Microsoft delivers comprehensive solution to battle rise in consent phishing emails
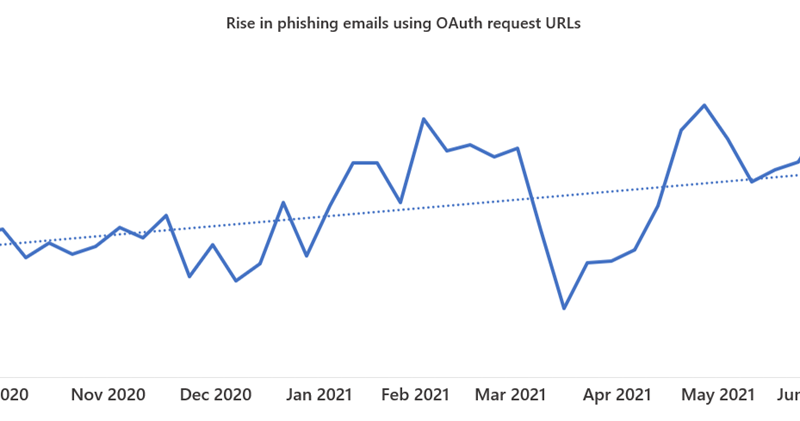
Microsoft threat analysts are tracking a continued increase in consent phishing emails, also called illicit consent grants, that abuse OAuth request links in an attempt to trick recipients into granting attacker-owned apps permissions to access sensitive data.
The post Microsoft delivers comprehensive solution to battle rise in consent phishing emails appeared first on Microsoft Security Blog. READ MORE HERE…