Stalking the Stalkerware

Ever get the feeling you’re being followed? Unfortunately, when it comes to our digital lives, this is increasingly the case. But while we’re all keen to boost our followers on social media, it’s a different matter when it comes to anonymous third parties secretly stalking us online. Yes, we’re already tracked by ISPs every time we go online, or by web providers like Google and social sites like Facebook and Twitter. But in these cases, we do get a little back in return: more streamlined, personalized services, and at the least, more relevant (if annoying) advertising. In the best scenario, though, we’d never be tracked without our consent.
With a phenomenon known as stalkerware, however, there’s zero gain for the victim. This is nothing short of government-style surveillance software used by individuals to spy on others – usually someone you know.
What is stalkerware?
We’re all spending more time on our smartphones. For the first time ever this year, time spent on mobile devices exceeded that spent in front of the TV. By 2021, it’s predicted that Americans will be glued to their handsets for nearly four hours per day. We chat and flirt with friends on social media. We post our photos and status updates. We email, text, IM and call via our devices. We also shop, hail taxis, or navigate around town, listen to music or watch YouTube or TV, and even bank online – all from the mini-computer in the palm of our hands.
Unfortunately, for some of us, there are people out there that want to know what we’re doing and who we’re with at all times. It could be a jealous partner, a jilted ex, over-protective parents, or even a suspicious employer. For them, a whole mini-industry has appeared over the past couple of years selling monitoring software, or more treacherously, trojan spyware and code that can hide itself, so you don’t even know it’s on your device. For just a few dollars, individuals can get their hands on an app which can monitor everything you do on your device. This includes
|
|
Breaking the law
Let’s be clear: it’s when monitoring software—and certainly, spyware—is used for stalking that it really becomes stalkerware. That means firms selling monitoring software may be operating in a grey area ethically and legally, depending on how the software is used. While they’re technically legitimate, the surveillance software is usually branded in such a way as to keep them just this side of the law. Think of concerned parents who want to ensure their children are safe, or of employers who want to ensure their staff are where they should be during work hours. That said, those who use such software to spy on individuals without their knowledge or consent are violating ethical standards and breaking the law. And if the software or code is specifically designed to hide itself, as with trojan spyware or spying code—then a line has certainly been crossed. You’re now neck deep in the shady gumshoe world of stalkerware.
There’s a huge range of “spyware” or “monitoring” apps available on the market today, including Retina-X, FlexiSpy, Mobistealth, Spy Master Pro, SpyHuman, Spyfone, TheTruthSpy, Family Orbit, mSpy, Copy9, Spyera, SpyBubble, and Android Spy. Given the often covert nature of the industry, it’s hard to get an accurate picture of exactly how widespread the use of such software for stalking is, although the number of titles on the market should give some indication. Reports from 2017 suggested 130,000 people had an account with Retina-X or FlexiSpy, while it was claimed a few years prior that mSpy had as many as two million users.
Stalkerware, or the use of monitoring software for stalking, represents not only a gross intrusion into your privacy, but also a possible security concern if the companies running these apps are themselves hacked or accidentally leak data belonging to victims of their customers.
How do I know if my phone has been hit?
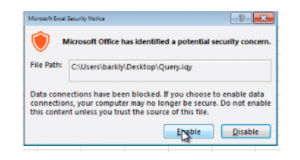
It can be quite difficult for users of stalkerware to install the spying app on your device without physical access to it. However, malicious links in emails, texts, on websites, or even on social media could represent a potential threat vector if attackers manage to trick you into clicking through to an unwanted install. Although iOS devices are difficult to tamper with unless they’re jailbroken—and jailbreaking itself is trickier than it used to be—Android users are more exposed.
While ‘legitimate’ GPS trackers and the like (such as Life360 and other monitoring apps) are available on Google Play and can be installed as visible apps, stalkerware is typically available on 3rd-party app stores, is installed without the user’s consent, and will do its best to stay hidden on your device, potentially disguising itself under different app or process names. So here are a few things you can do to spot the tell-tale signs something is not quite right:
|
|
How do I keep my device secure?
By its very nature, stalkerware is designed to stay hidden, so it can be hard to spot. But here are a few ideas to keep your device, and life, free from unwarranted snooping:
|
|
How Trend Micro can help
Trend Micro can help you fight against stalkerware on your Android device with Trend Micro Mobile Security. It can scan your device before, during, and after a download to detect for:
|
|
Depending on the type of stalkerware, it could fall into any of the above categories—but Trend Micro Mobile Security can help fight against all of them. Below are typical test examples of the protection processes it provides against Android malware, PUAs, and stalkerware.


Trend Micro also offers protection from PUAs on PCs and Macs via Trend Micro Security, to deal with the broader threat of stalkerware across multiple fixed as well as mobile platforms. Trend Micro Antivirus for Mac also provides protection against webcam hacks, which can be used for stalking.
Together, both solutions can help protect you—and your Windows and Mac desktops and Android mobile devices—against stalkerware.
Tags: Stalkerware, Antimalware, Antivirus, Endpoint Security, Mobile Security
Read More HERE