KillNet and affiliate hacktivist groups targeting healthcare with DDoS attacks
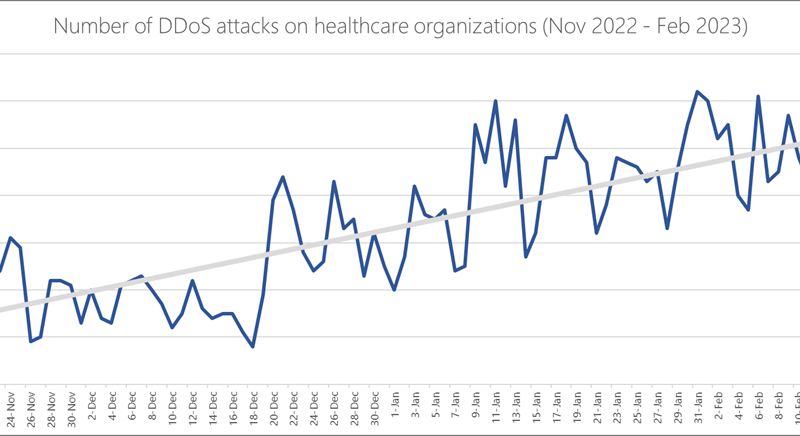
KillNet, a group that the US Department of Health and Human Services (DHHS) has called pro-Russia hacktivists, has been launching waves of attacks targeting governments and companies with focus on the healthcare sector. In this blog post, we provide an overview of the DDoS attack landscape against healthcare applications hosted in Azure over three months.
The post KillNet and affiliate hacktivist groups targeting healthcare with DDoS attacks appeared first on Microsoft Security Blog. READ MORE HERE…