Sophisticated cybersecurity threats demand collaborative, global response

Microsoft’s response to Solorigate
Since December, the United States, its government, and other critical institutions including security firms have been addressing the world’s latest serious nation-state cyberattack, sometimes referred to as ‘Solorigate’ or ‘SUNBURST.’ As we shared earlier this is a moment of reckoning for our industry and needs a unified response of defenders across public and private sectors. Microsoft is committed to protecting our customers and safeguarding our communities and we are proud to partner with industry partners to respond to this attack and strengthen our collective defenses. We believe transparency and clarity are important for strong cybersecurity and in that spirit, we are sharing information about some commonly asked questions. We look forward to serving and protecting our customers and communities.
Question: What has Microsoft’s role been in the Solorigate incident?
Answer:
As Brad Smith wrote on December 17, 2020, Solorigate is a moment of reckoning for security. We believe the Solorigate incident is an opportunity for the industry to work together to share information, strengthen defenses, and respond to attacks. We are proud to be part of the collaborative work being done to empower the defender community. Over the past two months, there have been several disclosures related to the Solorigate actor and Microsoft has had a unique perspective from several angles:
- Helping investigate with FireEye.
- Using indicators to find unusual activity and notifying customers and partners.
- Helping with customer investigations.
- Investigating our own environment.
In all of our investigations to date, data hosted in Microsoft services (including email) was sometimes a target in the incidents, but the attacker had gained privileged credentials in some other way.
Find the latest findings and guidance on Solorigate here.
Question: With your broad engagement, you’ve been criticized for not disclosing details as soon as you knew about them. How do you respond?
Answer:
We believe the Solorigate incident is an opportunity for the industry to work together to share information, strengthen defenses, and respond to attacks.
We have a very talented and experienced cybersecurity response team. In those situations where we provide investigative support to other organizations, we are restricted from sharing details. In these engagements, as well as when we notify organizations, those organizations have control in deciding what details they disclose and when they disclose them.
Additionally, investigations sometimes discover early indicators that require further research before they are actionable. Taking the time to thoroughly investigate incidents is necessary in order to provide the best guidance to the broader security community, our customers, and our partners.
We share actionable information regularly on our Solorigate resource center, and we are committed to providing additional updates if and when we discover new information to help inform and enable the community.
Question: The Cybersecurity & Infrastructure Security Agency (CISA) says other attack vectors have been discovered apart from SolarWinds. Has Microsoft in any way been an initial entry point for the Solorigate actor?
Answer:
No. In our investigations to date, data hosted in Microsoft services (including email) was sometimes a target in the incidents, but the attacker had gained privileged credentials in some other way.
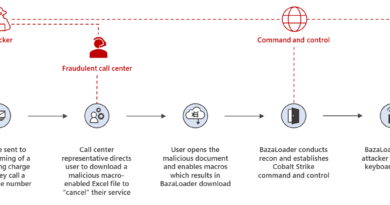
From the beginning, we have said that we believe this is a sophisticated actor that has many tools in its toolkit, so it is not a surprise that a sophisticated actor would also use other methods to gain access to targets. In our investigations and through collaboration with our industry peers, we have confirmed several additional compromise techniques leveraged by the actor, including password spraying, spearphishing, use of webshell, through a web server, and delegated credentials.
As we learn more from our engagements, we will continue to improve our security products and share learnings with the community. For the most up-to-date information and guidance, please visit our resource center.
Question: What should we know about the Microsoft notifications to customers? Does that mean you detected a compromise in Microsoft services?
Answer:
No, it means our telemetry indicated unusual activity in authorized accounts.
As part of the investigative team working with FireEye, we were able to analyze the attacker’s behavior with a forensic investigation and identify unusual technical indicators that would not be associated with normal user interactions. We then used our telemetry to search for those indicators and identify organizations where credentials had likely been compromised by the Solorigate actor.
Microsoft directly notifies the affected customers to provide the indicators they need to investigate the observed behavior with their organizational knowledge and within their specific context.
Question: Some have interpreted the wording in the SolarWinds 8K to mean that they were made aware of or were investigating an attack vector related to Microsoft Office 365. Has that been investigated?
The 8K wording is, “SolarWinds uses Microsoft Office 365 for its email and office productivity tools. SolarWinds was made aware of an attack vector that was used to compromise the Company’s emails and may have provided access to other data contained in the Company’s office productivity tools.”
Answer:
We have investigated thoroughly and have found no evidence they were attacked via Office 365. The wording of the SolarWinds 8K filing was unfortunately ambiguous, leading to erroneous interpretation and speculation, which is not supported by the results of our investigation. SolarWinds has confirmed these findings in their blog on February 3, 2021.
Question: Reuters broke news on December 17, 2020, alleging that “Microsoft’s own products were then used to further the attacks” and saying it was not immediately clear “how many Microsoft users were affected by the tainted products.” Is that article accurate?
Answer:
No, it is not accurate. As we said at the time, and based upon all investigations since, we have found no indications that our systems were used to attack others. Data hosted in Microsoft services (including email) were sometimes a post-compromise target of attack, but only after an attacker had gained privileged credentials in some other way.
Question: Some companies say the hackers entered its systems via Microsoft products. Do you dispute this?
Answer:
We’ve investigated each situation as we became aware of it and in each case, data hosted in Microsoft services (including email) were a target in the incident, but the attacker had gained privileged credentials in another way.
Question: When did Microsoft know about being attacked by the Solorigate actor?
Answer:
Our security teams work continually to protect users, devices, and data from ongoing threats to our environment, but the investigations specifically focused on the Solorigate actor began when we became aware of the malicious SolarWinds applications.
We published a Microsoft Internal Solorigate Investigation Update on December 31, 2020, and will provide another update soon.
Question: Given how serious Solorigate is, what can be done? What is the big takeaway?
Answer:
The cybersecurity industry has long been aware that sophisticated and well-funded actors were theoretically capable of advanced techniques, patience, and operating below the radar, but this incident has proven that it isn’t just theoretical.
We believe the Solorigate incident has proven the benefit of the industry working together to share information, strengthen defenses, and respond to attacks.
Additionally, the attacks have reinforced two key points that the industry has been advocating for a while now—defense-in-depth protections and embracing a zero trust mindset.
Defense-in-depth protections and best practices are really important because each layer of defense provides an extra opportunity to detect an attack and take action before they get closer to valuable assets. We saw this ourselves in our internal investigation, where we found evidence of attempted activities that were thwarted by defense-in-depth protections. So, we again want to reiterate the value of industry best practices such as outlined here, and implementing Privileged Access Workstations (PAW) as part of a strategy to protect privileged accounts.
A zero trust, “assume breach” philosophy is an important approach to defense. Many of the techniques we’ve observed are post-compromise techniques, so security companies and Microsoft are looking for ways to improve detections and provide protection even when an attacker gains unauthorized access.
READ MORE HERE