Go inside the new Azure Defender for IoT including CyberX
In 2020, the move toward digital transformation and Industry 4.0 took on new urgency with manufacturing and other critical infrastructure sectors under pressure to increase operational efficiency and reduce costs. But the cybersecurity model for operational technology (OT) was already shown to be lacking before the pandemic. A series of major cyberattacks across industries served as a wake-up call that the traditional “air-gapped” model for OT cybersecurity had become outdated in the era of IT/OT convergence and initiatives such as Smart Manufacturing and Smart Buildings. And the IoT and Industrial Internet of things (IIoT) are only getting bigger. Analysts predict we’ll have billions of IoT devices connected worldwide in a few years, drastically increasing the surface area for attacks.
Company boards and management teams are understandably concerned about increased safety and corporate liability risks as well as the financial impact of crippling downtime posed by IoT/OT breaches. They’re also concerned about losing sensitive IP such as proprietary formulas and product designs, since manufacturers are eight times more likely to be attacked for cyberespionage than other sectors, according to the 2020 Verizon DBIR.1
In my recent Microsoft Ignite presentation, Azure Defender for IoT including CyberX, I was joined by Nir Krumer, Principal PM Manager at Microsoft, to examine how the new Azure Defender for IoT incorporates CyberX’s agentless technology and IoT/OT-aware behavioral analytics, minimizing those risks by providing IT teams with continuous IoT/OT visibility into their industrial and critical infrastructure networks. You’re invited to view the full presentation and review some highlights below.
IT versus OT
Unlike information technology (IT) security, OT security is focused on securing physical processes and assets rather than digital assets like containers and SQL databases. Physical assets include devices like turbines, mixing tanks, HVAC systems in smart buildings and data centers, factory-floor machines, and more. In OT, the top focus is always on safety and availability. Availability means that your production facilities must be resilient and keep operating, because that’s where the revenue comes from. However, the biggest difference from IT security is that most chief information security officers (CISOs) and SOC teams today have little or no visibility into their OT risk, because they don’t have the multiple layers of controls and telemetry as we have in IT environments. And OT risk translates directly into business risk.
As recent history shows, attacks on OT are already underway. The TRITON attack on the safety controllers in a Middle East petrochemical facility was intended to cause major structural damage to the facility and possible loss of life. The attackers got their initial foothold in the IT network but subsequently used living-off-the-land (LOTL) tactics to gain remote access to the OT network, where they deployed their purpose-built malware. As this attack demonstrated, increased connectivity between IT and OT networks gives adversaries new ways of compromising unmanaged OT devices, which historically haven’t supported agents and are typically invisible to IT teams.
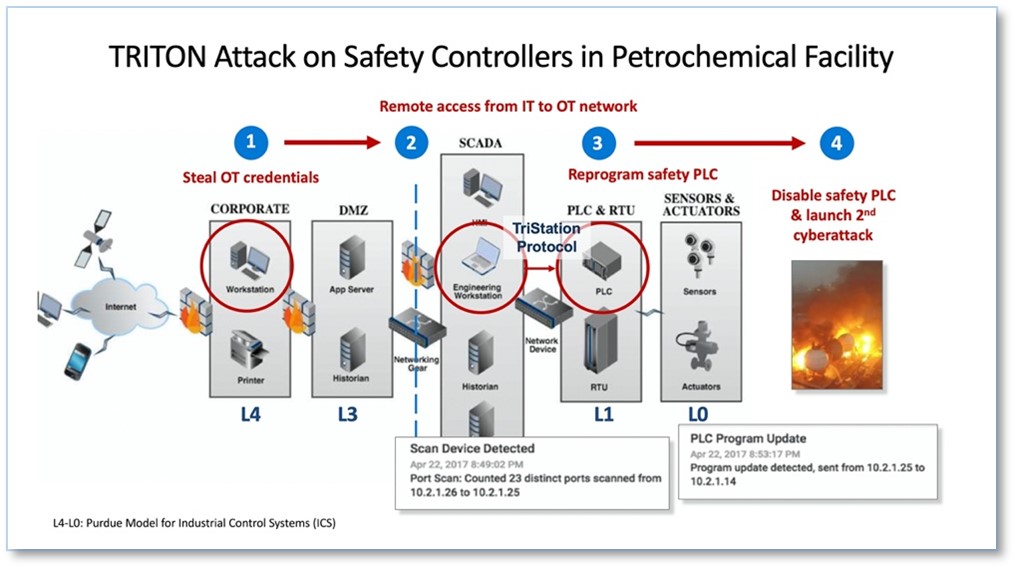
Figure 1: Purdue Model traversal in TRITON attack.
How Azure Defender for IoT works for you
By incorporating agentless technology from Microsoft’s recent acquisition of CyberX, Azure Defender for IoT enables IT and OT teams to identify critical vulnerabilities and detect threats using IoT/OT-aware behavioral analytics and machine learning—all without impacting availability or performance.
In our Ignite presentation, we broke down five key capabilities provided by the product’s agentless security for unmanaged IoT/OT devices:
- Asset discovery: Because you cannot protect what you do not know you have, Azure Defender tells you what IoT/OT devices are in your network and how they’re communicating with each other. Also, if you’re implementing a Zero Trust policy, you need to know how these devices are connected so you can segment them onto their own network and manage granular access to them.
- Risk and vulnerability management: Azure Defender helps you identify vulnerabilities such as unauthorized devices, unpatched systems, unauthorized internet connections, and devices with unused open ports—so you can take a prioritized approach to mitigating IoT/OT risk for your crown jewel assets. These are the critical devices whose compromise would have a major impact on your organization, such as a safety incident, loss of revenue, or theft of sensitive IP.
- Continuous IoT threat monitoring and response: Azure Defender continuously monitors the OT network using Layer 7 Deep Packet Inspection (DPI), informing you immediately when there has been unusual or unauthorized behavior, and empowering you to mitigate an attack before it causes a production failure or safety incident. It incorporates a deep understanding of all major industrial protocols (including Modbus, DNP3, Siemens S7, Ethernet/IP CIP, GE-SRTP, and Yokogawa) and patented, IoT/OT-aware behavioral analytics to detect threats faster and more accurately, with a far shorter learning period than generic baselining algorithms.
- Operational efficiency: When you have malfunctioning or misconfigured equipment, you need to quickly figure out what went wrong. By providing deep visibility into what’s going on in the network—such as a misconfigured engineering workstation that’s constantly scanning the network—you can help your IoT/OT engineers quickly identify and address the root cause of those issues.
- Unified IT/OT security monitoring and governance: Azure Defender for IoT is deeply integrated with Azure Sentinel and also supports third-party tools such as Splunk, IBM QRadar, and ServiceNow. This helps break down silos that slow communication between IT and OT teams, and creates a common language between them to quickly resolve issues. It also enables you to quickly address attacks that cross IT/OT boundaries (like TRITON), as well as leverage the workflows and training you spent years building in your security operations center (SOC)—so you can apply them to IoT and OT security as well.
Deployment Architecture
So, how does this system get deployed? Azure Defender for IoT uses a network sensor to capture a copy of the network traffic through the switch port analyzer (SPAN). It uses a technique called passive monitoring or network traffic analysis (NTA) to identify assets, vulnerabilities, and threats without impacting the performance or reliability of the IoT/OT network. The solution can be 100 percent on-premises, connected to Azure, or a hybrid of the two (for example, by forwarding alerts to Azure Sentinel).
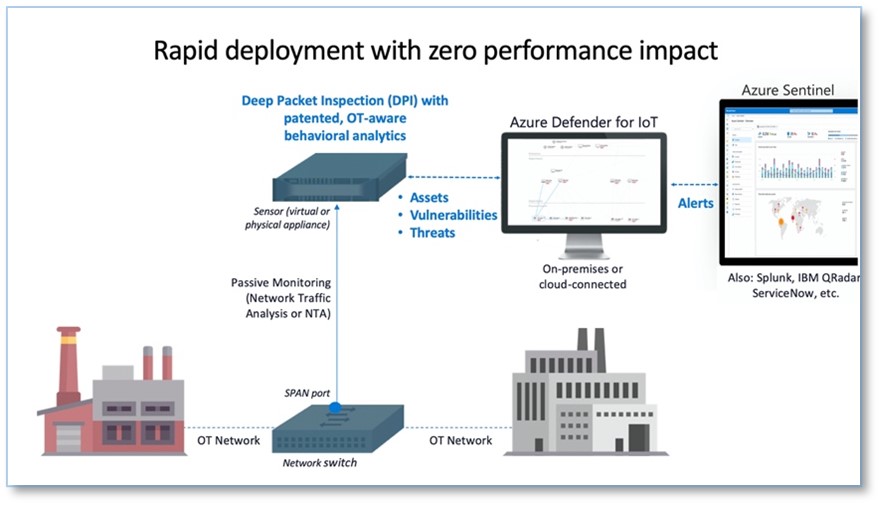
Figure 2: Azure Defender for IoT uses an on-premises network sensor to capture and analyze all IoT/OT traffic. The solution can be deployed fully on-premises, or connected to Azure, or in hybrid environments where the SIEM is cloud-based, as with Azure Sentinel.
Azure Sentinel integration
To enable rapid detection and response for attacks that cross IT/OT boundaries, Azure Defender is deeply integrated with Azure Sentinel—Microsoft’s cloud-native SIEM/SOAR platform. As a SaaS-based solution, Azure Sentinel delivers reduced complexity, built-in scalability, lower total cost of ownership (TCO), and continuous threat intelligence and software updates. It also provides built-in IoT/OT security capabilities, including:
- Deep integration with Azure Defender for IoT: Azure Sentinel provides rich contextual information about specialized OT devices and behaviors detected by Azure Defender—enabling your SOC teams to correlate and detect modern kill-chains that move laterally across IT/OT boundaries.
- IoT/OT-specific SOAR playbooks: Sample playbooks enable automated actions to swiftly remediate IoT/OT threats.
- IoT/OT-specific threat intelligence: In addition to the trillions of signals collected daily, Azure Sentinel now incorporates IoT/OT-specific threat intelligence provided by Section 52, our specialized security research team focused on IoT/OT malware, campaigns, and adversaries.
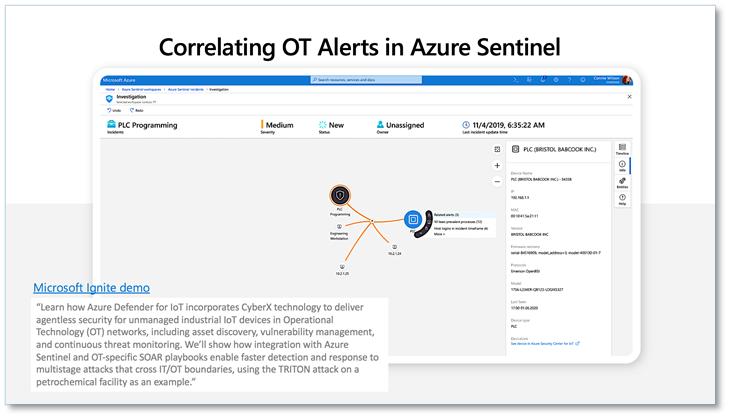
You are invited to watch our Microsoft Ignite presentation to learn more about Azure Defender for IoT, including a live demo of how deep integration with Azure Sentinel can be used to investigate multistage IT/OT attacks like TRITON.
Visit the Azure Defender for IoT website to learn more and try it for free during Public Preview. You can also learn more about Microsoft Security solutions by visiting our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1 2020 Verizon DBIR, pages 36 and 59.
READ MORE HERE