Microsoft and Zscaler help organizations implement the Zero Trust model
While digital transformation is critical to business innovation, delivering security to cloud-first, mobile-first architectures requires rethinking traditional network security solutions. Some businesses have been successful in doing so, while others still remain at risk of very costly breaches.
MAN Energy Solutions, a leader in the marine, energy, and industrial sectors, has been driving cloud transformation across their business. As with any transformation, there were challenges—as they began to adopt cloud services, they quickly realized that the benefits of the cloud would be offset by poor user experience, increasing appliance and networking costs, and an expanded attack surface.
In 2017, MAN Energy Solutions implemented “Blackcloud”—an initiative that establishes secure, one-to-one connectivity between each user and the specific private apps that the user is authorized to access, without ever placing the user on the larger corporate network. A virtual private network (VPN) is no longer necessary to connect to these apps. This mitigates lateral movement of bad actors or malware.
This approach is based on the Zero Trust security model.
Understanding the Zero Trust model
In 2019, Gartner released a Market Guide describing its Zero Trust Network Access (ZTNA) model and making a strong case for its efficacy in connecting employees and partners to private applications, simplifying mergers, and scaling access. Sometimes referred to as software-defined perimeter, the ZTNA model includes a “broker” that mediates connections between authorized users and specific applications.
The Zero Trust model grants application access based on identity and context of the user, such as date/time, geolocation, and device posture, evaluated in real-time. It empowers the enterprise to limit access to private apps only to the specific users who need access to them and do not pose any risk. Any changes in context of the user would affect the trust posture and hence the user’s ability to access the application.
Access governance is done via policy and enabled by two end-to-end, encrypted, outbound micro-tunnels that are spun on-demand (not static IP tunnels like in the case of VPN) and stitched together by the broker. This ensures apps are never exposed to the internet, thus helping to reduce the attack surface.
As enterprises witness and respond to the impact of increasingly lethal malware, they’re beginning to transition to the Zero Trust model with pilot initiatives, such as securing third-party access, simplifying M&As and divestitures, and replacing aging VPN clients. Based on the 2019 Zero Trust Adoption Report by Cybersecurity Insiders, 59 percent of enterprises plan to embrace the Zero Trust model within the next 12 months.
Implement the Zero Trust model with Microsoft and Zscaler
Different organizational requirements, existing technology implementations, and security stages affect how the Zero Trust model implementation takes place. Integration between multiple technologies, like endpoint management and SIEM, helps make implementations simple, operationally efficient, and adaptive.
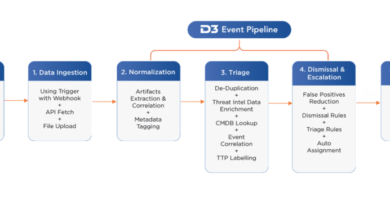
Microsoft has built deep integrations with Zscaler—a cloud-native, multitenant security platform—to help organizations with their Zero Trust journey. These technology integrations empower IT teams to deliver a seamless user experience and scalable operations as needed, and include:
Azure Active Directory (Azure AD)—Enterprises can leverage powerful authentication tools—such as Multi-Factor Authentication (MFA), conditional access policies, risk-based controls, and passwordless sign-in—offered by Microsoft, natively with Zscaler. Additionally, SCIM integrations ensure adaptability of user access. When a user is terminated, privileges are automatically modified, and this information flows automatically to the Zscaler cloud where immediate action can be taken based on the update.
Microsoft Endpoint Manager—With Microsoft Endpoint Manager, client posture can be evaluated at the time of sign-in, allowing Zscaler to allow or deny access based on the security posture. Microsoft Endpoint Manager can also be used to install and configure the Zscaler app on managed devices.
Azure Sentinel—Zscaler’s Nanolog Streaming Service (NSS) can seamlessly integrate with Azure to forward detailed transactional logs to the Azure Sentinel service, where they can be used for visualization and analytics, as well as threat hunting and security response.
Implementation of the Zscaler solution involves deploying a lightweight gateway software, on endpoints and in front of the applications in AWS and/or Azure. Per policies defined in Microsoft Endpoint Manager, Zscaler creates secure segments between the user devices and apps through the Zscaler security cloud, where brokered micro-tunnels are stitched together in the location closest to the user.
If you’d like to learn more about secure access to hybrid apps, view the webinar on Powering Fast and Secure Access to All Apps with experts from Microsoft and Zscaler.
Rethink security for the cloud-first, mobile-first world
The advent of cloud-based apps and increasing mobility are key drivers forcing enterprises to rethink their security model. According to Gartner’s Market Guide for Zero Trust Network Access (ZTNA) “by 2023, 60 percent of enterprises will phase out most of their remote access VPNs in favor of ZTNA.” Successful implementation depends on using the correct approach. I hope the Microsoft-Zscaler partnership and platform integrations help you accomplish the Zero Trust approach as you look to transform your business to the cloud.
For more information on the Zero Trust model, visit the Microsoft Zero Trust page. Also, bookmark the Security blog to keep up with our expert coverage on security matters and follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE