Telcos to get expanded scam-blocking powers through telecommunications law amendment
The federal government has announced it will amend telecommunications legislation to provide telcos with the ability to block scam SMS messages.
“The regulatory amendment we have enacted provides the telecommunications sector with the authority they need to block malicious SMS messages at scale and protect the Australian public from scammers,” Minister for Home Affairs Karen Andrews said.
“The Morrison government is committed to collaborating with industry to tackle new and emerging threats to the Australian community, including scams that exploit digital technologies for nefarious ends.”
The changes entail amending the Telecommunications (Interception and Access) Act 1979 (TIA Act) so that telcos can intercept malicious SMS messages to be able to block them.
The regulatory amendments have been in development for some time, with Home Affairs secretary Mike Pezzullo telling Senate Estimates that his department had been in talks with the telecommunications industry to provide more powers to telcos for blocking spam and malicious content through the TIA Act.
Telstra CEO Andy Penn said in light of the regulatory changes, his telco was now developing a new cyber safety capability designed to automatically detect and block scam SMS messages as they travel across its network.
The capability is currently being run as a pilot inside Telstra so that any scam SMS messages sent to its staff can help “train” the systems to spot the difference between a legitimate and a malicious SMS. This latest capability is part of Telstra’s Cleaner Pipes initiative that commenced last year.
Andrews also announced that a new Joint Policing Cybercrime Coordination Centre — the JPC3 — will be operational from March 2022, which will specifically focus on preventing cyber criminals from scamming, stealing, and defrauding Australians.
The JPC3’s operations will be led by Australian Federal Police (AFP) assistant commissioner Justine Gough, who will become the AFP’s first full-time executive dedicated to countering cyber crime.
“AFP-led JPC3 will target at scale those cyber criminals who trick firms using business email compromise or unleash mass phishing attacks, which can scam individuals out of personal information or money,” the AFP said.
With Andrews announcing these new cyber initiatives, the AFP simultaneously said it has prevented cyber criminals from stealing AU$24 million from local superannuation accounts through a newly unveiled operation.
Under Operation Zinger, the AFP said it shut down a criminal marketplace dealing in the online sale of cybercrime software, which contained over 500,000 compromised online credentials.
By examining 500 gigabytes of data, the AFP was able to determine victims and offenders. The AFP then proceeded to contact 20 superannuation companies and facilitated the remediation of more than 25 managed super information systems to protect 681 matched super accounts attached to members and 35 matched super accounts attached to employers.
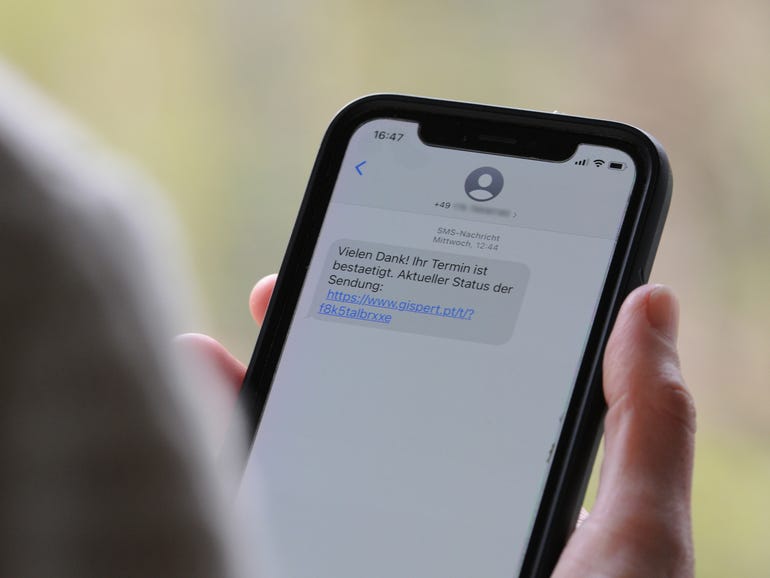
The AFP has also charged a Sydney man for stealing more than AU$100,000 in an illegal SMS phishing scam that targeted the banks and telecommunications accounts of more than 450 victims. The phishing scam entailed luring victims onto a phony webpage, via SMS, and asking them to provide personal information. The charged individual then used this information to access victims’ telephone and bank accounts. He also created new accounts without their knowledge.
The AFP worked with Commonwealth Bank of Australia, National Australia Bank, and Telstra to identify victims who had entered information into these phony webpages. The companies also placed additional security protocols on those account holders, helping prevent more than AU$4 million from being stolen from the accounts of another 16,000 Australians, the AFP said.
The charged individual, if found guilty, could face up to 26 years of imprisonment.
All of the new measures follow the theme of countering cyber threats, much like other initiatives announced by Home Affairs in recent months such as the Critical Infrastructure Bill that is currently waiting for Royal Assent, its national ransomware action plan, and new principles for critical technology supply chain security.
RELATED COVERAGE
READ MORE HERE
