Protecting on-premises Exchange Servers against recent attacks

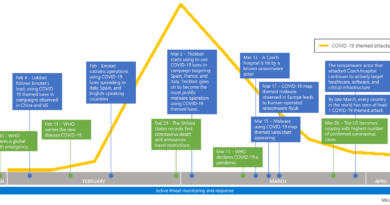
For the past few weeks, Microsoft and others in the security industry have seen an increase in attacks against on-premises Exchange servers. The target of these attacks is a type of email server most often used by small and medium-sized businesses, although larger organizations with on-premises Exchange servers have also been affected. Exchange Online is not vulnerable to these attacks.
While this began as a nation-state attack, the vulnerabilities are being exploited by other criminal organizations, including new ransomware attacks, with the potential for other malicious activities.
This is now what we consider a broad attack, and the severity of these exploits means protecting your systems is critical. While Microsoft has regular methods for providing tools to update software, this extraordinary situation calls for a heightened approach. In addition to our regular software updates, we are also providing specific updates for older and out-of-support software with the intent to make it as easy as possible to quickly protect your business.
The first step is making sure all relevant security updates are applied to every system. Find the version of Exchange Server you are running and apply the update. This will provide protection for known attacks and give your organization time to update servers to a version that has a full security update.
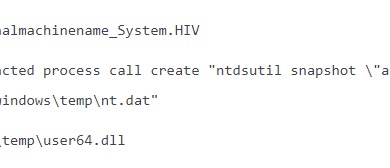
The next critical step is to identify whether any systems have been compromised, and if so, remove them from the network. We have provided a recommended series of steps and tools to help — including scripts that will let you scan for signs of compromise, a new version of the Microsoft Safety Scanner to identify suspected malware, and a new set of indicators of compromise that is updated in real time and shared broadly. These tools are available now, and we encourage all customers to deploy them.
Our customer service team has been working around the clock alongside hosting companies and our partner community to raise awareness with potentially affected customers. With the help of the community, we are working to raise awareness about these critical updates and tools with more than 400,000 customers.
To illustrate the scope of this attack and show the progress made in updating systems, we’ve been working with RiskIQ. Based on telemetry from RiskIQ, we saw a total universe of nearly 400,000 Exchange servers on March 1. By March 9 there were a bit more than 100,000 servers still vulnerable. That number has been dropping steadily, with only about 82,000 left to be updated. We released one additional set of updates on March 11, and with this, we have released updates covering more than 95% of all versions exposed on the Internet.
Finally, groups trying to take advantage of this vulnerability are attempting to implant ransomware and other malware that could interrupt business continuity. To best protect against this, we encourage all customers to review the ransomware guidance from the U.S. Cybersecurity Agency and Infrastructure Security as well as Microsoft’s own guidance on how to prepare for and protect against this sort of exploit.
This is the second time in the last four months that nation state actors have engaged in cyberattacks with the potential to affect businesses and organizations of all sizes. We continue to monitor these sophisticated attacks closely and apply the breadth and depth of our technology, human expertise, and threat intelligence to better prevent, detect, and respond.
Microsoft is deeply committed to supporting our customers against these attacks, to innovating on our security approach, and to partnering closely with governments and the security industry to help keep our customers and communities secure.
READ MORE HERE