Mylobot Botnet Emerges with Rare Level of Complexity
An unusual botnet dubbed Mylobot has emerged, percolating up from the Dark Web – and displaying a never-before-seen level of complexity in terms of the sheer breadth of its various tools, especially evasion techniques.
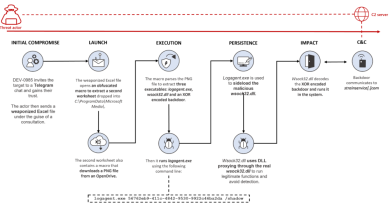
According to an analysis posted on Tuesday by Tom Nipravsky, a security researcher for Deep Instinct, Mylobot’s bag of tricks is bursting at the seams. These include anti-VM, anti-sandbox and anti-debugging techniques; wrapping internal parts with an encrypted resource file; code injection; process hollowing (where an attacker creates a new process in a suspended state, and replaces its image with the one that is to be hidden); reflective EXE, which involves executing EXE files directly from memory, without having them on disk; and, it also has a delaying mechanism of 14 days before accessing its C&C servers.
“The fact that everything takes place in memory (while executing the main business logic of the botnet in an external process using code injection) makes it even harder to detect and trace,” Nipravsky said.
In terms of function, Mylobot can be used to download whatever payload its bot herders choose, whether that’s cryptomining, ransomware, banking trojans, spyware or others. It could also be used for DDoS attacks.
“The main functionality of the botnet enables an attacker to take complete control of the user’s system – it behaves as a gate to download additional payloads from the command-and-control servers,” Nipravsky said. He also said that after examining the C&C server, it turns out that it has been used by other malware campaigns, all of which emanate from the Dark Web – so the threat actors behind Mylobot are likely involved in a range of activities.
Mylobot also hunts for other malware on target machines, and disables anything it comes across – an indicator of the mounting competition among cybercriminals for territory. The Dark Web has lowered the barrier of entry when it comes to the skills needed to get into the game, meaning that there are more and more players scrambling for a piece of the action.
“The Dark Web plays a critical part in the spread of malware: It’s rather simple accessibility of services and knowledge has made it easy for any attacker to gain much more abilities in minimum effort,” explained Nipravsky. “By using the Dark Web, anyone today can access an online market and purchase a malware. An attacker can purchase access to exploit kits, buy traffic of tens of thousands of users to a web page, or even buy a full ransomware-as-a-service for his own use.”
The botnet is one to watch, warned Nipravsky.
“Mylobot can result in loss of tremendous amount of data, the need to shut down computers for recovery purposes, which can lead to disasters in enterprises,” he said. “The fact that the botnet behaves as a gate for additional payloads, puts the enterprise in risk for leak of sensitive data as well, following the risk of keyloggers/banking trojans installations.”
READ MORE HERE