How to manage Microsoft Windows BitLocker
This is Susan Bradley for CSO online. Today we’re going to talk about ways that we can determine if we’ve got bit locker enabled on our machines. But first a little bit of background as to why this topic came up. Recently in the July updates all of the servicing stacks for Windows 10 came out with updates to address an issue with Secure Boot feature that may cause bit locker to go into recovery mode because of a race condition. As you can see in the KB article our security section for all of the servicing stack patches for Windows 10 all the way back to Windows Server 2012 all received the servicing stack update to fix this issue. This first came up in May updates when Jody McCarter on the patch management dot org list identified that certain updates were causing this issue. If you had bit locker enabled you had a hard time patching that month. On some machines it bit locker was enabled, it actually caused the system to not boot properly. You had to go in suspend bit locker. And then go ahead and install the update. Now normally bit locker is a very quiet technology. It cooperates very well with Windows Update. This time it didn’t. And it brought up the question in my mind of do we have at our fingertips at a moment’s notice ways that we can identify which machines do and do not have bit locker. One of the easiest ways of course is PowerShell.
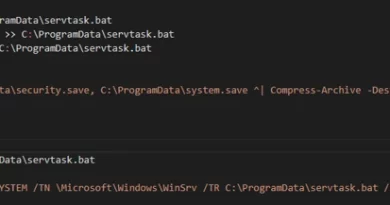
From a PowerShell command prompt type and manage dash B dash status C.
And it reports if the system is encrypted or not. Takes a little bit of time. But it comes back with the status. And then it comes back with their support of the system indicating the drive is full encrypted. One thing to think about when rolling out Bitlocker is ways to help the end user self recover. Again not the bit locker usually has problems with updating but in case you do have issues it’s wise to have a plan in place so the end users have the ability to get back that recovery key. There’s a couple of ways you can do it. If you have a Azure Active Directory you can actually hook it in and have it available in their portal. As you can see from the account Active Directory windows page. My home computer is Azure Active Directory joined. And if I had an issue all I’d have to do is log in with my credentials and I could click here and get that bit locker key. If you don’t have Azure Active Directory let’s say you just use Microsoft accounts. Those bitlocker recovery keys are automatically uploaded to a Microsoft account site. In fact if you’ve ever purchased surface devices you may not realize this but if you log in automatically with a Microsoft account those bit locker recovery keys are automatically saved up in the cloud. You go to account at Microsoft dot com slash devices and your bit locker recovery keys are there. You may even have recovery keys from long ago devices. Here I’ve got some old old surface devices that I don’t even have around anymore and still have the bit locker recover key up in the cloud. Bottom line there’s many ways to control and manage this bit locker keys. Until the next time this is Susan Bradley for CSO Online.
READ MORE HERE