Microsoft works with healthcare organizations to protect from popular ransomware during COVID-19 crisis: Here’s what to do

True to form, human-operated ransomware campaigns are always on prowl for any path of least resistance to gain initial access to target organizations. During this time of crisis, as organizations have moved to a remote workforce, ransomware operators have found a practical target: network devices like gateway and virtual private network (VPN) appliances. Unfortunately, one sector that’s particularly exposed to these attacks is healthcare.
As part of intensified monitoring and takedown of threats that exploit the COVID-19 crisis, Microsoft has been putting an emphasis on protecting critical services, especially hospitals. Now more than ever, hospitals need protecting from attacks that can prevent access to critical systems, cause downtime, or steal sensitive information.
Why attackers are using human-operated ransomware
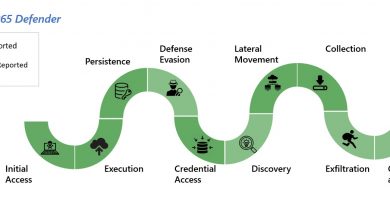
While a wide range of adversaries have been known to exploit vulnerabilities in network devices, more and more human-operated ransomware campaigns are seeing the opportunity and are jumping on the bandwagon. REvil (also known as Sodinokibi) is one of the ransomware campaigns that actively exploit gateway and VPN vulnerabilities to gain a foothold in target organizations. After successful exploitation, attackers steal credentials, elevate their privileges, and move laterally across compromised networks to ensure persistence before installing ransomware or other malware payloads.
Microsoft has been tracking REvil as part of a broader monitoring of human-operated ransomware attacks. Our intel on ransomware campaigns shows an overlap between the malware infrastructure that REvil was observed using last year and the infrastructure used on more recent VPN attacks. This indicates an ongoing trend among attackers to repurpose old tactics, techniques, and procedures (TTPs) for new attacks that take advantage of the current crisis. We haven’t seen technical innovations in these new attacks, only social engineering tactics tailored to prey on people’s fears and urgent need for information. They employ human-operated attack methods to target organizations that are most vulnerable to disruption—orgs that haven’t had time or resources to double-check their security hygiene like installing the latest patches, updating firewalls, and checking the health and privilege levels of users and endpoints—therefore increasing probability of payoff.
Human-operated ransomware attacks are a cut above run-of-the-mill commodity ransomware campaigns. Adversaries behind these attacks exhibit extensive knowledge of systems administration and common network security misconfigurations, which are often lower on the list of “fix now” priorities. Once attackers have infiltrated a network, they perform thorough reconnaissance and adapt privilege escalation and lateral movement activities based on security weaknesses and vulnerable services they discover in the network.
In these attacks, adversaries typically persist on networks undetected, sometimes for months on end, and deploy the ransomware payload at a later time. This type of ransomware is more difficult to remediate because it can be challenging for defenders to go and extensively hunt to find where attackers have established persistence and identify email inboxes, credentials, endpoints, or applications that have been compromised.
We saw something. We said something.
The global crisis requires everyone to step up, especially since attackers seem to be stepping up in exploiting the crisis, too, even as some ransomware groups purportedly committed to spare the healthcare industry. Through Microsoft’s vast network of threat intelligence sources, we identified several dozens of hospitals with vulnerable gateway and VPN appliances in their infrastructure. To help these hospitals, many already inundated with patients, we sent out a first-of-its-kind targeted notification with important information about the vulnerabilities, how attackers can take advantage of them, and a strong recommendation to apply security updates that will protect them from exploits of these particular vulnerabilities and others.
When managing VPN or virtual private server (VPS) infrastructure, it’s critical for organizations to know the current status of related security patches. Microsoft threat intelligence teams have observed multiple nation-state and cybercrime actors targeting unpatched VPN systems for many months. In October 2019, both the National Security Agency (NSA) and National Cyber Security Centre (NCSC) put out alerts on these attacks and encouraged enterprises to patch.
As organizations have shifted to remote work in light of the pandemic, we’re seeing from signals in Microsoft Threat Protection services (Microsoft Defender ATP, Office 365 ATP, and Azure ATP) that the attackers behind the REvil ransomware are actively scanning the internet for vulnerable systems. Attackers have also been observed using the updater features of VPN clients to deploy malware payloads.
Microsoft strongly recommends that all enterprises review VPN infrastructure for updates, as attackers are actively tailoring exploits to take advantage of remote workers.
How to detect, protect, and prevent this type of ransomware
The Department of Homeland Security (DHS) Cybersecurity and Infrastructure Security Agency (CISA) and Department of Commerce National Institute of Standards and Technology (NIST) have published useful guidance on securing VPN/VPS infrastructure.
We understand how stressful and challenging this time is for all of us, defenders included, so here’s what we recommend focusing on immediately to reduce risk from threats that exploit gateways and VPN vulnerabilities:
- Apply all available security updates for VPN and firewall configurations.
- Monitor and pay special attention to your remote access infrastructure. Any detections from security products or anomalies found in event logs should be investigated immediately. In the event of a compromise, ensure that any account used on these devices has a password reset, as the credentials could have been exfiltrated.
- Turn on attack surface reduction rules, including rules that block credential theft and ransomware activity. To address malicious activity initiated through weaponized Office documents, use rules that block advanced macro activity, executable content, process creation, and process injection initiated by Office applications. To assess the impact of these rules, deploy them in audit mode.
- Turn on AMSI for Office VBA if you have Office 365.
To help organizations build a stronger security posture against human-operated ransomware, we published a comprehensive report and provided mitigation steps for making networks resistant against these threats and cyberattacks in general. These mitigations include:
- Harden internet-facing assets and ensure they have the latest security updates. Use threat and vulnerability management to audit these assets regularly for vulnerabilities, misconfigurations, and suspicious activity.
- Secure Remote Desktop Gateway using solutions like Azure Multi-Factor Authentication (MFA). If you don’t have an MFA gateway, enable network-level authentication (NLA).
- Practice the principle of least-privilege and maintain credential hygiene. Avoid the use of domain-wide, admin-level service accounts. Enforce strong randomized, just-in-time local administrator passwords. Use tools like LAPS.
- Monitor for brute-force attempts. Check excessive failed authentication attempts (Windows security event ID 4625).
- Monitor for clearing of Event Logs, especially the Security Event log and PowerShell Operational logs. Microsoft Defender ATP raises the alert “Event log was cleared” and Windows generates an Event ID 1102 when this occurs.
- Determine where highly privileged accounts are logging on and exposing credentials. Monitor and investigate logon events (event ID 4624) for logon type attributes. Domain admin accounts and other accounts with high privilege should not be present on workstations.
- Utilize the Windows Defender Firewall and your network firewall to prevent RPC and SMB communication among endpoints whenever possible. This limits lateral movement as well as other attack activities.
We continue to work with our customers, partners, and the research community to track human-operated ransomware and other trends attackers are using to take advantage of this global crisis.
For more guidance on how to stay protected during this crisis, we will continue to share updates on our blog channels.
Microsoft Threat Protection Intelligence Team
Microsoft Threat Intelligence Center (MSTIC)
Talk to us
Questions, concerns, or insights on this story? Join discussions at the Microsoft Threat Protection tech community.
Read all Microsoft security intelligence blog posts.
Follow us on Twitter @MsftSecIntel.
READ MORE HERE