Lemon Group’s Cybercriminal Businesses Built on Preinfected Devices


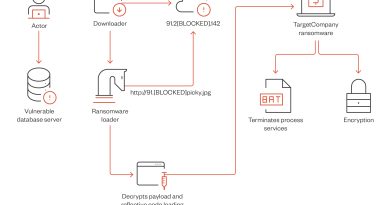
1) SMS plugin: Capable of intercepting received SMS and read specific messages such as one-time passwords (OTP) from various platforms such as WhatsApp, JingDong (a shopping app), and Facebook. This plugin feeds the business of SMS PVA, which provides phone numbers and OTP features for their customers.
2) Proxy plugin and proxy seller: Able to setup reverse proxy from an infected phone and use the network resources of the affected mobile device in exchange for their DoveProxy business.
3) Cookie plugin/WhatsApp plugin/Send plugin and promotion platform:
a. The cookie plugin hooks to Facebook-related apps and intercepts specific activities to launch events (e.g., Facebook app’s list of activities). It also dumps Facebook-related cookies from the app data directory and uploads it to the C&C server. This plugin can also harvest other data like the Friends list, profile, email addresses, and others.
b. The WhatsApp plugin is used to hijack WhatsApp sessions to send unwanted messages. These two were used for “overseas marketing” so the customers can use compromised Facebook accounts and boost their marketing platform by posting on Facebook on behalf of the compromised accounts. Registering a Facebook account has now become more difficult and can be banned due to malicious activities coming from newly created accounts, so these list of compromised accounts are perfect for marketing purposes.
4) Splash plugin: Hook popular apps to intercept specific activities such as launching event request ads from advertisements. Victims will see unexpected ads while launching official apps on their devices.
5) Silent plugin: When any activity needs an installation permission, it gets a list of tasks from the C&C, and each task includes apk (Android Package) metadata and the action, such as install and uninstall. This plugin executes the silent installation and launches the installed app.
Rebranding and impact
When we published a research paper on the operations of Lemon Group in February 2022, the group changed their operation name. In May, they removed some traces of “Lemon” and rebranded as “Durian Cloud SMS.” However, the servers are still the same and intact.
Through our monitoring, we have detected over 490,000 mobile numbers used for OTP requests of Lemon SMS and, later, Durian SMS service. The customers of Lemon SMS PVA generated OTPs from platforms like JingDong, WhatsApp, Facebook, QQ, Line, and Tinder, among other applications.
Tracking the indicators using Trend Micro™ Smart Protection Network™, the number of infected devices are distributed globally as the threat actor controls devices in more than 180 countries. The top 10 countries affected:
- US
- Mexico
- Indonesia
- Thailand
- Russia
- South Africa
- India
- Angola
- Philippines
- Argentina
Read More HERE