This Week in Security News June 4, 2021 Director, Global Threat Communications


Welcome to our weekly roundup, where we share what you need to know about cybersecurity news and events that happened over the past few days. This week, read about how the world’s largest meatpacker, JBS, was the target of an organized cybersecurity attack. Also, learn how a DarkSide ransomware variant is targeting virtual machine-related files on VMware ESXI servers.
Read on:
Where Bug Bounty Programs Fall Flat
Cybercriminal forums shows that cybercriminals have specific preferences, shown by the exploits they requisition, and that bug bounty programs either are too slow, don’t pay enough, or are just the start of profit-making. In this Threatpost podcast episode, Mayra Fuentes, senior threat researcher at Trend Micro, discusses the people who are buying and selling exploits in the underground and why.
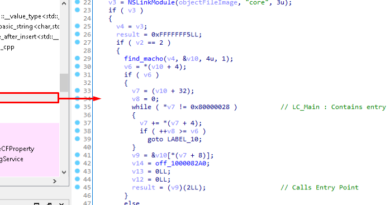
DarkSide on Linux: Virtual Machines Targeted
The DarkSide ransomware group is targeting organizations in manufacturing, finance, and critical infrastructures in regions such as the U.S., France, Belgium and Canada. In this blog, Trend Micro discusses how DarkSide targets virtual machine-related files on VMware ESXI servers, parses its embedded configuration, kills virtual machines (VMs), encrypts files on the infected machine, collects system information, and sends it to the remote server.
New security segment XDR combines elements of SIEM; security orchestration, automation, and response (SOAR); endpoint detection and response (EDR); and network traffic analysis (NTA) in a cloud-based platform. This centralizes security data, threat hunting, and incident response. In this article, learn how analysts predict that XDR and SIEM are colliding.
Manage Open-Source Code Security Risks
The adoption of open-source code has increased exponentially over the past decade, with a large percentage of commercial software now using it. Developers are constantly sharing common features and code functionality across the internet and globe. In this blog, learn best practices to mitigate the unique risks that accompany its use.
Cyberattack hits JBS meat works in Australia, North America
On May 30, the world’s largest meatpacker, JBS USA, reported that it was the target of an organized cybersecurity attack, affecting some of the servers supporting its North American and Australian IT systems. The attack shut down operations across several Australian states, delaying certain transactions with customers and suppliers.
Latest Report Identifies Foundational Threats to the 5G Infrastructure
A new paper from the Cybersecurity Infrastructure Agency (CISA), National Security Agency, and the Office of the Director of National Intelligence has found three major potential threat vectors to 5G infrastructure: policy and standards, supply chain, and 5G systems architecture. There are two sub-threat vectors on the policies and standards category: open standards and optional controls. Learn more about the new report in this blog.
Russian underground forums launch competitions for cryptocurrency, NFT hacks
Over the past month, operators of Russian underground forums have been running a competition asking for papers that examine “how to target cryptocurrency-related technology.” The contest requests unorthodox methods from the theft of private keys and wallets used to store cryptocurrency including Bitcoin and Ethereum, to submissions for “unusual” cryptocurrency mining software and proposals relating to smart contracts and non-fungible tokens (NFTs).
Proven Leadership in Multi-Layered Threat Defense
The rapidly evolving threat landscape requires partnership with a trusted cybersecurity expert that can provide protection across distributed endpoints, networks, cloud infrastructure and hybrid environments. Independent research plays a vital role for the cybersecurity buyer and that’s why Trend Micro is delighted to have maintained its leadership position across multiple cybersecurity environments—according to some of the world’s most respected authorities.
Malware Can Use This Trick to Bypass Ransomware Defense in Antivirus Solutions
Researchers have disclosed significant security weaknesses in popular software applications that could be abused to deactivate their protections. Twin attacks aim at circumventing the protected folder feature offered by antivirus programs to encrypt files and disable their real-time protection by simulating mouse “click” events.
Trend Micro researchers discovered a vulnerability in macOS rooted in the Core Virtual Machine Server (CVMServer). The vulnerability, labeled CVE-2021-30724, is triggered by an integer overflow leading to an out-of-bounds memory access, from which point privilege escalation can be attained. It affects devices running older versions of macOS Big Sur 11.4, iOS 14.6, and iPadOS 14.6.
What are your thoughts on the JBS attack? Share in the comments below or follow me on Twitter to continue the conversation: @JonLClay.
Read More HERE