Preparing your enterprise to eliminate passwords

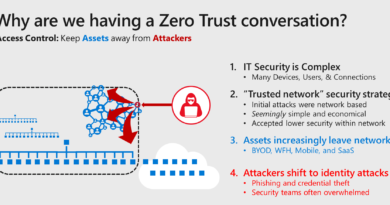
Anyone who uses the internet knows the hassles of using a user name and password to access their own information, whether it’s their banking, online shopping, social media, medical information, etc. If you’re a CIO, a CISO, or any other exec at a company who is thinking about digital security, the user name/password paradigm is more than a hassle, it’s a true security challenge, which keeps many of us up at night.
I can tell you that deploying a companywide strategy for eliminating passwords isn’t easy, but it’s also probably not as hard as you think, either. When I told our senior leaders that we’d be eliminating passwords in about 24 months, they applauded. When I said getting there would temporarily disrupt support for select line of business apps and devices, they had questions. What I share with you today is based on what we’ve learned in this process.
I’ve been talking about eliminating passwords for a while now, aligning to our principles for identity strategy, and the most common response I get from my peers is: “Great, how can I do it at my company?” Today, I’m outlining the basic steps necessary to eliminate passwords, with the acknowledgement that we’re still on the journey. I believe we’ve mapped out the right path, but we aren’t finished yet.
The first step is to segment the user population in your network. You’ll have to bifurcate your users into two groups: 1) those users in a compliance boundary (for example, people who handle credit card/payment information); and 2) everyone else. This segmentation is necessary because there are compliance requirements in some industries that essentially require using user names and passwords. Until the regulations catch up with the technology, the people in this segment will be forced to continue using passwords. The good news is that the rest of your user population is probably quite sizable and can move forward on the journey towards eliminating passwords.
Once the user population is segmented, the remaining steps can be pursued, and they don’t have to be done sequentially. If you follow these steps, you’ll have a vastly superior user experience for your employees and a more secure network while you’re on the path to ending passwords in your own environment:
- Banned passwords—Create a list of banned passwords that your user population is prevented from using. These are passwords that are commonly used, such as qwerty123, 123456, password1, and those that are easily guessable, like sports teams and month/year combinations. This list can be created using Azure Active Directory (Azure AD) password protection, which works in a hybrid environment and leverages machine learning from 650B authorizations every month. You could also create a list via other service offerings available in the industry.
- Use Multi–Factor Authentication (MFA)—MFA, or two-factor authentication, is a secure authentication method in which a user is only granted access after successfully presenting at least two separate pieces of evidence to an authentication mechanism. Using MFA is the single most effective security practice that companies are NOT employing. We employ MFA in our environment via Windows Hello, Microsoft Authenticator, and/or Azure MFA, but there are multiple options for implementing MFA including FIDO keys, smart cards, and tokens. In fact, we recently announced that companies can now go passwordless with the public preview of FIDO2 security keys support in Azure AD, making it even easier to implement MFA. And, contrary to popular belief, we are not a Microsoft-only environment; our network includes every operating system and platform available.
- Modernize hardware—Ideally, you would update your hardware to add biometric reader capabilities and Trusted Platform Module 2.0 (TPM2.0), or FIDO 2.0 and above. Biometrics can replace passwords and create a nearly friction-free experience for users. There are other hardware options that support MFA, which don’t provide a user experience as smooth as biometrics, but still support MFA and offer much better security. TPM technology provides hardware-based, security-related functions which can also be used in place of traditional passwords.
- Legacy authentication—The final and most difficult step in the process is eliminating the use of legacy authentication. This includes all protocols that use basic authentication and can’t enforce any type of second factor authentication. This step is time consuming, laborious, and can create headaches when it occasionally breaks services. If your company is already completely in the cloud, and doesn’t have any legacy authentication anywhere, you can eliminate passwords very quickly. For the rest of us, it will take longer. There are features in Azure AD that allow a view into the audit logs and help identify the applications which are using legacy authentication. One approach to this step is to block legacy authentication through conditional access.
My last advice is to think carefully about how you engage with users to implement all the steps I outlined in this blog. Promote the user benefits at the outset of your program. This is a lesson I learned the hard way. When we first started on this path, I started promoting the use of “MFA everywhere” to our employees. People interpreted this as requiring smart cards everywhere. They saw this as one more technical, cumbersome requirement from the IT department. Eventually I figured out that our employees were universally excited about eliminating passwords, so I communicated with them about how each step helped us with that goal. I got a much more positive response. When people see that our efforts make their experience better, it is easy to get their enthusiastic participation.
As I mentioned above, we’re still on this journey, and we’re wrestling with the same challenges everyone else faces. One thing I try to remember is the adage about not letting perfection stand in the way of progress. Taking any of the steps I’ve outlined above will help improve your security environment, even if the total elimination of passwords is something you won’t achieve for years. We haven’t achieved our end goal, but we’re making progress and currently over 90 percent of our employees are able to sign in to our network without entering a password. Once our users no longer need to enter a password for anything, we can eliminate passwords entirely. We believe we’ll achieve this in about 18-24 months. As we make progress on our quest to eliminate passwords, I’ll continue to share what we’ve learned.
To learn more about going passwordless visit The end of passwords.
READ MORE HERE