How companies are securing devices with Zero Trust practices
Organizations are seeing a substantial increase in the diversity of devices accessing their networks. With employees using personal devices and accessing corporate resources from new locations in record numbers, IT leaders are seeing an increase in their attack surface area. They’re turning to Zero Trust security models to ensure they have the visibility they need, and their data is protected as its accessed from outside the corporate network using a wider variety of devices.
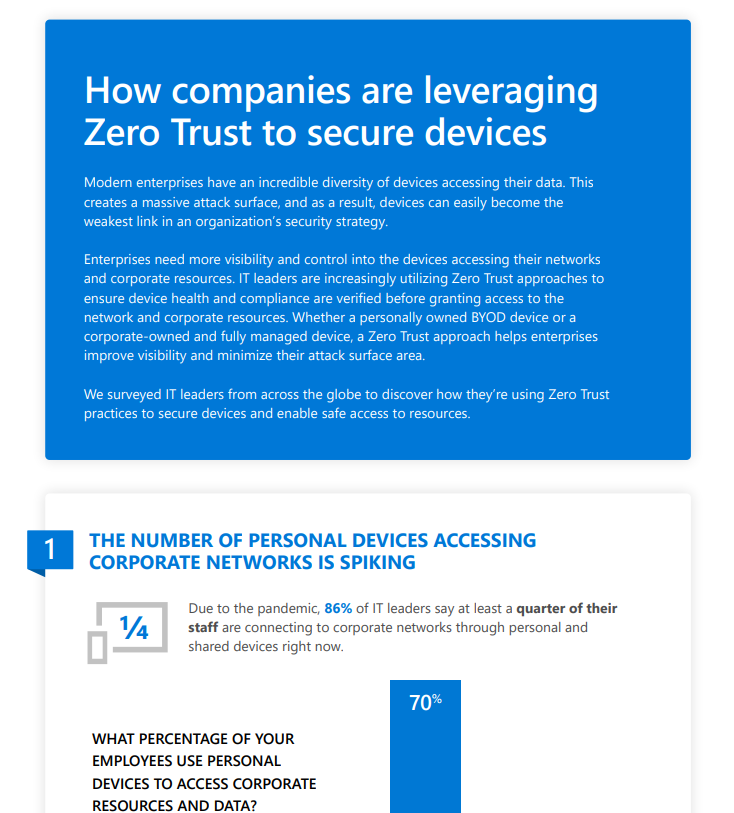
We surveyed IT leaders around the world to determine how they’re using Zero Trust practices to protect their devices and enable access to the corporate network from unsecured devices.
- More personal devices are accessing corporate resources than ever. In response to the substantial shift to remote work, IT leaders report seeing more of their employees using personal devices to access their networks. As a result, they’re prioritizing device management solutions to improve security and control on personal devices.
- Devices accessing the network are monitored but often left out of access decisions. While most IT leaders report that they’re monitoring device health and compliance, the majority aren’t currently using that status in their access decision making. Preventing unauthorized and risky devices is critical to protecting corporate data in a modern environment.
- Personal devices are widely agreed to increase risk exposure. Over 92 percent of IT leaders agree that a proliferation of personal devices is increasing their attack surface area. However, much less say they’re prepared for managing access from unsecured devices.
Check out the infographic for more details.
If you’re looking at how to help prevent devices from being the weakest link in your security strategy, check out our Zero Trust deployment guidance for endpoints.
To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE