Protect against phishing with Attack Simulation Training in Microsoft Defender for Office 365

Sophisticated cyberattacks are on the rise, with email phishing as the most common attack vector. We’ve seen it all over the news with stories like Hafnium that targeted Exchange servers1 or the Nobelium attack against SolarWinds,2 which show just how easy it is for bad actors to distribute a malicious URL and gain sustained access to networks to install ransomware across a wide number of industries and verticals. Working from home poses a greater security risk as organizations are required to rely more heavily on email communication to run their businesses, and cybercriminals have an increased opportunity to phish users.
Attack Simulation Training helps mitigate phishing risk
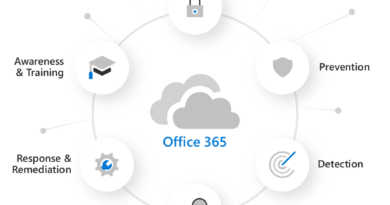
Microsoft has been working hard to understand these types of attacks and create solutions that help prevent, detect, and remediate vulnerability at the most basic point of attack: the user. Attack Simulation Training is one of those solutions. Attack Simulation Training is included in Microsoft Defender for Office 365 Plan 2 and E5 offerings and provides a behavior-based solution to mitigate phishing risk across your organization. It provides the necessary tools to run intelligent simulations and measure users for a baseline awareness of phishing risk, provide actionable insights and recommendations to remediate risk with hyper-targeted training designed to change behavior, and then measure behavioral progress against that benchmark through repeated simulation. This all happens straight from the Microsoft 365 Defender portal.
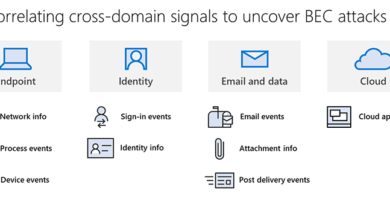
Attack Simulation Training was released as part of Microsoft Defender for Office 365 to ensure customers had a complete prevent, detect, investigate, and respond solution. Other offerings may only provide a portion of these capabilities. Microsoft Defender for Office 365 offers essential threat investigation and response capabilities to keep malicious communication from reaching users’ inboxes, and Attack Simulation Training provides the ability to test where vulnerabilities lie in your organization and reduce your phish risk score by educating users with a vast library of trainings. Together, both Microsoft Defender for Office 365 and Attack Simulation Training can prevent a future data compromise saving your organization time and unexpected costs.
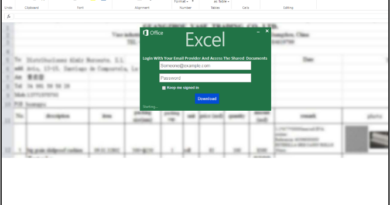
Through Attack Simulation Training’s intelligent automation, you can target your simulations by setting custom criteria and creating tailored payloads to fit your business. Additionally, you can leverage hundreds of premade email payloads in the template library that were modeled on real phishing attempts. After you run simulations, you’ll get several training options of content by Terranova Security that includes a variety of tailored courses, micro learnings, and nano learnings available in over 20 different languages. If you haven’t already, try Attack Simulation Training and learn how to set up a new phish simulation in this two-part blog series.
Learn more
At Microsoft, we keep our customers top of mind when making product investment decisions. Since we announced Attack Simulation Training at Ignite in 2020, we have made significant investments to ensure our customers have the best email simulation and training platform for their businesses. Two key investment areas that the product team recently made were:
- The ability for customers to access all the data that they have through Graph API reads. Learn more in our Tech Community blog post.
- The ability for organizations to customize anything on the landing page and make it their own, including adding their own branding. Read our blog post here.
You can also read more about Attack Simulation Training’s new regional availability and access all the latest product updates in the Attack Simulation Training blog series.
Watch our overview video of Attack Simulation Training to get a better feel of the user interface and some of its key reporting and insights capabilities.
Try Attack Simulation Training straight from the Microsoft 365 Defender portal and learn how to get started today!
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1HAFNIUM targeting Exchange Servers with 0-day exploits, Microsoft Threat Intelligence Center (MSTIC), Microsoft 365 Defender Threat Intelligence Team, Microsoft 365 Security, Microsoft. 2 March 2021.
2New sophisticated email-based attack from NOBELIUM, Microsoft Threat Intelligence Center (MSTIC), Microsoft 365 Defender Threat Intelligence Team, Microsoft. 27 May 2021.
READ MORE HERE