Amazon Comes Under Fire for Facial Recognition Platform
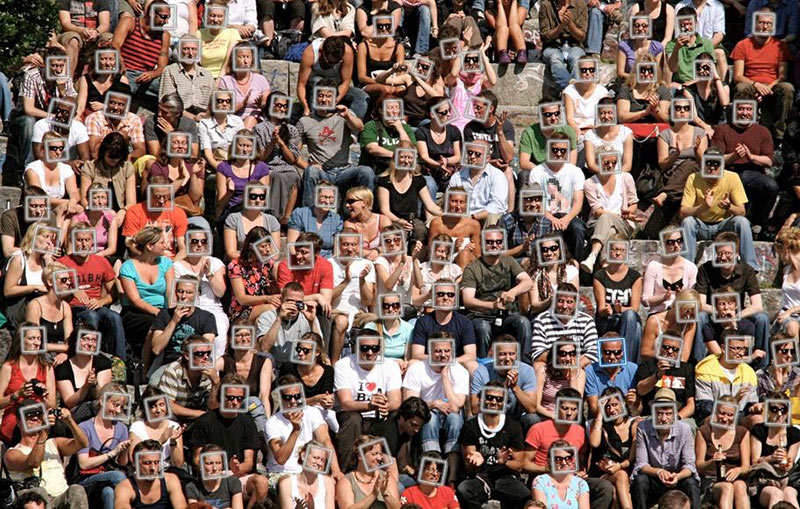
Privacy advocates say facial recognition can be an agent of authoritarian surveillance; others say it’s an invaluable tool to combat kidnapping, locate lost children and track down criminals on the run. READ MORE HERE…