Malware That Spits Cash Out Of ATMs Has Spread Across The World
At 10am on a late November morning in Freiburg, Germany, a bank employee noticed something was wrong with a bank ATM.
It had been hacked with a piece of malware called “Cutlet Maker” that is designed to make ATMs eject all of the money inside them, according to a law enforcement official familiar with the case.
“Ho-ho-ho! Let’s make some cutlets today!” Cutlet Maker’s control panel reads, alongside cartoon images of a chef and a cheering piece of meat. In an apparent Russian play-on-words, a cutlet not only means a cut of meat, but a bundle of cash, too.
A joint investigation between Motherboard and the German broadcaster Bayerischer Rundfunk (BR) has uncovered new details about a spate of so-called “jackpotting” attacks on ATMs in Germany in 2017 that saw thieves make off with more than a million Euros. Jackpotting is a technique where cybercriminals use malware or a piece of hardware to trick an ATM into ejecting all of its cash, no stolen credit card required. Hackers typically install the malware onto an ATM by physically opening a panel on the machine to reveal a USB port.
In some cases, we have identified the specific bank and ATM manufacturer affected. Although a European non-profit said jackpotting attacks have decreased in the region in the first half of this year, multiple sources said the number of attacks in other parts of the world has gone up. Attacked regions include the U.S., Latin America, and Southeast Asia, and the issue impacts banks and ATM manufacturers across the financial industry.
“The U.S. is quite popular,” a source familiar with ATM attacks said. Motherboard and BR granted multiple sources, including law enforcement officials, anonymity to speak more candidly about sensitive hacking incidents.
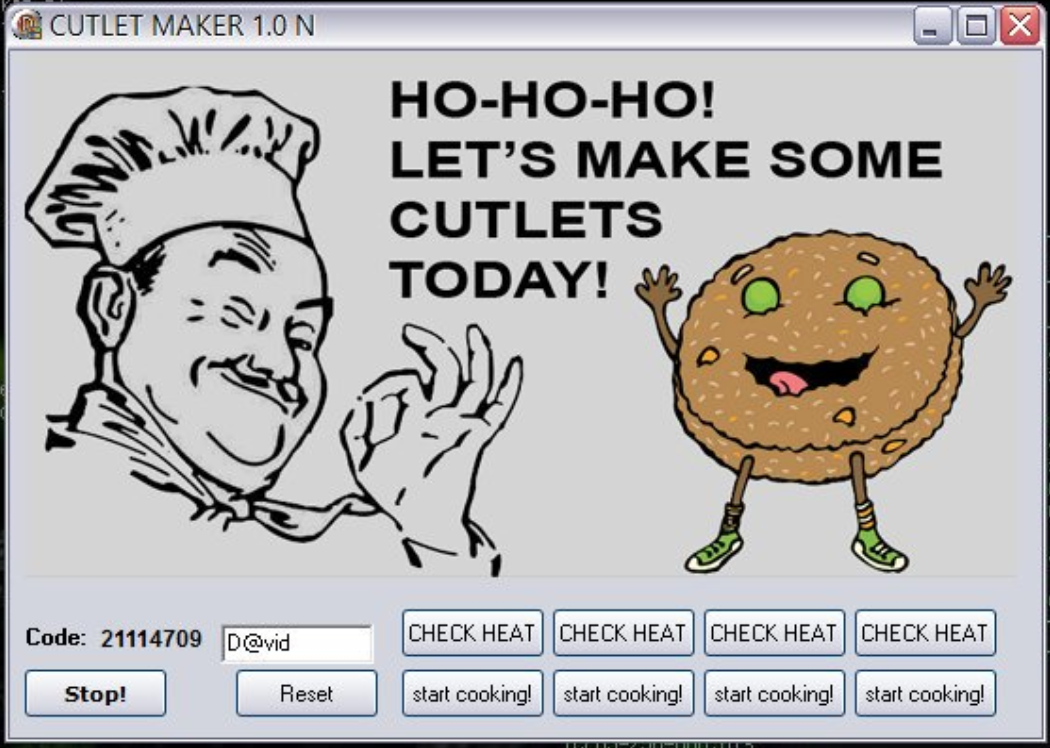
A screenshot of the Cutlet Maker control panel. Image: Twitter account of @CryptoInsane
*
During the annual Black Hat cybersecurity conference in 2010, late researcher Barnaby Jack demonstrated live on stage his own strain of ATM malware. The audience broke into applause as the ATM displayed the word “JACKPOT” and ejected a steady stream of bank notes.
Now, similar attacks have been deployed in the wild.
In that Freiburg instance no cash was stolen, the law enforcement official said. But Christoph Hebbecker, a prosecuting attorney for the German state of North Rhine-Westphalia, said his office is investigating 10 incidents that took place between February and November 2017, including attacks in which thieves did make off with bundles of cash. In all, hackers stole 1.4 million Euro ($1.5 million), Hebbecker said.
Hebbecker added that because of the similar nature of the attacks, he believes they are all linked to the same criminal gang. In some cases, the prosecutors have video evidence, but they have no suspects so far, they added.
“The investigation is still ongoing,” Hebbecker said in an email in German.
Multiple sources said a number of the 2017 attacks in Germany impacted the bank Santander; two sources said they specifically involved the Wincor 2000xe model of ATM, made by the ATM manufacturer Diebold Nixdorf.
“In general, we do not comment on dedicated, single cases,” Bernd Redecker, director of corporate security and fraud management at Diebold Nixdorf, said in a phone call. “However, we are of course dealing with our customers on jackpotting, and we are aware of these cases.” Diebold Nixdorf has also sold these ATMs to the U.S. market.

An overview of the 2000xe model of ATM. Image: Wincor Nixdorf.
A Santander spokesperson said in an emailed statement, “Protecting our customers’ information and the integrity of our physical network is at the core of what we do. Our experts are involved at every stage of product development and operations to protect customers and the bank from fraud and cyber threats. This focus on protecting our data and operations prevents us from commenting on specific security issues.”
Officials in Berlin said they had faced at least 36 jackpotting cases since spring 2018, resulting in several thousand Euro being stolen. They declined to name the specific malware used.
In all, authorities have recorded 82 jackpotting attacks in Germany across different states in the past several years, according to police spokespeople. However, not all of those attacks resulted in successful cash-outs.
Do you know about other jackpotting attacks? We’d love to hear from you. Using a non-work phone or computer, you can contact Joseph Cox securely on Signal on +44 20 8133 5190, Wickr on josephcox, OTR chat on jfcox@jabber.ccc.de, or email joseph.cox@vice.com.
It’s important to remember ATM jackpotting is not limited to a single bank or ATM manufacturer, though. It is likely the other attacks impacted banks other than Santander; those are simply the attacks our investigation identified.
“You will see this across all vendors; this is not dedicated towards a specific machine, nor towards a specific brand, and definitely not a region,” Redecker said.
Part of the security issue for ATMs is that many of them are, in essence, aged Windows computers.
“These are very old, slow machines,” the source familiar with ATM attacks said.
ATM manufacturers have made security improvements to their devices, Redecker from Diebold Nixdorf stressed. But that doesn’t necessarily mean all ATMs across the industry will be up to the same standard.
And responsibility on securing access to the ATMs falls on the banks too.
“In order to execute a jackpotting attack, you have to have access to the internal components of the ATM. So, preventing that first physical attack on the ATM goes a long way toward preventing the jackpotting attack,” David N. Tente, executive director of USA, Canada & Americas at the ATM Industry Association (ATMIA), said in an email.
Redecker said he’s been seeing attacks across the globe since 2012, with Germany suffering its first jackpotting attacks in Berlin in 2014.
Around the time of the 2017 attacks, researchers at cybersecurity firm Kaspersky published research showing Cutlet Maker for sale on hacking forums since May of that year. It seemed anyone with a few thousand dollars could buy the malware, and have a go at jackpotting ATMs themselves.
“The bad guys are selling these developments [malware] to just anybody,” David Sancho, senior threat researcher at cybersecurity firm Trend Micro, and who works with Europol on jackpotting research, said. That has enabled smaller outfits or enterprising criminals to start targeting ATMs, he added.
“Potentially this can affect any country in the world,” Sancho said.
Motherboard spoke to one cybercriminal claiming to sell the Cutlet Maker malware.
“Yes I’m selling. It costs $1000,” they wrote in an email, adding that they can offer support on how to use the tool as well. The seller provided screenshots of an instruction manual in Russian and English, which steps potential users through how to empty an ATM. Sections of the manual include how to check how many banknotes are inside the ATM, and installing the malware itself.
The European Association for Secure Transactions (EAST), a non-profit that tracks financial fraud, said jackpotting attacks decreased 43 percent over the previous year, in a report published this month. But it’s worth stressing that EAST’s report only covers Europe.
“It happens in parts of the world where they don’t have to tell anybody about it,” the source familiar with ATM attacks added. “It’s increasing, but, again, the biggest problem we’ve got is that nobody wants to report this.”
That lowering of the barrier of entry to ATM malware has arguably driven to some of the spike in jackpotting attacks. In January 2018, the Secret Service began warning financial institutions of the first jackpotting attacks in the U.S., although those used another piece of ATM malware called Ploutus.D.
“Globally, our 2019 survey indicates that jackpotting attacks are increasing,” Tente from ATMIA wrote in an email.
As the source familiar with ATM attacks said, “There are attacks happening, but a lot of the time it’s not publicized.”
Subscribe to our new cybersecurity podcast, CYBER.
READ MORE HERE


