Safeguarding against cryptomining attacks Threat Research Engineer Threat Research Engineer
Later, they gain an initial foothold into the Apache Amazon EC2 instance by exploiting a well-known vulnerability in the Apache Struts Framework (CVE-2017-5638) using a public proof of concept (POC), which enables them to execute commands on the compromised host remotely. They attempt to enumerate the running processes and current user, obtain the current working directory and view the /etc/passwd file. Then, they proceed to deploy a JSP webshell, for later persistence.
Through the deployed webshell, the attacker can:
- View environment variables
- Browse through the directories using a file manager
- Search for files on the compromised host
- Execute commands and get the output
- Connect to MySQL database (if there is any) on the compromised host or any other host
- Capture the desktop graphical user interface (GUI), if there is one.
To start, they list out the details of the instances in that region by performing the DescribeInstances API call using the AWS Command Line Interface (CLI). Later, they download a pre-compiled ELF file, and we see it scanning the subnet for the default ports for Apache Tomcat Manager, Redis, Apache CouchDB™, and Docker Engine API (a RESTful API). They discover another Drupal Amazon EC2 instance with port 80 open for public access.
Equipped with the relevant information, the attackers fetch the AWS Identity and Access Management (IAM) role credentials associated with the Apache Amazon EC2 instance by querying the AWS IMDS and try enumerating the permissions in a very intrusive and noisy manner, which we confirmed from the unusual AWS CloudTrail logs.
On the compromised instance itself, they immediately enumerate and download the contents of the Amazon S3 buckets.
On the newly discovered host, they execute a brute force attack on the SSH and later, they identify that this instance is running Drupal CMS 8.4.2 in the default configuration on the HTTP port 80. They successfully exploit CVE-2018-7600 and launch a remote code execution attack using a public POC. Next, the attackers upload a hypertext preprocessor (PHP) backdoor into the web root.
Using this backdoor, the attackers download the Apache Struts™ Exploit into the world-writable directory (/tmp) and attempt reading the Unix shadow file by exploiting the Struts vulnerability (CVE-2017-5638) on the same machine they gained initial access from. Upon the unsuccessful attempt, they move to deploying the XMRig coinminer on both the machines.
Lastly, to cover their tracks, the attacker shuts down the Amazon EC2 instances.
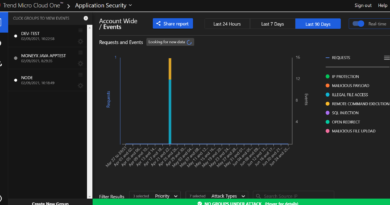
Trend Micro Cloud One Correlations
Trend Micro Cloud One is a platform comprised of 7 security solutions purpose-built for cloud builders. For the first set of detections, we used Trend Micro Cloud One™ – Workload Security, which provides automated security via powerful APIs. Workload Security uses advanced security controls such as intrusion prevention system (IPS), deep packet inspection (DPI), and integrity monitoring to protect against coinminer attacks. The following detection rules safeguard the vulnerable instances against the reported CVEs:
Workload Security
IPS detections:
- 1005934 – Identified Suspicious Command Injection Attack
- 1006823 – Identified Suspicious Command Injection Attack – 1
- 1005604 – Apache Struts Multiple Remote Command Execution Vulnerability
- 1008207 – Apache Struts2 Remote Code Execution Vulnerability (CVE-2017-5638)
- 1009265 – Apache Struts OGNL Expression Remote Command Execution Vulnerability (CVE-2018-11776)
- 1008970 – Drupal Core Remote Code Execution Vulnerability (CVE-2018-7600)
Integrity monitoring detections:
- Unix – Monitor Processes Running From ‘/tmp’ Directories (ATT&CK T1059)
Log inspection detections:
- 1002828 – Application – Secure Shell Daemon (SSHD)
- 1002792 – Default Rules Configuration
Trend Micro Cloud One™ – Network Security
The following set of detections were found with Network Security. This solution provides defense in depth by inspecting ingress and egress traffic and providing virtual patching as well as post-compromise detection and disruption.
- 29068: HTTP: Apache Struts 2 Struts 1 Plugin Remote Code Execution Vulnerability
- 27410: HTTP: Apache Struts Multipart Encoding Command Injection Vulnerability
- 32892: HTTP: OGNL Entity Usage in an HTTP URI
- 31031: HTTP: Drupal Core Multiple Subsystems Input Validation Vulnerability
Read More HERE