Microsoft Zero Trust deployment guide for your applications
Introduction
More likely than not, your organization is in the middle of a digital transformation characterized by increased adoption of cloud apps and increased demand for mobility. In the age of remote work, users expect to be able to connect to any resource, on any device, from anywhere in the world. IT admins, in turn, are expected to securely enable their users’ productivity, often without changing the infrastructure of their existing solutions. For many organizations, with resources spread across multiple clouds, as well as on-prem, this means supporting complex hybrid deployments.
In this guide, we will focus on how to deploy and configure Microsoft Cloud App Security to apply Zero Trust principles across the app ecosystem, regardless of where those apps reside. Deploying Cloud App Security can save customers significant time, resources, and of course, improve their security posture. We will simplify this deployment, focusing on a few simple steps to get started, and then stepping through more advanced monitoring and controls. Specifically, we’ll walk through the discovery of Shadow IT, ensuring appropriate in-app permissions are enforced, gating access based on real-time analytics, monitoring for abnormal behavior based on real-time UEBA, controlling user interactions with data, and assessing the cloud security posture of an organization.
Getting started
Your Zero Trust journey for apps starts with understanding the app ecosystem your employees are using, locking down shadow IT, and managing user activities, data, and threats in the business-critical applications that your workforce leverages to be productive.
Discover and control the use of Shadow IT
The total number of apps accessed by employees in the average enterprise exceeds 1,500. That equates to more than 80 GB of data uploaded monthly to various apps, less than 15% of which are managed by their IT department. And as remote work becomes a reality for most, it’s no longer enough to apply access policies to only your network appliance.
To get started discovering and assessing cloud apps, set up Cloud Discovery in Microsoft Cloud App Security, and analyze your traffic logs against a rich cloud app catalog of over 16,000 cloud apps. Apps are ranked and scored based on more than 90 risk factors to help assess the risk Shadow IT poses to your organization.
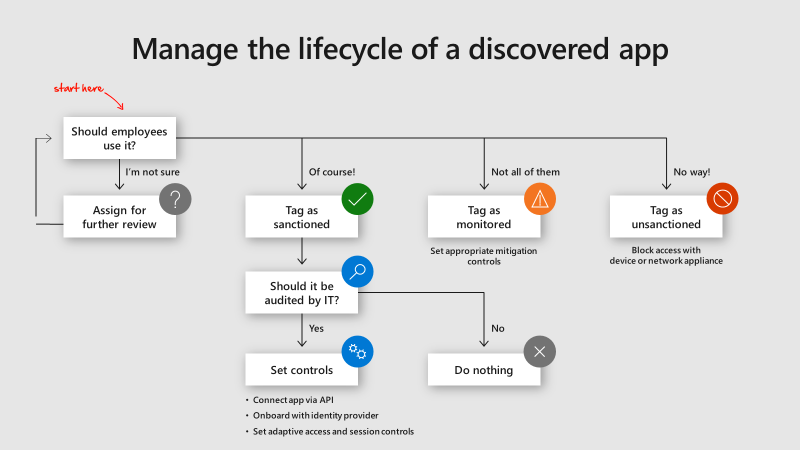
Once this risk is understood, each individual application can be evaluated, manually or via policy, to determine what action to take. The following decision tree shows potential actions that can be taken, based on whether the applications’ risk is deemed acceptable. Sanctioned applications can then be onboarded with your identity provider to enable centralized management and more granular control, while unsanctioned applications can be blocked by your network appliance or at the machine-level with one-click by leveraging Microsoft Defender ATP.
Monitor user activities and data
Once applications are discovered, one of the next steps for sanctioned apps is to connect them via API to gain deep visibility into those applications – after all, these are the apps where your most sensitive data resides. Microsoft Cloud App Security uses enterprise-grade cloud app APIs to provide instant visibility and governance for each cloud app being used.
Connect your business critical cloud applications, ranging from Office 365 to Salesforce, Box, AWS, GCP, and more, to Microsoft Cloud App Security to gain deep visibility into the actions, files, and accounts that your users touch day-in and day-out. Leverage these enterprise-grade API connections to enable the admin to perform governance actions, such as quarantining files or suspending users, as well as mitigate against any flagged risk.
Automate data protection and governance
For an organization that is constantly growing and evolving, the power of automation cannot be overstated. Once your apps are connected to Microsoft Cloud App Security, you can leverage versatile policies to detect risky behavior and violations, and automate actions to remediate those violations.
Microsoft Cloud App Security provides built-in policies for both risky activities and sensitive files, as well as the ability to create custom policies as needed, based on your own environment. For example, if a user forgets to label sensitive data appropriately before uploading it to the cloud, you can automate the application of the correct label by leveraging Microsoft Cloud App Security to scan the file, whether that app is hosted in a Microsoft or non-Microsoft cloud. In addition, more likely than not, guests or partner users are collaborating with you in your sensitive applications. You can set automatic actions to expire a shared link or removing external users while informing the file owner.
Protect against cyber threats and rogue apps
Connecting your apps enables you to automate data and access governance, but it also enables detecting and remediating against cyberthreats and rogue apps. Attackers closely monitor where sensitive information is most likely to end up and develop dedicated and unique attack tools, techniques, and procedures, such as illicit OAuth consent grants and cloud ransomware.
Microsoft Cloud App Security provides rich behavioral analytics and anomaly detections to help organizations securely adopt the cloud by providing malware protection, OAuth app protection, and comprehensive incident investigation and remediation. Because these are already enabled, you do not need to configure them. However, we recommend logging into your Cloud App Security portal to fine-tune them based on your environment (Click on Control, then Policies and select Anomaly detection policy).
Cloud App Security’s user and entity behavioral analytics (UEBA) and machine learning (ML) capabilities are enabled out-of-the-box so that you can immediately detect threats and run advanced threat detection across your cloud environment. Because they’re automatically enabled, new anomaly detection policies provide immediate results by providing immediate detections, targeting numerous security use cases such as impossible travel, suspicious inbox rules and ransomware across your users and the machines and devices connected to your network. In addition, the policies expose more data from the Cloud App Security detection engine and can be refined to help you speed up the investigation process and contain ongoing threats.
Configuring Advanced Controls
You’ve now assessed your cloud environment, unsanctioned dangerous and risky applications, and added automation to protect your sensitive corporate resources in your business-critical applications. Getting advanced means extending those security controls by deploying adaptive access controls that match the risk of each individual session and assessing and patching the security posture of your multi-cloud environments.
Deploy adaptive access and session controls for all apps
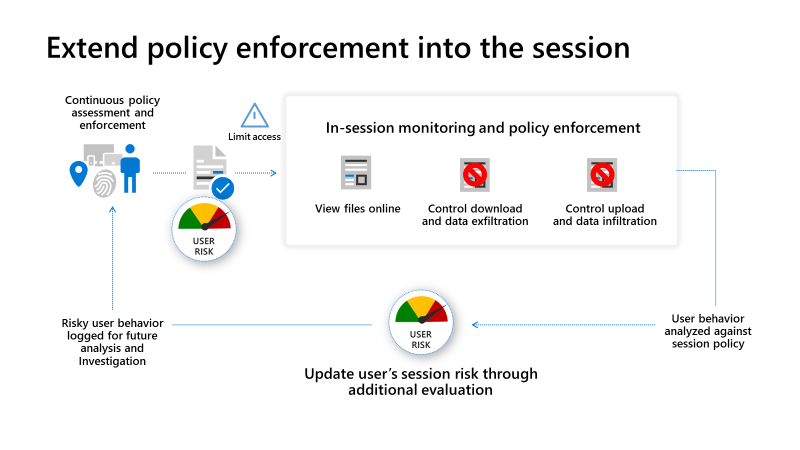
In today’s modern and dynamic workplace, it’s not enough to know what’s happening in your cloud environment after the fact. Stopping breaches and leaks in real-time before employees intentionally or inadvertently put data and organizations at risk is key. Simultaneously, it’s business-critical to enable users to securely use their own devices productively.
Enable real-time monitoring and control over access to any of your apps with Microsoft Cloud App Security access and session policies, including cloud and on-prem apps and resources hosted by the Azure AD App Proxy. For example, you can create policies to protect the download of sensitive content when using any unmanaged device. Alternatively, files can be scanned on upload to detect potential malware and block them from entering sensitive cloud environments.
Assess the security posture of your cloud environments
Beyond SaaS applications, organizations are heavily investing in IaaS and PaaS services. Microsoft Cloud App Security goes beyond SaaS security to enable organizations to assess and strengthen their security posture and Zero Trust capabilities for major clouds, such as Azure, Amazon Web Services, and Google Cloud Platform. These assessments focus on detailing the security configuration and compliance status across each cloud platform. In turn, you can limit the risk of a security breach, by keeping the cloud platforms compliant with your organizational configuration policy and regulatory compliance, following the CIS benchmark, or the vendor’s best practices for a secure configuration.
Microsoft Cloud App Security’s cloud platform security provides tenant-level visibility into all your Azure subscriptions, AWS accounts, and GCP projects. Getting an overview of the security configuration posture of your multi-cloud platform from a single location enables a comprehensive risk-based investigation across all your resources. The security configuration dashboard can then be used to drive remediation actions and minimize risk across all your cloud environments. View the security configuration assessments for Azure, AWS, and GCP recommendations in Cloud App Security to investigate and remediate against any gaps.
More Zero Trust deployment guides to come
We hope this blog helps you deploy and successfully incorporate apps into your Zero Trust strategy. Make sure to check out the other deployment guides in the series by following the Microsoft Security blog to keep up with our expert coverage on security matters. For more information on Microsoft Security Solutions visit our website. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE