This Week in Security News: XORDDoS and Kaiji Botnet Malware Variants Target Exposed Docker Servers and Ripple20 Vulnerabilities Could Impact Millions of IoT Devices

Welcome to our weekly roundup, where we share what you need to know about the cybersecurity news and events that happened over the past few days. This week, learn about two recently detected variants of existing Linux botnet malware types targeting exposed Docker servers. Also, read about a group of vulnerabilities dubbed Ripple20 that have the potential to critically impact millions of IoT devices across many different industries.
Read on:
The Fear of Vendor Lock-in Leads to Cloud Failures
Vendor lock-in, the fear that by investing too much with one vendor an organization reduces their options in the future, has been an often-quoted risk since the mid-1990s. Organizations continue to walk a fine line with their technology vendors. Ideally, you select a set of technologies that not only meet your current needs but that align with your future vision as well.
How Do I Select a Mobile Security Solution for My Business?
The percentage of companies admitting to suffering a mobile-related compromise has grown, despite a higher percentage of organizations deciding not to sacrifice the security of mobile devices to meet business targets. To make things worse, the C-suite is the most likely group within an organization to ask for relaxed mobile security protocols – despite also being highly targeted by cyberattacks.
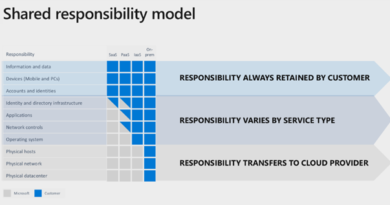
Knowing Your Shared Security Responsibility in Microsoft Azure and Avoiding Misconfigurations
Trend Micro is excited to launch new Trend Micro Cloud One™ – Conformity capabilities that will strengthen protection for Azure resources. As with any launch, there is a lot of new information, so we held a Q&A with one of the founders of Conformity, Mike Rahmati. In the interview, Mike shares how these new capabilities can help customers prevent or easily remediate misconfigurations on Azure.
FBI Warns K-12 Schools of Ransomware Attacks via RDP
The US Federal Bureau of Investigation (FBI) this week sent out a security alert to K-12 schools about the increase in ransomware attacks during the coronavirus pandemic, and especially about ransomware gangs that abuse RDP connections to break into school systems.
XORDDoS, Kaiji Botnet Malware Variants Target Exposed Docker Servers
Trend Micro recently detected variants of two existing Linux botnet malware types targeting exposed Docker servers: XORDDoS malware and Kaiji DDoS malware. Having Docker servers as their target is a new development for both XORDDoS and Kaiji; XORDDoS was known for targeting Linux hosts on cloud systems, while recently discovered Kaiji was first reported to affect internet of things (IoT) devices.
Frost & Sullivan Employee, Customer Data for Sale on Dark Web
A group is hawking records of more than 12,000 Frost & Sullivan employees and customers on a hacker folder. According to Cyble CEO Beenu Arora the breach was a result of a misconfigured backup directory on one of Frost & Sullivan’s public-facing servers. The KelvinSecurity Team said they put the information – which includes names, email addresses, company contacts, login names and hashed passwords – for sale in a hacking forum to sound the “alarm” after Frost & Sullivan didn’t respond to the group’s attempt to alert it to the exposed database.
Millions of IoT Devices Affected by Ripple20 Vulnerabilities
Israeli cybersecurity firm JSOF has released information on a group of vulnerabilities dubbed Ripple20. These vulnerabilities have the potential to critically impact millions of internet of things (IoT) devices across many different industries — crucial machines in the medical, oil and gas, transportation, power, and manufacturing industries can be affected by these bugs.
Nvidia Warns Windows Gamers of Serious Graphics Driver Bugs
Graphics chipmaker Nvidia has fixed two high-severity flaws in its graphics drivers. Attackers can exploit the vulnerabilities to view sensitive data, gain escalated privileges or launch denial-of-service (DoS) attacks in impacted Windows gaming devices.
Cyberattacks from the Frontlines: Incident Response Playbook for Beginners
For enterprises, staying competitive in an ever-changing market involves keeping up with the latest technological trends. However, without the parallel development of security infrastructure and robust response, new technology could be used as a conduit for cyberthreats that result in losses. Organizations should aim to prevent these breaches from happening — but having protocols for reducing a breach lifecycle is an essential and realistic approach for dealing with current threats.
OneClass Unsecured S3 Bucket Exposes PII on More than One Million Students, Instructors
An unsecured database belonging to remote learning platform OneClass has exposed information associated with more than a million students in North America who use the platform to access study guides and educational assistance. Data exposed includes full names, email addresses (some masked), schools and universities attended, phone numbers, school and university course enrollment details and OneClass account details.
During the past decade, various countries and industries have actively developed guidelines and frameworks for OT security. Recently, multiple guidelines have been integrated, and two standards as global standards are IEC62443 and the NIST CSF, SP800 series, from the viewpoint of security in smart factories. In this series, Trend Miro explains the overviews of IEC62443 and NIST CSF, in order to understand their concepts required for security in smart factories.
Many businesses have misperceptions about cloud environments, providers, and how to secure it all. In order to help separate fact from fiction when it comes to your cloud environment, Trend Micro debunks 8 myths to help you confidently take the next steps in the cloud.
Does your organization have an incident response playbook for potential breaches? Share your thoughts in the comments below or follow me on Twitter to continue the conversation: @JonLClay.
Read More HERE