Trend Micro Research : Research
Latest Batloader Campaigns Use Pyarmor Pro for Evasion
In June 2023, Trend Micro observed an upgrade to the evasion techniques used by the Batloader initial access malware, which we’ve covered in previous blog entries. Read More HERE…
Related CherryBlos and FakeTrade Android Malware Involved in Scam Campaigns
Trend Micro’s Mobile Application Reputation Service (MARS) team discovered two new related Android malware families involved in cryptocurrency-mining and financially-motivated scam campaigns targeting Android users. Read More HERE…
Supply-Chain Attack Targeting Pakistani Government Delivers Shadowpad
We recently found that an MSI installer built by the National Information Technology Board (NITB), a Pakistani government entity, delivered a Shadowpad sample, suggesting a possible supply-chain attack. Read More HERE…
Possible Supply-Chain Attack Targeting Pakistani Government Delivers Shadowpad
We recently found that a modified installer of the E-Office app used by the Pakistani government delivered a Shadowpad sample, suggesting a possible supply-chain attack. Read More HERE…
Hunting for A New Stealthy Universal Rootkit Loader
In this entry, we discuss the findings of our investigation into a piece of a signed rootkit, whose main binary functions as a universal loader that enables attackers to directly load a second-stage unsigned kernel module. Read More HERE…
Malvertising Used as Entry Vector for BlackCat, Actors Also Leverage SpyBoy Terminator
We found that malicious actors used malvertising to distribute malware via cloned webpages of legitimate organizations. The distribution involved a webpage of the well-known application WinSCP, an open-source Windows application for file transfer. We were able to identify that this activity led to a BlackCat (aka ALPHV) infection, and actors also used SpyBoy, a terminator that tampers with protection provided by agents. Read More HERE…
An Overview of the Different Versions of the Trigona Ransomware
The Trigona ransomware is a relatively new ransomware family that began activities around late October 2022 — although samples of it existed as early as June 2022. Since then, Trigona’s operators have remained highly active, and in fact have been continuously updating their ransomware binaries. Read More HERE…
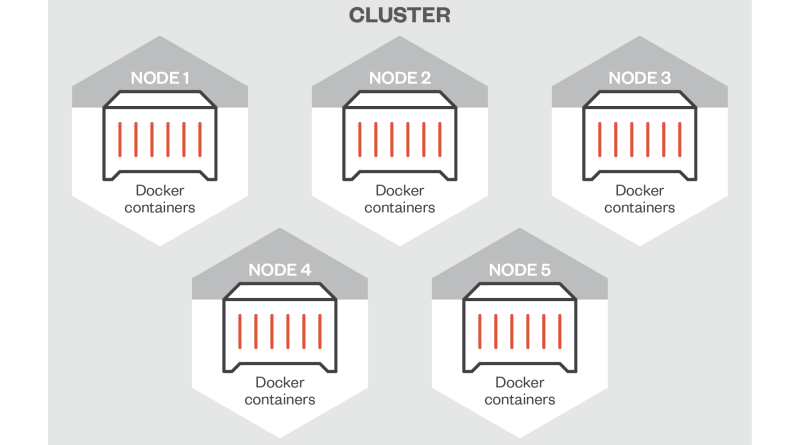
Gaps in Azure Service Fabric’s Security Call for User Vigilance
In this blog post, we discuss different configuration scenarios that may lead to security issues with Azure Service Fabric, a distributed platform for deploying, managing, and scaling microservices and container applications. Read More HERE…
Behind the Scenes: Unveiling the Hidden Workings of Earth Preta
This blog entry discusses the more technical details on the most recent tools, techniques, and procedures (TTPs) leveraged by the Earth Preta APT group, and tackles how we were able to correlate different indicators connected to this threat actor. Read More HERE…