Trend Micro Research : Cloud
A Better Way to Secure Servers & Cloud Workloads
Why endpoint security falls short in the complexity of modern IT infrastructure Read More HERE…
Trend Vision One™ – A Cybersecurity Consolidation Path
A single-platform approach delivers value greater than the sum of its parts Read More HERE…
Platform Approach to Cybersecurity: The New Paradigm
Embracing platform approach as the path to enhanced security and resilience Read More HERE…
Tailing Big Head Ransomware’s Variants, Tactics, and Impact
We analyze the technical details of a new ransomware family named Big Head. In this entry, we discuss the Big Head ransomware’s similarities and distinct markers that add more technical details to initial reports on the ransomware. Read More HERE…
Four Must-haves to Strengthen Your Endpoint Security
To combat complexity and achieve optimal security outcomes, there are four key factors an organization should consider when evaluating their endpoint security. Read More HERE…
How to Deploy Generative AI Safely and Responsibly
New uses for generative AI are being introduced every day—but so are new risks. Read More HERE…
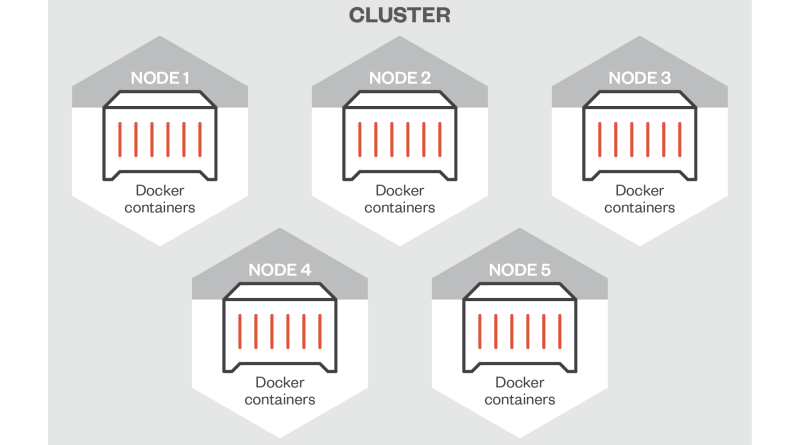
Gaps in Azure Service Fabric’s Security Call for User Vigilance
In this blog post, we discuss different configuration scenarios that may lead to security issues with Azure Service Fabric, a distributed platform for deploying, managing, and scaling microservices and container applications. Read More HERE…
Generative AI Assistant Makes Hunting Threats Faster
Learn how analysts can search for threats with greater accuracy, speed, and effectiveness. Read More HERE…