Spear phishing campaigns—they’re sharper than you think
Even your most security-savvy users may have difficulty identifying honed spear phishing campaigns. Unlike traditional phishing campaigns that are blasted to a large email list in hopes that just one person will bite, advanced spear phishing campaigns are highly targeted and personal. They are so targeted, in fact, that we sometimes refer to them as “laser” phishing. And because these attacks are so focused, even tech-savvy executives and other senior managers have been duped into handing over money and sensitive files by a well-targeted email. That’s how good they are.
Even though spear phishing campaigns can be highly effective, they aren’t foolproof. If you understand how they work, you can put measures in place to reduce their power. Today, we provide an overview of how these campaigns work and steps you can take to better protect your organization and users.
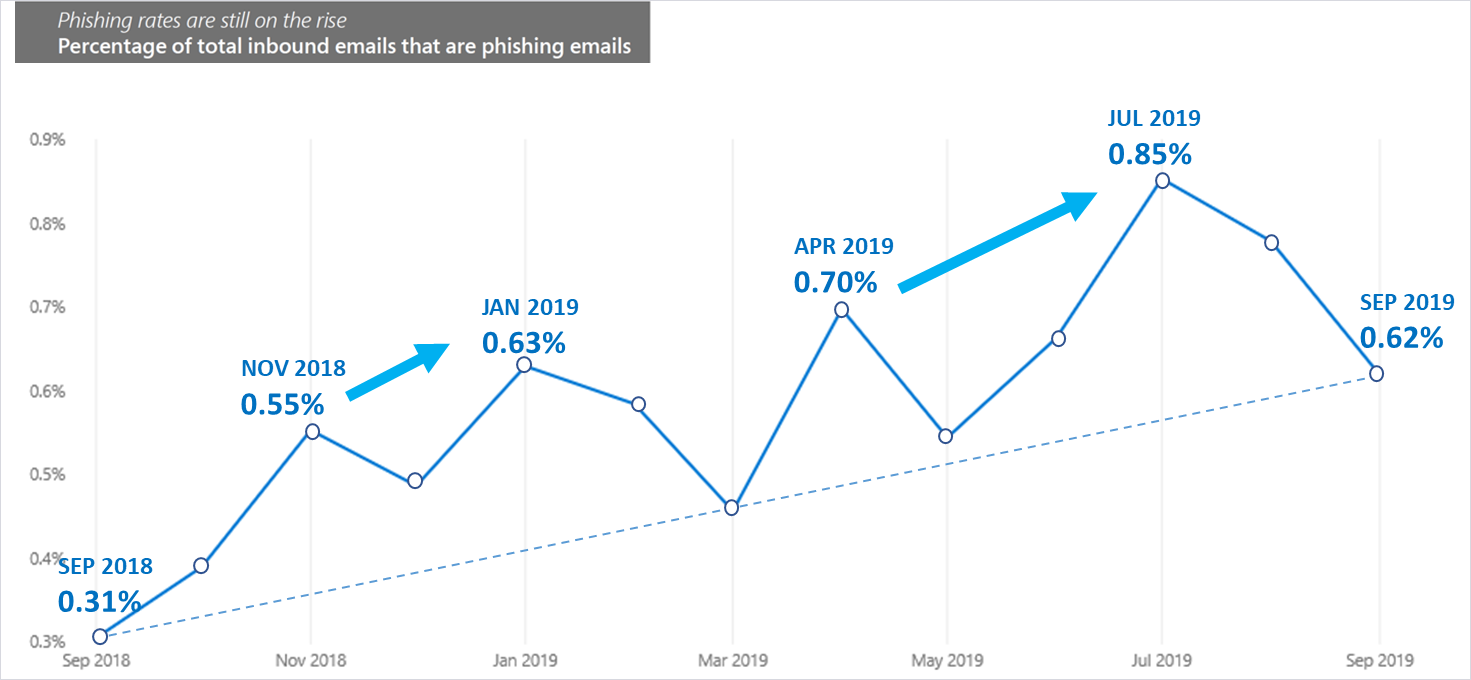
Figure 1. Percentage of inbound emails associated with phishing on average increased in the past year, according to Microsoft security research (source: Microsoft Security Intelligence Report).
Step 1: Select the victims
To illustrate how clever some of these campaigns are, imagine a busy recruiter who is responsible for filling several IT positions. The IT director is under a deadline and desperate for good candidates. The recruiter posts the open roles on their social networks asking people to refer leads. A few days later they receive an email from a prospective candidate who describes the role in the email. The recruiter opens the attached resume and inadvertently infects their computer with malware. They have just been duped by a spear phisher.
How did it happen?
In a spear phishing campaign, the first thing an attacker needs to do is identify the victims. These are typically individuals who have access to the data the attacker wants. In this instance, the attackers want to infiltrate the human resources department because they want to exfiltrate employee social security numbers. To identify potential candidates they conduct extensive research, such as:
- Review corporate websites to gain insight into processes, departments, and locations.
- Use scripts to harvest email addresses.
- Follow company social media accounts to understand company roles and the relationships between different people and departments.
In our example, the attackers learned by browsing the website that the convention for emails is first.last@company.com. They browsed the website, social media, and other digital sources for human resources professionals and potential hooks. It didn’t take long to notice several job openings. Once the recruiter shared details of jobs online, would-be attackers had everything they needed.
Why it might work: In this instance it would be logical for the victim to open the attachment. One of their job responsibilities is to collect resumes from people they don’t know.
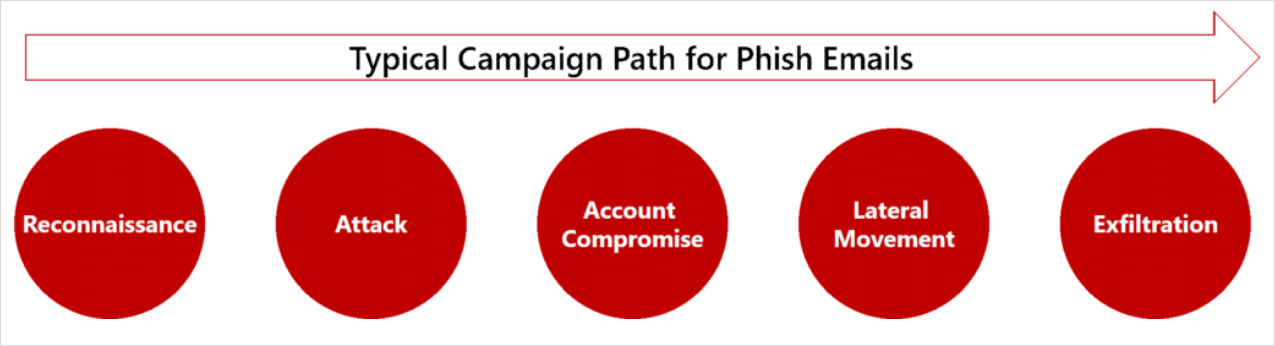
Figure 2. Research and the attack are the first steps in a longer strategy to exfiltrate sensitive data.
Step 2: Identify the credible source
Now let’s consider a new executive who receives an email late at night from their boss, the CEO. The CEO is on a trip to China meeting with a vendor, and in the email, the CEO references the city they’re in and requests that the executive immediately wire $10,000 to pay the vendor. The executive wants to impress the new boss, so they jump on the request right away.
How did it happen?
In spear phishing schemes, the attacker needs to identify a credible source whose emails the victim will open and act on. This could be someone who appears to be internal to the company, a friend, or someone from a partner organization. Research into the victim’s relationships informs this selection. In the first example, we imagined a would-be job seeker that the victim doesn’t know. However, in many spear phishing campaigns, such as with our executive, the credible source is someone the victim knows.
To execute the spear phishing campaign against the executive, the attackers uncovered the following information:
- Identified senior leaders at the company who have authority to sign off on large sums of money.
- Selected the CEO as the credible source who is most likely to ask for the money.
- Discovered details about the CEO’s upcoming trip based on social media posts.
Why it might work: Targeting executives by impersonating the CEO is increasingly common—some refer to it as whale phishing. Executives have more authority and access to information and resources than the average employee. People are inclined to respond quickly when the boss emails—especially if they say it’s urgent. This scenario takes advantage of those human power dynamics.
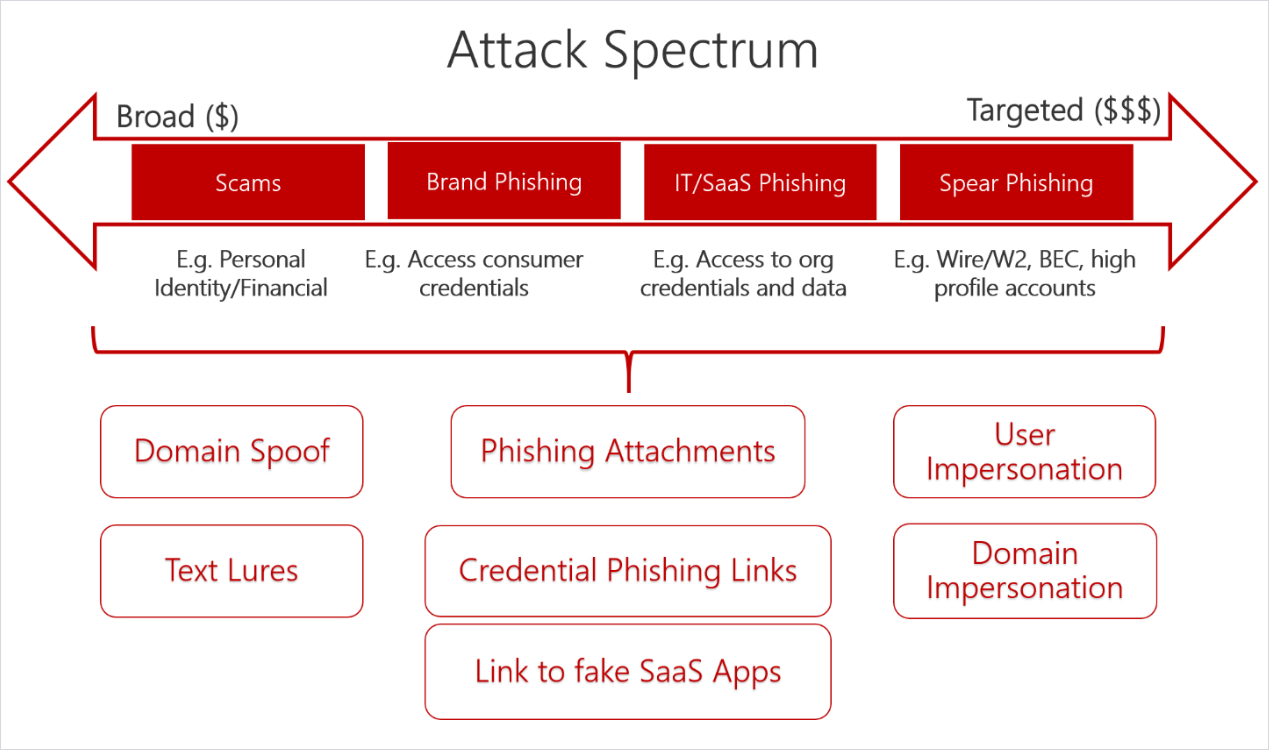
Figure 3. The more targeted the campaign, the bigger the potential payoff.
Step 3: Victim acts on the request
The final step in the process is for the victim to act on the request. In our first example, the human resources recruiter could have initiated a payload that would take over his computer or provide a tunnel for the attacker to access information. In our second scenario, the victim could have wired large sums of money to a fraudulent actor. If the victim does accidentally open the spear phishing email and respond to the call to action, open a malicious attachment, or visit an infected webpage, the following could happen:
- The machine could be infected with malware.
- Confidential information could be shared with an adversary.
- A fraudulent payment could be made to an adversary.
Catch more phishy emails
Attackers have improved their phishing campaigns to better target your users, but there are steps you can take to reduce the odds that employees will respond to the call to action. We recommend that you do the following:
- Educate users on how to detect phishing emails—Spear phishing emails do a great job of effectively impersonating a credible source; however, there are often small details that can give them away. Help users identify phish using training tools that simulate a real phish. Here are a few tells that are found in some phish that you can incorporate into your training:
- An incorrect email address or one that resembles what you expect but is slightly off.
- A sense of urgency coupled with a request to break company policy. For example, fast tracking payments without the usual checks and procedures.
- Emotive language to evoke sympathy or fear. For example, the impersonated CEO might say you’re letting them down if you do not make the urgent payment.
- Inconsistent wording or terminology. Does the business lingo align with company conventions? Does the source typically use those words?
- Encourage users to communicate potential phishing emails—It’s important that users flag phishing emails to the proper team. This can be done natively within many enterprise email systems. It can also be helpful if users talk with their peers about the phishing emails they receive. Spear phishers typically don’t send blast emails; however, they may select several people from the same department or with business relationships. Talking will alert other users to be on the lookout for phishy emails.
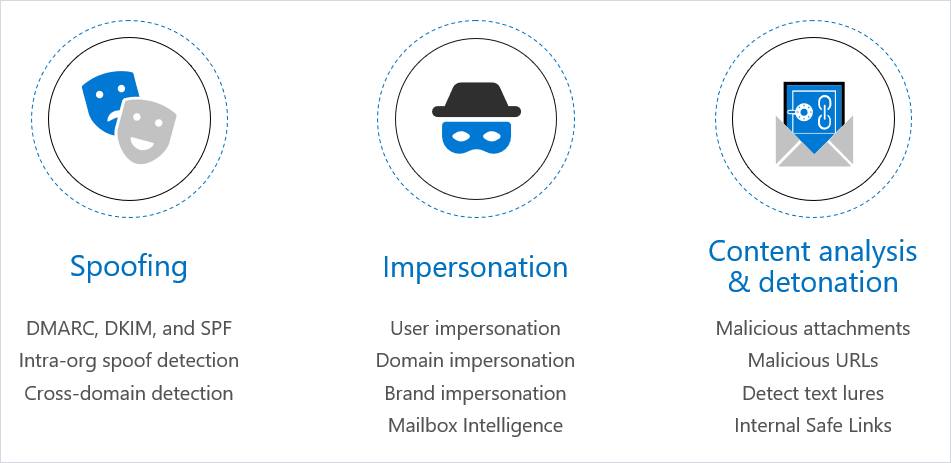
Figure 4. Enhanced anti-phishing capabilities are available in Microsoft Office 365.
- Deploy technology designed to block phishing emails—If users don’t receive the phishing email, they can’t act on it! Deploy technology that can help you catch phishing emails before they land in someone’s inbox. For instance, Office 365, one of the world’s largest email providers, offers a variety of protection against phishing attacks by default and through additional offerings such as Microsoft Advanced Threat Protection (ATP) anti-phishing. Importantly, Microsoft has both been advancing the anti-phishing capabilities of Office 365 (see Figure 4 above) and improving catch rates of phishing emails.
Get in touch
Reach out to Diana Kelley on LinkedIn or Twitter or Seema Kathuria on LinkedIn or Twitter and let them know what you’d like to see us cover as they talk about new security products and capabilities.
Also, bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE