The Risk of Ransomware Supply Chain Attacks

Ransomware has been a major threat to cybersecurity throughout the years, dominating boardroom discussions. It is a type of malware that prevents or limits users from accessing their systems. Malicious actors lock the system’s screen or user files until a hefty ransom is paid.
First seen in Russia between 2005 and 2006, ransomware’s popularity as a business model spread across the globe. By 2012, Trend Micro has observed a continuous spread of infections across Europe and North America.
Ransomware has also reached a new height during the pandemic; one analysis reveals a 105% surge in ransomware last year with hundreds of millions of attacks detected. The surge is due to capitalizing on digital investment and remote work.
Moreover, ransomware-as-a-service offerings have attracted a new breed of malicious groups, which then increased the volume and variety of threats. Initial access brokers (IABs) often provide an entry point, phishing attack or RDP compromise. Then the affiliate takes the offer, utilizing various tools to move and exfiltrate data and deliver their ransomware payload.
Major organizations are singled out in sophisticated “big game hunting” attacks while SMBs suffer in even greater numbers. Double, triple and even quadruple extortion have become commonplace ways to force payment. And some of the most aggressive groups like Conti and REvil make billions.
Ransomware incidents
Over the past two years alone, ransomware has infected major organizations, causing millions of dollars in damages.
Kaseya
On July 2021, Kaseya announced its system was infiltrated, impacting about 1,500 organizations that use the company’s services. REvil claimed responsibility for the attack and demanded a few thousand to $5 million. The company declined to pay and worked with the FBI and CISA, obtaining a universal decryptor key.
Benttag
Benttag had 150GB worth of data stolen from its North American Division in May 2021. DarkSide took responsibility and demanded a ransom of $7.5 million but accepted $4.4 million in bitcoin after days of negotiation.
Colonial Pipeline
Also in May 2021, the Colonial Pipeline incident made news all over the globe. The attack forced the largest fuel pipeline in the US to halt operation. DarkSide was able to breach the company’s system through a virtual private network account, which allowed employees to access the company’s network. Apart from locking Colonial Pipeline’s computer systems, DarkSide also stole over 100 GB of corporate data.
Nvidia
In February 2022, the world’s largest semiconductor chip company was infiltrated by a ransomware attack. The group behind the breach, LAPSUS$, claimed it took 1TB of data, including files about Nvidia hardware and software. The hackers demanded the company pay up in cryptocurrency to keep the data secret. Nvidia swiftly responded by tightening its security and working with cyber incident response experts to contain the situation.
Ransomware supply chain risk
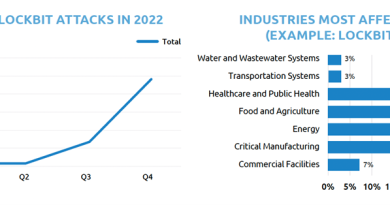
Ransomware is now present in 25% of data breaches, a 13% year-on-year increase. The volume of reports to the FBI, itself representing just the tip of the iceberg, jumped 109% from 2017 to 2021.
And because malicious groups are always looking for a handsome payday, supply chains have become an attractive target. Supply chains can offer either a poorly defended access vector and/or an opportunity to multiply profits by infecting many organizations through a single supplier.
The corporate attack surface is also increasingly distributed – across an extensive supply chain that spans cloud and software providers, professional services firms and other connected entities. Each one of these may have privileged network access or store sensitive information belonging to client organizations.
Each one, therefore, represents a potential security risk that must be addressed. Yet too often supply chains are nebulous and ill-defined, with controls applied in a reactive and haphazard manner, if at all. This must change.
What we found
To learn more, Trend Micro commissioned Sapio Research to interview 2958 IT Decision Makers across 26 countries: UK, Belgium, Czech Republic, Netherlands, Spain, Sweden, Norway, Finland, Denmark, France, Germany, Switzerland, Austria, USA, Italy, Canada, Taiwan, Japan, Australia, India, Poland, Hong Kong, Mexico, Colombia, Chile, Brazil.
It is vital to have transparency around the risk of ransomware to improve supply chain security. However, only 47% of organizations we interviewed share knowledge about ransomware attacks with their supplies. Twenty-five percent also say they don’t share potentially useful threat information with partners. Moreover, detection rates were also alarming low for ransomware activities:
Read More HERE