Trend Micro Research : Cyber Crime
Tailing Big Head Ransomware’s Variants, Tactics, and Impact
We analyze the technical details of a new ransomware family named Big Head. In this entry, we discuss the Big Head ransomware’s similarities and distinct markers that add more technical details to initial reports on the ransomware. Read More HERE…
How to Deploy Generative AI Safely and Responsibly
New uses for generative AI are being introduced every day—but so are new risks. Read More HERE…
SeroXen Mechanisms: Exploring Distribution, Risks, and Impact
This is the third installment of a three-part technical analysis of the fully undetectable (FUD) obfuscation engine BatCloak and SeroXen malware. In this entry, we document the techniques used to spread and abuse SeroXen, as well as the security risks, impact, implications of, and insights into highly evasive FUD batch obfuscators. Read More HERE…
Generative AI Assistant Makes Hunting Threats Faster
Learn how analysts can search for threats with greater accuracy, speed, and effectiveness. Read More HERE…
Analyzing the FUD Malware Obfuscation Engine BatCloak
We look into BatCloak engine, its modular integration into modern malware, proliferation mechanisms, and interoperability implications as malicious actors take advantage of its fully undetectable (FUD) capabilities. Read More HERE…
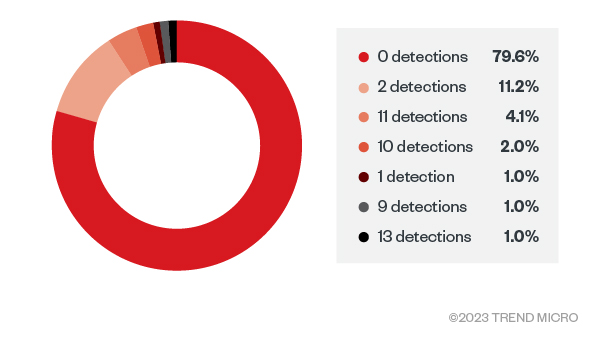
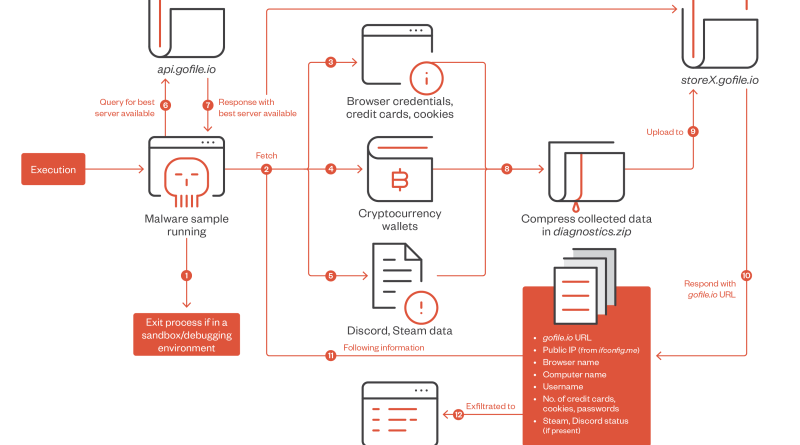
Rust-Based Info Stealers Abuse GitHub Codespaces
This is the first part of our security analysis of an information stealer targeting GitHub Codespaces (CS) that discusses how attackers can abuse these cloud services for a variety of malicious activities. Read More HERE…
Lemon Group’s Cybercriminal Businesses Built on Preinfected Devices
An overview of the Lemon Group’s use of preinfected mobile devices, and how this scheme is potentially being developed and expanded to other internet of things (IoT) devices. This research was presented in full at the Black Hat Asia 2023 Conference in Singapore in May 2023. Read More HERE…
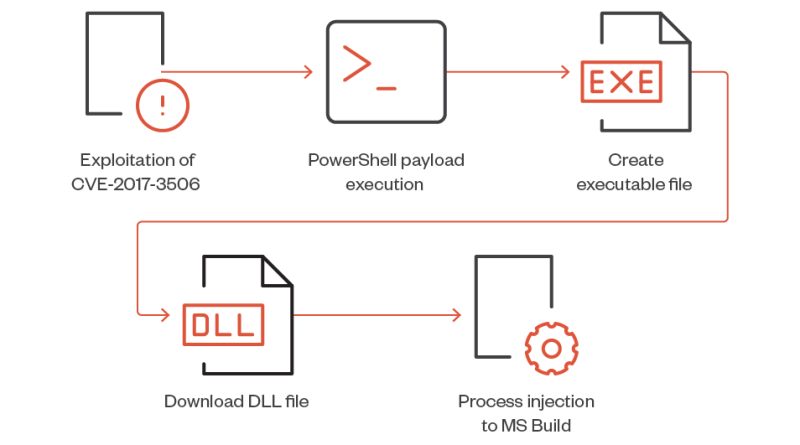
8220 Gang Evolves With New Strategies
We observed the threat actor group known as “8220 Gang” employing new strategies for their respective campaigns, including exploits for the Linux utility “lwp-download” and CVE-2017-3506, an Oracle WebLogic vulnerability. Read More HERE…
Attackers Use Containers for Profit via TrafficStealer
We found TrafficStealer abusing open container APIs in order to redirect traffic to specific websites and manipulate engagement with ads. Read More HERE…