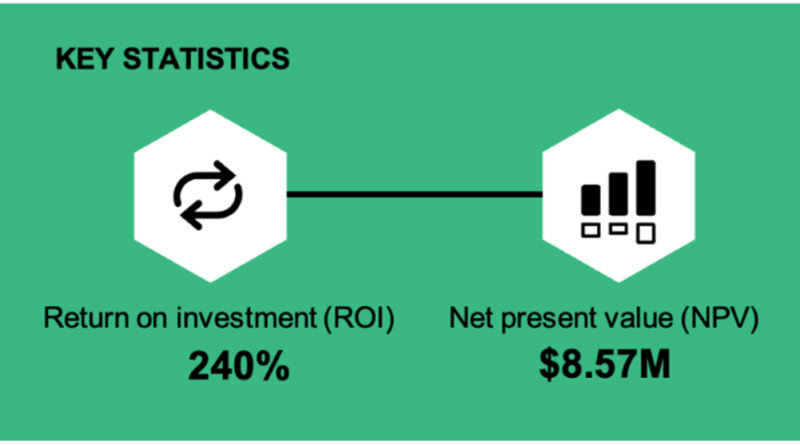
Microsoft Entra delivers 240 percent ROI, according to new Forrester study
Learn why Microsoft Entra delivers 240-percent ROI—get key benefits and real-world learnings from adopters across the financial, high-tech, and manufacturing sectors.
The post Microsoft Entra delivers 240 percent ROI, according to new Forrester study appeared first on Microsoft Security Blog. READ MORE HERE…