New Tesla Hack Gives Thieves Their Own Personal Key

Last year, Tesla issued an update that made its vehicles easier to start after being unlocked with their NFC key cards. Now, a researcher has shown how the feature can be exploited to steal cars.
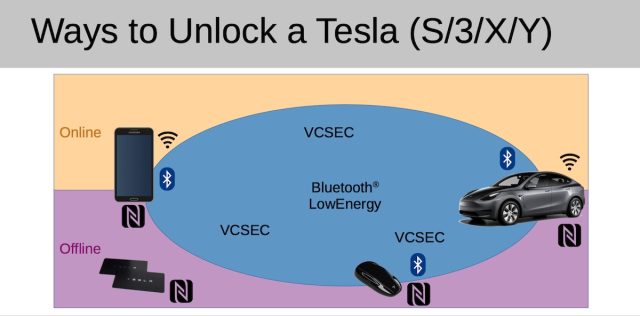
For years, drivers who used their Tesla NFC key card to unlock their cars had to place the card on the center console to begin driving. Following the update, which was reported here last August, drivers could operate their cars immediately after unlocking them with the card. The NFC card is one of three means for unlocking a Tesla; a key fob and a phone app are the other two.
Enrolling your own key
Martin Herfurt, a security researcher in Austria, quickly noticed something odd about the new feature: Not only did it allow the car to automatically start within 130 seconds of being unlocked with the NFC card, but it also put the car in a state to accept entirely new keys—with no authentication required and zero indication given by the in-car display.
“The authorization given in the 130-second interval is too general… [it’s] not only for drive,” Herfurt said in an online interview. “This timer has been introduced by Tesla… in order to make the use of the NFC card as a primary means of using the car more convenient. What should happen is that the car can be started and driven without the user having to use the key card a second time. The problem: within the 130-second period, not only the driving of the car is authorized, but also the [enrolling] of a new key.”
The official Tesla phone app doesn’t permit keys to be enrolled unless it’s connected to the owner’s account, but despite this, Herfurt found that the vehicle gladly exchanges messages with any Bluetooth Low Energy, or BLE, device that’s nearby. So the researcher built his own app, named Teslakee, that speaks VCSec, the same language that the official Tesla app uses to communicate with Tesla cars.
A malicious version of Teslakee that Herfurt designed for proof-of-concept purposes shows how easy it is for thieves to surreptitiously enroll their own key during the 130-second interval. (The researcher plans to release a benign version of Teslakee eventually that will make such attacks harder to carry out.) The attacker then uses the Teslakee app to exchange VCSec messages that enroll the new key.
All that’s required is to be within range of the car during the crucial 130-second window of it being unlocked with an NFC card. If a vehicle owner normally uses the phone app to unlock the car—by far the most common unlocking method for Teslas—the attacker can force the use of the NFC card by using a signal jammer to block the BLE frequency used by Tesla’s phone-as-a-key app.
This video demonstrates the attack in action:
As the driver enters the car after unlocking it with an NFC card, the thief begins exchanging messages between the weaponized Teslakee and the car. Before the driver has even driven away, the messages enroll a key of the thief’s choice with the car. From then on, the thief can use the key to unlock, start, and turn off the car. There is no indication from the in-car display or the legitimate Tesla app that anything is amiss.
Herfurt has successfully used the attack on Tesla Models 3 and Y. He hasn’t tested the method on new 2021+ facelift models of the S and X, but he presumes they are also vulnerable because they use the same native support for phone-as-a-key with BLE.
Tesla didn’t respond to an email seeking comment for this post.
READ MORE HERE



