Microsoft unifies SIEM and XDR to help stop advanced attacks
For all of us in security, the last twelve months have been an incredible series of challenges—from balancing remote work with family priorities, to helping build resilient businesses, and protecting against the latest attacks. 2020 showed us that while we have made great progress, there is still a lot we can do as individuals, organizations, and as a community to keep secure. Here at Microsoft, we’re committed to applying these learnings to help create a stronger, more unified approach to security for all—no matter what platform you’re on, device you’re trying to protect, or cloud your data is in.
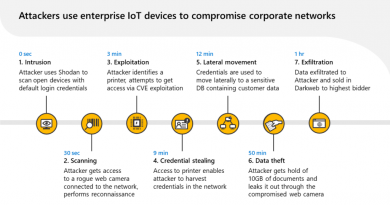
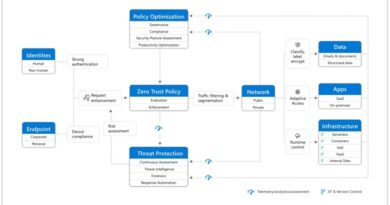
To help protect against advanced attacks, last September at Microsoft Ignite we shared our vision to create the most complete approach to securing your digital landscape, all under a single umbrella. We combined the breadth of Azure Sentinel, our cloud-native SIEM (security information and event management) with the depth of Microsoft 365 Defender and Azure Defender, our XDR (extended detection and response) tools, to help fight against attacks that take advantage of today’s diverse, distributed, and complex environments.
Today we are taking the next step in unifying these experiences and delivering enhanced tools and intelligence to stop modern threats.
Unified experiences
Most SIEMs on the market today simply take logs from multiple sources. Azure Sentinel accepts logs across your environment with many third-party security products and can go a step further with Azure Defender and Microsoft 365 Defender. Starting today, incidents, schema, and alerts are shared between Azure Sentinel and Microsoft 365 Defender. This means you get a unified view in Azure Sentinel, then can seamlessly drill down into an incident for more context in Microsoft 365 Defender.
For example: Start in Azure Sentinel for your bird’s eye view to understand an overarching incident, then move directly into Microsoft 365 Defender to investigate an asset or a user in more detail. You can even remediate and close the incident directly within Microsoft 365 Defender, all while maintaining bi-directional syncing with Azure Sentinel. This is next level SIEM integration you won’t find anywhere else.
On the Microsoft 365 Defender side, we are working to reduce the number of portal experiences. The goal is to have a single unified XDR experience for securing end-user environments, rather than a suite of products. Today marks a significant milestone in that effort as we integrate the capabilities of Microsoft Defender for Endpoint and Defender for Office 365 together into the unified Microsoft 365 Defender portal. These changes simplify tasks that would require multiple experiences across comparable products in the market. We have also taken the opportunity to significantly enhance the email entity page with a new 360-degree view of email alerts with relevant context and email alert capabilities.
Enhanced tools and intelligence to stop advanced attacks
As well as unifying the capabilities of Microsoft Defender for Endpoint and Defender for Office 365 into Microsoft 365 Defender, we have also created new enhanced experiences including:
- Threat Analytics, now in preview, provides detailed threat intelligence reports from expert Microsoft security researchers that help you understand, prevent, and mitigate active threats.
- Learning Hub where you can use instructional resources with best practices and how-tos.
- Attack Simulation Training in Microsoft Defender for Office 365 which helps you detect, prioritize, and remediate phishing risks. It uses neutralized versions of real attacks to simulate the continually changing attacker landscape, enabling highly accurate and up-to-date detection of risky behavior, with rich reporting and analytics to help customers measure their progress.
With Azure Sentinel, we’re focused on giving you a richer organization-wide view with expanded data collection and helping you to respond faster with new incident response and automation capabilities. Today we are announcing more than 30 new connectors to simplify data collection across your entire environment, including multi-cloud environments. These new connectors include Salesforce service cloud, VMWare, Cisco Umbrella, and Microsoft Dynamics.
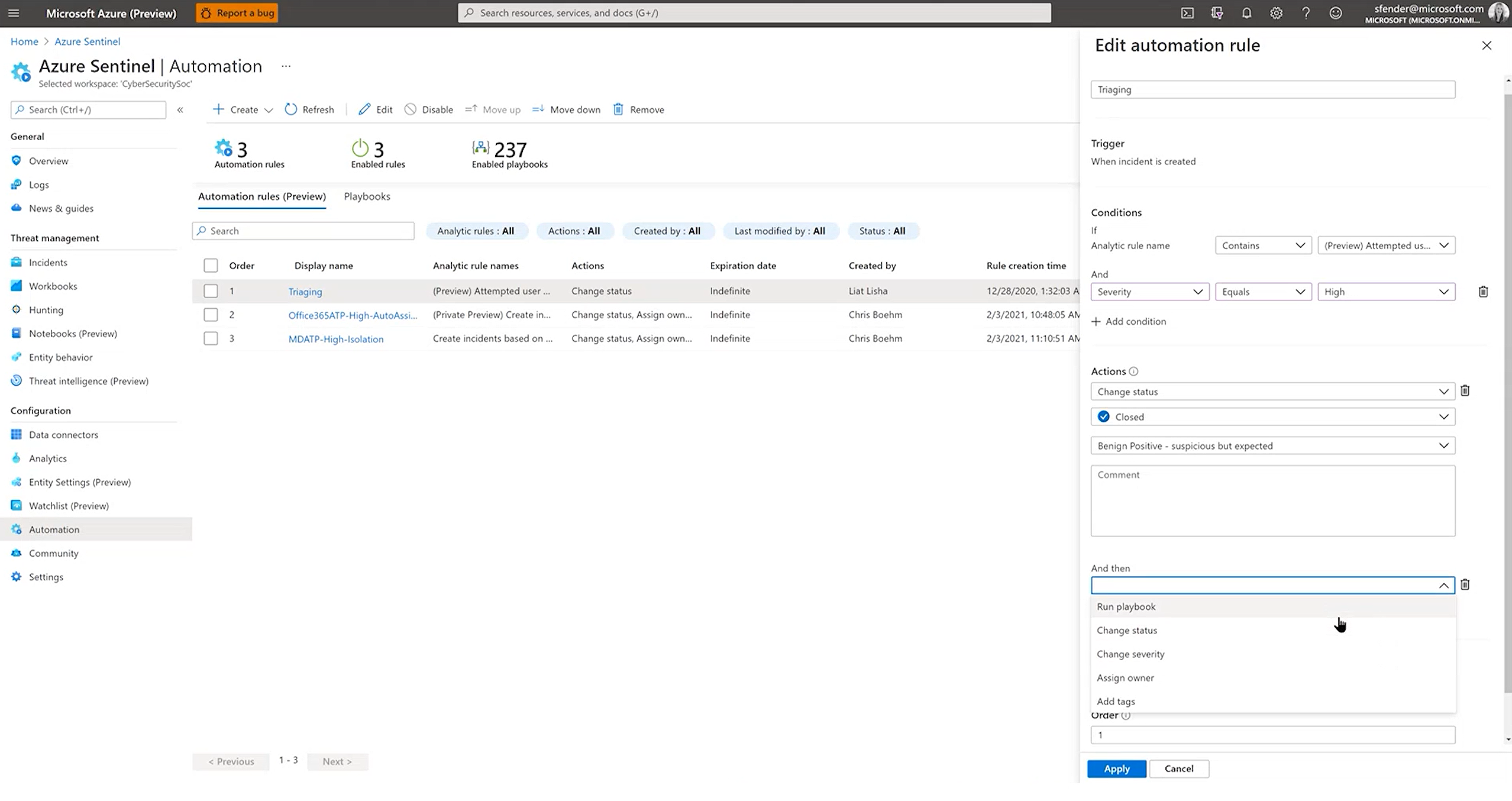
We’re also expanding Azure Sentinel’s SOAR capabilities. Today we’re introducing automation rules (a new and simple framework for automating common tasks), and new automation connectors with additional built-in SOAR playbooks. These new playbooks enable automation workflows such as blocking a suspicious IP address with Azure Firewall, isolating endpoint devices with Microsoft Intune, or updating the risk state of a user with Azure Active Directory Identity Protection. You can learn more about these Azure Sentinel innovations on the Azure Sentinel Microsoft Ignite 2021 announcement blog.
Finally, Azure Defender now provides improved alerts features, including improved triaging experience with better performance for larger alert lists, alerts from Azure Resource Graph, sample creation feature for Azure Defender alerts, and alignment with Azure Sentinel’s incident experience. To learn more about these and other Azure Security Center announcements, please read the Azure Security Center Microsoft Ignite 2021 announcement blog.

Looking ahead
We’ve been on a long journey to figure out how to understand and help you protect against advanced attacks. We’re only just getting started on our mission and will continue to unify tools and add intelligence to help keep your environment healthy and secure.
Be sure to check out our Microsoft Ignite session, and learn more about our SIEM + XDR offering.
As always, thank you for your continued partnership on this journey.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
-Rob, Eric, and our entire Microsoft Security Team
READ MORE HERE