How Microsoft Defender for IoT can secure your IoT devices
Cybersecurity threats are always evolving, and today we’re seeing a new wave of advanced attacks specifically targeting IoT devices used in enterprise environments as well as operational technology (OT) devices used in industrial systems and critical infrastructure (like ICS/SCADA). It’s not surprising since 60 percent of security practitioners believe IoT and OT security is one of the least secured aspects of their organization and less than 50 percent of organizations have deployed solutions designed specifically to secure their IoT and OT devices. Customers recognize that these types of devices are often unpatched, misconfigured, and unmonitored, making them the ideal targets for attackers.
To address these risks, we’re excited to announce Microsoft Defender for IoT, formerly Azure Defender for IoT, is adding agentless monitoring capabilities to secure enterprise IoT devices connected to IT networks [like Voice over Internet Protocol (VoIP), printers, and smart TVs], so organizations can take advantage of a single integrated solution that can secure all of their IoT and OT infrastructure. Access to the public preview of these new capabilities will be available on November 30, 2021.
Threats and customer challenges
In the past, attacks on IoT and OT devices for many organizations seemed like a hypothetical threat but in recent years organizations have learned otherwise. We’ve seen attacks on cameras and VoIP devices,1 smart building automation,2 service providers providing IoT services, and then there have been ransomware attacks—like the ones that shut down a major gas pipeline3 and global food processor. All of these highlight the challenge of securing IoT and OT devices.
There are many ways attackers will attempt to compromise and take advantage of enterprise IoT devices. They can be used as a point of entry, for lateral movement, or evasion just to name a few examples. The following chart below depicts a cyber kill chain involving two IoT devices. One is used as a point of entry, and another is used for lateral movement that inevitably leads to the exfiltration of sensitive information.

Figure 1: Attackers scan the internet for vulnerable internet-facing IoT devices and then use them as a point of entry. Next, they will perform reconnaissance and lateral movement to achieve their goals.
While most organizations recognize IoT and OT security as the least secured aspects of their organization, they continue to deploy devices at high rates and with little hesitation due to the demand for digital transformation and to remain competitive. Due to this, Chief Information Security Officers will soon be responsible for an attack surface area that is many times larger than what they are used to today and a vast majority of that new surface area will be unmanaged IoT and OT devices.
When it comes to IoT and OT security, organizations face a long list of challenges. Some of the top challenges include:
- Lack complete visibility to all their IoT and OT asset inventory.
- Lack detailed IoT and OT vulnerability management capabilities.
- Lack of mature detections for IoT and OT-specific attacks.
- Lack of insights and automation that an integrated SIEM and extended detection and response solution can bring.
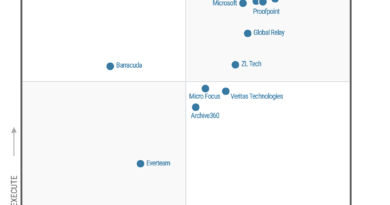
Because of these threats and challenges, security and risk leaders ranked the IoT and cyber-physical systems as their top concerns for the next three to five years.4
Microsoft Defender for IoT is part of the Microsoft SIEM and XDR offering
We recognize that IoT is just one of the security inputs in a comprehensive threat protection strategy. For that reason, adding agentless enterprise IoT support to Microsoft Defender for IoT and making it part of our broader SIEM and XDR offer, enables us to deliver comprehensive security for all your endpoint types, applications, identities, and more. Customers will now be able to get the same types of vulnerability management, threat detection, response, and other capabilities for enterprise IoT devices that were previously only available for managed endpoints and OT devices. With it, organizations get the visibility and insights they need to address complex multi-stage attacks that specifically take advantage of IoT and OT devices to achieve their goals. Learn more about Microsoft 365 Defender, Microsoft Defender for Cloud, and Microsoft Sentinel.
Our customers tell us that the biggest challenge they face when it comes to securing enterprise IoT devices is gaining enough visibility to locate, identify, and secure their complete IoT asset inventory. Defender for IoT takes a unique approach to solve this challenge and can help you discover and secure your IoT devices within Microsoft 365 Defender environments in minutes. We’ll share more about our unique approach in the passive, agentless architecture section below.

Figure 2: View your complete IT and IoT inventory alongside the rest of your IT devices (workstations, servers, and mobile) within a single unified view.
The second biggest challenge our customers face is related to vulnerability management. Defender for IoT can perform assessments for all your enterprise IoT devices. These recommendations are surfaced in the Microsoft 365 console (for example, Update to a newer version of Bash for Linux).

Figure 3: Prioritize vulnerabilities and misconfigurations and use integrated workflows to bring devices into a more secure state.
The third biggest challenge we hear about is related to threat detection. To ensure we have leading-edge efficacy for enterprise IoT threats, we’ve tasked Section 52, our in-house IoT and OT security research team, to ensure we have the best possible detection capabilities. Section 52’s work recently enabled Defender for IoT to rank number 1 in threat visibility coverage in the MITRE ATT&CK for ICS evaluation, successfully detecting malicious activity for 100 percent of major attack steps and 96 percent of all adversary sub-steps (with fewest missed detections of any other vendor).
Defender for IoT customers benefit from the machine learning and threat intelligence obtained from trillions of signals collected daily across the global Microsoft ecosystem (like email, endpoints, cloud, Azure Active Directory, and Microsoft 365), augmented by IoT and OT-specific intelligence collected by our Section 52 security research team. Because Section 52 works in close collaboration with domain experts across the broader Microsoft security research and threat intelligence teams—Microsoft Threat Intelligence Center (MSTIC) and Microsoft Security Response Center (MSRC)—we enable our customers to reduce the alert signal to noise ratio by providing them with prioritized incidents that render end-to-end attacks in complete context rather than giving them an endless list of uncorrelated alerts. This will lead to high efficacy incident response.

Figure 4: View prioritized incidents that are inclusive of IT and IoT devices all in a single dashboard to reduce confusion, clutter, investigation times, and alert fatigue.
Finally, one of the last things our customers have shared is that they struggle with finding solutions that will enable them to securely meet the promise of IT and OT network convergence initiatives.5 Most tools have difficulty providing analysts with a user experience that can correlate and render multi-stage attacks that cross IT and OT network boundaries.
Because Microsoft Defender for IoT is part of the broader Microsoft SIEM and XDR offer, we can provide analysts with the automation and visualization tools they need to address attacks crossing IT and OT network boundaries. Analysts can perform incident response holistically rather than as separate disconnected attacks that require extensive manual investigations to bring together. With these efficiency gains, analysts can stop attacks and bring their environments back to a pre-breach state far more quickly.

Figure 5: Deep contextual telemetry (like asset and connection details) combined with threat intelligence (like analytics rules, SOAR playbooks, and dashboards) from Section 52 helps analysts perform high-efficiency incident response.
Passive, agentless architecture
Some of the key design principles for Defender for IoT are to be non-invasive and to be easy to deploy. By using the existing Microsoft Defender for Endpoint clients, which are often deployed pervasively across an organization’s infrastructure, we can provide immediate device discovery with no additional deployment or configuration required. For the most complete view of your IoT and OT devices and specifically for network segments where Defender for Endpoint sensors are not present, Defender for IoT includes a deployable network sensor that can be used to collect all of the network data it needs for discovery, behavioral analytics, and machine learning.

Figure 6: A hybrid sensor approach using Defender for Endpoint clients as sensors provide customers with broad visibility on day one. Deploying the network sensor or using one from a third-party can ensure complete visibility and can be deployed over time.
Microsoft Defender for IoT is an open platform that allows customers to integrate third-party network data to enrich the information coming from multiple sources. For example, organizations that have already deployed Corelight’s open Network Detection and Response (NDR) platform and its Zeek-based network sensors can connect it to Defender for IoT enabling it to access raw network data from Corelight. From here Defender for IoT will apply its behavioral analytics and machine learning capabilities to discover and classify devices as well as protect, detect, and respond to attacks.
Learn more about our Corelight partnership and its integration within Microsoft Defender for IoT.
Get ready for the upcoming public preview!
While we’re excited to share all this news with you today, were even more excited to hear your feedback. Please join the new Microsoft Defender for IoT public preview which will be available on November 30, 2021. In the first build of the preview, you will have access to five main capabilities:
- An integrated view of IoT and OT Device Inventory available in the Azure console.
- Microsoft Defender for Endpoint clients will act as IoT network sensors and will add devices to Microsoft 365 Defender Device Inventory.
- An integrated IoT and OT Network Sensor will be available for deployment.
- IoT Threat and Vulnerability Assessments will be available in the Microsoft 365 Defender console.
- Support for third-party network sensors.
Additional new capabilities are expected to be released soon, including richer security recommendations, detections, and responses.
More details on the upcoming public preview and roadmap can be viewed in our Ignite session.
More information on the current release of Microsoft Defender for IoT (formerly Azure Defender for IoT) which offers OT security can be found in the following resources:
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1Microsoft: Russian state hackers are using IoT devices to breach enterprise networks, Catalin Cimpanu, ZDNet. 5 August 2019.
2Hackers are hijacking smart building access systems to launch DDoS attacks, Catalin Cimpanu, ZDNet. 2 February 2020.
3Hackers Breached Colonial Pipeline Using Compromised Password, William Turton, Kartikay Mehrotra, Bloomberg. 4 June 2021.
4Develop a Security Strategy for Cyber-Physical Systems, Susan Moore, Gartner. 13 April 2021.
5When IT and Operational Technology Converge, Christy Pettey, Gartner. 13 January 2017.
READ MORE HERE