Closing the Door: DeadBolt Ransomware Locks Out Vendors With Multitiered Extortion Scheme
The dark blue line in the survival analysis in Figure 8 shows the date range when victims paid the ransom amount. In this analysis, the victims that do not pay the ransom amount are referred to as survivors, while those who do are referred to as terminal. This analysis allows us to better understand the science of ransomware and ransom payout prevention.
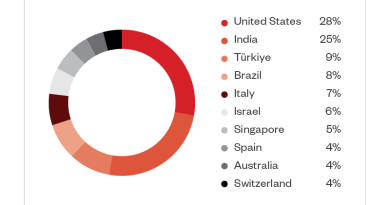
We can go further and say that for about 5 to 7.5 bitcoins (roughly US$200,000 to US$300,000 as of this publishing), they would be willing to give away their methods — we are, however, only taking them for their word, which admittedly is on the charitable side. On the other hand, the charitable assumption on our end allows for this analysis. It’s also possible that DeadBolt actors think that a conversion ratio of 6% (300,000 divided by 4,400,000) is substantial enough to cash out. They obviously know a lot more about payment ratios than we do, because they eventually topped out at 8%.
It’s also clear that they knew in advance that US$300,000 would have been a good, low-risk deal. That in turn suggests that the entire operation cost them less than US$150,000, otherwise their profit margins would be undesirable. However, it’s worth noting that the fact that 92% of victims have chosen not to pay ransom is an enormous success in cybersecurity — one that we often choose to ignore; instead, we tend to focus on how much ransomware actors have earned in their attacks.
Let’s try to understand the economic damage that DeadBolt has caused as best as we can. Presumably, for those who paid ransom, their financial losses would have been greater than 0.03 bitcoins (roughly US$1,000 at that time of publishing). For those who didn’t pay ransom, we can reasonably assume that their losses were lower, between zero to US$1,000. We can simplify the matter and suggest that their financial losses could be US$500 on the average.
(0.08 4,988 × 1,000) + (0.92 × 4,988 × 500) = 2,693,520
Based on this calculation, DeadBolt causes about US$2,693,520 worth of economic damage to earn US$300,000. It’s also interesting to think that the US$300,000 amount that they are asking for in exchange of the vulnerability details would probably be split among multiple members of the DeadBolt operation. Based on these numbers, DeadBolt actors are running the risk of incarceration for demanding millions of dollars from their victims, for a chance to earn only thousands, which doesn’t seem to be a sensible risk quantification.
Is it about the money, therefore, or about the damage caused? Are DeadBolt actors punishing society at large or just specific vendors? Or does this represent a refined business model that focuses on automation and volume, along with a chance to get a large single payout from affected vendors? These are some of the questions that we are left with after investigating ransomware groups such as DeadBolt.
Security recommendations
Users and organizations can keep their NAS devices secure by implementing the following security recommendations:
- Regularly update your NAS devices. Make sure that the latest patches have been installed as soon as they are available.
- Keep NAS devices offline. If you need to access your NAS device remotely, do it securely by opting to use either your NAS vendor’s remote access services (which most major NAS vendors offer) or use a virtual private network (VPN) solutions.
- Use a strong password and two-factor authentication (2FA). Do not use weak passwords or default credentials. If your NAS device supports 2FA, enable it to add an extra layer of protection against brute force attacks.
- Keep your connection and ports secure. Keep incoming and outgoing traffic secure by enabling HTTPs instead of HTTP. Remember to close all unused communication ports and change default ports.
- Shut down or uninstall unused and out-of-date services. Remove unused or out-of-date services to reduce the risk of NAS device compromise.
Conclusion
Overall, the total ransom amount that was paid was low in comparison to the number of infected devices, which led us to the conclusion that most people didn’t pay the ransom. It’s also worth pointing out that DeadBolt’s ransom amount costs more than the price of a brand-new NAS device, which is possibly why majority of its victims were not willing to pay to keep their data. Presumably, if the cost was higher, even more victims would be less likely to pay. The goal of DeadBolt actors is to infect as many victims as possible to get a decent payout or to get a vendor to pay one of the ransom options to get substantial financial payouts from its attacks.
Even though the vendor master decryption key did not work in DeadBolt’s campaigns, the concept of holding both the victim and the vendors ransom is an interesting approach. It’s possible that this approach will be used in future attacks, especially since this tactic requires a low amount of effort on the part of a ransomware group.
DeadBolt represents several innovations in the ransomware world: It targets NAS devices, has a multitiered payment and extortion scheme, and has a flexible configuration. But perhaps its main contribution to the ransomware ecosystem will be the legacy of its heavily automated approach. There is a lot of attention on ransomware families that focus on big-game hunting and one-off payments, but it’s also important to keep in mind that ransomware families that focus on spray-and-pray types of attacks such as DeadBolt can also leave a lot of damage to end users and vendors.
| SHA-256 | Detection |
| 3c4af1963fc96856a77dbaba94e6fd5e13c938e2de3e97bdd76e1fca6a7ccb24 | Ransom.Linux.DEADBOLT.YXCEP |
| 80986541450b55c0352beb13b760bbd7f561886379096cf0ad09381c9e09fe5c | Ransom.Linux.DEADBOLT.YXCEP |
| e16dc8f02d6106c012f8fef2df8674907556427d43caf5b8531e750cf3aeed77 | Ransom.Linux.DEADBOLT.YXCEP |
| acb3522feccc666e620a642cadd4657fdb4e9f0f8f32462933e6c447376c2178 | Ransom.Linux.DEADBOLT.YXCEP |
| 14a13534d21d9f85a21763b0e0e86657ed69b230a47e15efc76c8a19631a8d04 | Ransom.Linux.DEADBOLT.YXCEP |
| 444e537f86cbeeea5a4fcf94c485cc9d286de0ccd91718362cecf415bf362bcf | Ransom.Linux.DEADBOLT.YXCEP |
Yara rules
rule deadbolt_cgi_ransomnote : ransomware {
meta:
description = “Looks for CGI shell scripts created by DeadBolt”
author = “Trend Micro Research”
date = “2022-03-25”
hash = “4f0063bbe2e6ac096cb694a986f4369156596f0d0f63cbb5127e540feca33f68”
hash = “81f8d58931c4ecf7f0d1b02ed3f9ad0a57a0c88fb959c3c18c147b209d352ff1”
hash = “3058863a5a169054933f49d8fe890aa80e134f0febc912f80fc0f94578ae1bcb”
hash = “e0580f6642e93f9c476e7324d17d2f99a6989e62e67ae140f7c294056c55ad27”
strings:
$= “ACTION=$(get_value \”$DATA\” \”action\”)”
$= “invalid key len”
$= “correct master key”
$= “‘{\”status\”:\”finished\”}'”
$= “base64 -d 2>/dev/null”
condition:
uint32be(0) != 0x7F454C46 // We are not interested on ELF files here
and all of them
}
rule deadbolt_uncompressed : ransomware {
meta:
description = “Looks for configuration fields in the JSON parsing code”
author = “Trend Micro Research”
date = “2022-03-23”
hash = “444e537f86cbeeea5a4fcf94c485cc9d286de0ccd91718362cecf415bf362bcf”
hash = “80986541450b55c0352beb13b760bbd7f561886379096cf0ad09381c9e09fe5c”
hash = “e16dc8f02d6106c012f8fef2df8674907556427d43caf5b8531e750cf3aeed77”
strings:
$= “json:\”key\””
$= “json:\”cgi_path\””
$= “json:\”client_id\””
$= “json:\”vendor_name\””
$= “json:\”vendor_email\””
$= “json:\”vendor_amount\””
$= “json:\”payment_amount\””
$= “json:\”vendor_address\””
$= “json:\”master_key_hash\””
$= “json:\”payment_address\””
$= “json:\”vendor_amount_full\””
condition:
elf.type == elf.ET_EXEC
and all of them
}
Read More HERE