3 steps to secure your multicloud and hybrid infrastructure with Azure Arc
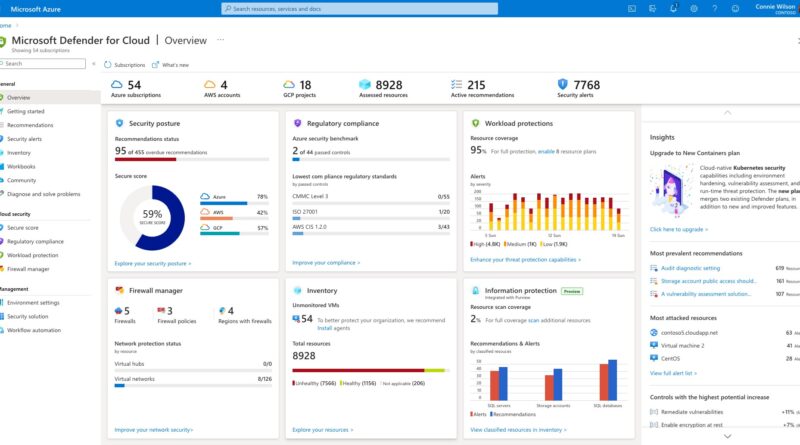
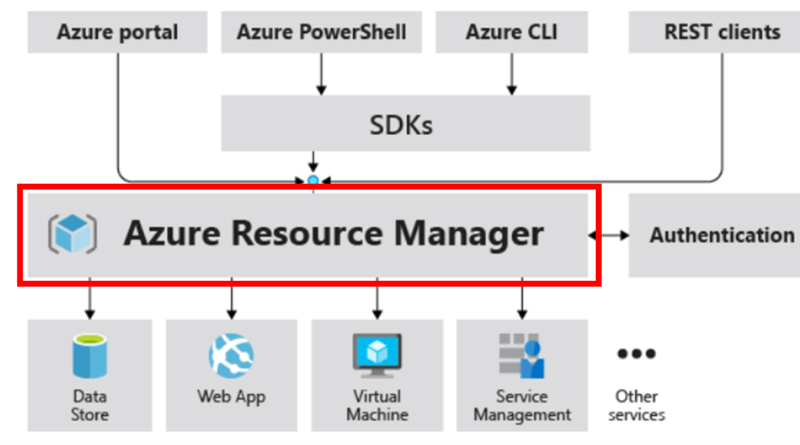
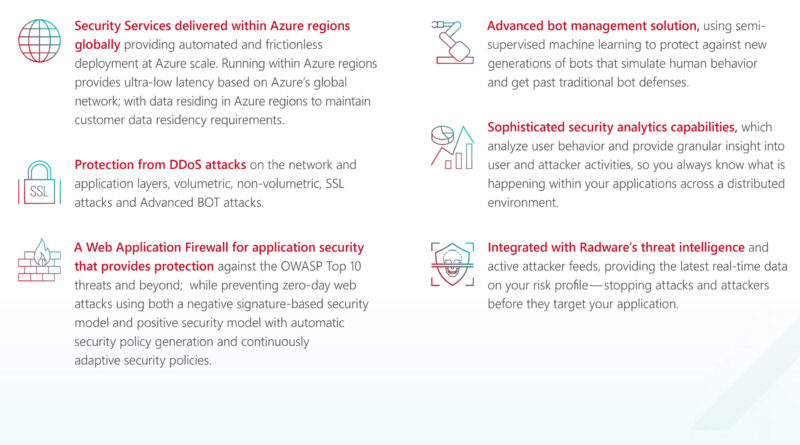
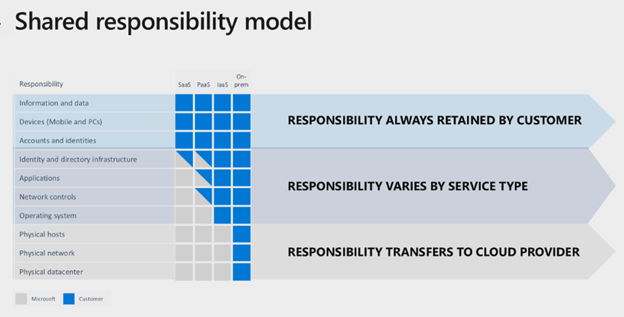
In this blog, we will share how you can increase security for on-premises and hybrid infrastructure through offerings including Azure Arc, Microsoft Defender for Cloud, and Secured-core for Azure Stack HCI.
The post 3 steps to secure your multicloud and hybrid infrastructure with Azure Arc appeared first on Microsoft Security Blog. READ MORE HERE…