Zabbix vulnerabilities added to CISA catalog
Two Zabbix vulnerabilities have been added to the US Cybersecurity Infrastructure and Security Agency’s catalog of known exploited vulnerabilities.
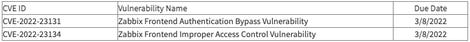
Federal civilian agencies have until March 8 to patch CVE-2022-23131 and CVE-2022-23134 — a Zabbix Frontend authentication bypass vulnerability and a Zabbix Frontend improper access control vulnerability. Zabbix is a popular open-source monitoring platform.
Patches for the issues were released in December. Zabbix explained that in the case of instances “where the SAML SSO authentication is enabled (non-default), session data can be modified by a malicious actor, because a user login stored in the session was not verified.”
“Malicious unauthenticated actor may exploit this issue to escalate privileges and gain admin access to Zabbix Frontend. To perform the attack, SAML authentication is required to be enabled and the actor has to know the username of Zabbix user (or use the guest account, which is disabled by default),” Zabbix said.
“To remediate this vulnerability, apply the updates listed in the ‘Fixed Version’ section to appropriate products or if an immediate update is not possible, follow the presented below workarounds.”
Zabbix credited SonarSource’s Thomas Chauchefoin for discovering and reporting the issue. SonarSource released its own blog on the vulnerabilities where Chauchefoin goes into detail about the intricacies of the issue. He discovered it in November and noted that the initial patch proposed by Zabbix was able to be bypassed.
BluBracket’s Casey Bisson explained that Zabbix is broadly used by businesses of all sizes to monitor servers and network equipment everywhere from data centers to branch offices.
“A vulnerability that allows attackers past the authentication controls could give those attackers access to extensive details about the infrastructure,” Bisson said.
“The details in Zabbix could reveal a map of sensitive company networks and equipment deep in company networks, including potentially vulnerable versions of software on that equipment. That information might be used to target further electronic attacks, social engineering, and spear phishing.”
Vulcan Cyber’s Mike Parkin added that Zabbix has a user base distributed worldwide, with a large portion of them in Europe, and spread across a range of verticals.
Both the National Cyber Security Center of the Netherlands and the Ukrainian Computer Emergency Response Team released notices about the issue in recent days. The Ukrainian notice says CVE-2022-23131 has a severity level of 9.1.
Parkin noted that the attack surface is reduced because the target has to be in a non-default configuration, and the attacker needs to know a valid username.
“Zabbix has included a workaround – disabling SAML authentication – and patches have been released, so it should be straightforward for affected organizations to mitigate this issue,” Parkin said.
READ MORE HERE
