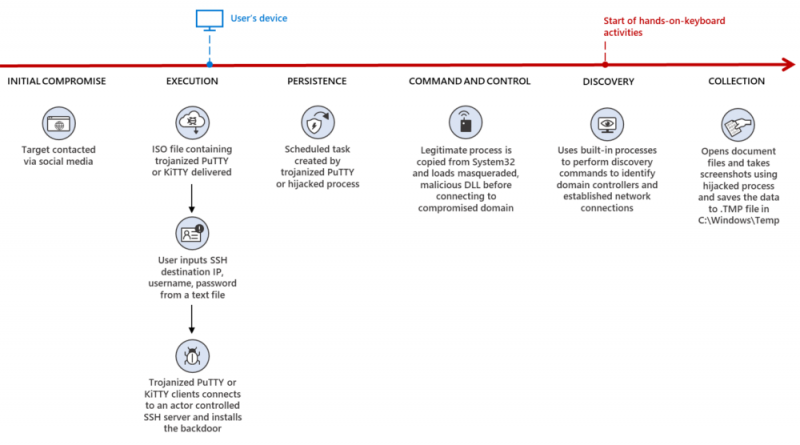
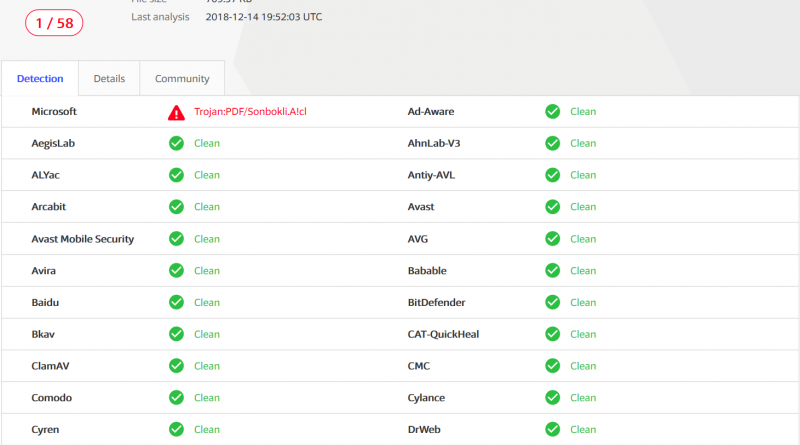
In recent months, Microsoft detected weaponization of legitimate open-source software by an actor the Microsoft Threat Intelligence Center (MSTIC) tracks as ZINC, targeting employees at media, defense and aerospace, and IT service provider organizations in the US, UK, India, and Russia.
The post ZINC weaponizing open-source software appeared first on Microsoft Security Blog. READ MORE HERE…