Discover what’s new and gain technical expertise from MISA at Ignite
It’s hard to believe we’re so close to the end of another year, and what a year it’s been. For too brief a time in some places, our masks were tossed away, only to find us digging them out of drawers again not long after. But masked up or not, it’s been good to see local restaurants buzzing with activity again, along with fans enjoying sporting events, concerts, and even some shows on Broadway. There’s a sense of expectation in the air, and I’m excited to see what 2022 has in store for all of us.
That renewed optimism can be seen in the continued growth of the Microsoft Intelligent Security Association (MISA) member base—now reaching 275 partners, with 273 product integrations and 243 managed service offerings. We have high expectations for the remainder of this fiscal year, including doubling our membership to roughly 450 as we continue partnering with even more leading-edge cybersecurity firms. We’re also expanding our product portfolio and are excited to announce that two new products for compliance, risk, and privacy are joining the MISA lineup.
Welcoming new compliance, risk, and privacy solutions
Microsoft compliance helps our customers comply with national, regional, and industry-specific requirements governing the collection and use of data. Through MISA, members get support in building managed services and integrations that help them:
- Identify and remediate critical risks within your organization.
- Safeguard sensitive data across clouds, apps, and endpoints.
- Assess compliance and respond to legal and regulatory requirements.
Advanced Audit in Microsoft 365
With Advanced Audit in Microsoft 365, you can conduct forensic and compliance investigations with visibility into user activities across Microsoft 365 services. Using audit log search in the Microsoft 365 compliance center and the Office 365 Management Activity API, Advanced Audit enables audit logs to be retained for up to 10 years, provides access to crucial events that determine the scope of a compromise, and helps with ongoing regulatory, legal, and internal obligations. Customers can specify how long to retain audit records according to a priority level, ensuring that specific policies take priority over others.
“Joining MISA brings our relationship with Microsoft to the next level, enabling seamless integrations for our joint customers using Office 365 and more,” said John Coyle, Vice President Business Development, Sumo Logic. “Our cloud-native integration with Microsoft Office 365’s Advanced Auditing capabilities enables customers to apply Sumo Logic’s powerful Continuous Intelligence Platform and Cloud SIEM, providing clear, detailed trails for rapid investigation of user activity to quickly identify potential breaches and scope of compromise in Microsoft Office 365 data.”
Privacy Management for Microsoft 365
Privacy Management for Microsoft 365 helps companies safeguard personal data and build a privacy resilient workplace by proactively identifying and protecting against privacy risks, such as data hoarding, data transfers, and data oversharing—empowering information workers to make smart data-handling decisions while automating and managing subject requests at scale. Privacy Management is available within the Microsoft 365 compliance center.
With our new Privacy APIs, we’re enabling a broader partner ecosystem to integrate with Privacy Management for Microsoft 365. This integration enables our partners to build solutions that automate the Microsoft 365 portion of subject rights requests. This helps our joint customers ensure that they are compliant with an ever-growing number of regulations across Microsoft 365, as well as non-Microsoft data sources.
“Joining MISA enhances our relationship with Microsoft and our commitment to providing a unified solution for organizations to automate their data security and privacy operations across all their structured and unstructured data systems,” said Vivek Kokkengada, Vice President of Products, Securiti. “Our new integration with Privacy Management for Microsoft 365 using Microsoft’s new Privacy APIs enables our joint customers to automatically fulfill the Microsoft 365 portion of subject rights requests within Privacy Management and ensure compliance with an ever-growing number of privacy regulations globally. Being a MISA member allows us to work closely with the Microsoft teams and stay on the forefront of new strategic integration opportunities to add value to our joint customers.”
Microsoft investing $20 billion in cybersecurity
During the White House Cybersecurity Summit on August 25, 2021, Microsoft Chairman and Chief Executive Officer Satya Nadella shared that the company will quadruple our cybersecurity investments, investing $20 billion to advance our security solutions over the next five years, and $150 million in technical services to help federal, state, and local governments upgrade their security protection. We will also expand partnerships with community colleges and non-profits for cybersecurity training. As many organizations are facing a shortage of cybersecurity professionals, we want to ensure everyone has and uses the protection available today. Watch chairman and president of Microsoft Brad Smith’s video announcement on CNBC.
Lower marketplace fees spur reseller engagement
As software needs rise, customers need to streamline how they buy and deploy software. With more than 30,000 solutions published, the commercial marketplace—Microsoft AppSource and Microsoft Azure Marketplace—is how we connect our customers and partners. To help drive these customer and partner connections, we’ve reduced fees to just 3 percent—down from an industry standard of 20 percent—for every transactable application published in the commercial marketplace. This reduction enables higher margins for partners while simplifying the fee structure.
Independent software vendors (ISVs) with transactable commercial marketplace offers can now set one price for customers and another price for Microsoft Cloud Solution Provider (CSP) partners. This allows ISVs to provide margin to their CSP partners, while CSP partners can also resell outside the commercial marketplace. This added flexibility can help create stronger connections among partners while incentivizing ISVs to share margins with resellers, making it more profitable for partners to sell Microsoft commercial marketplace offers.
Unlock this opportunity and gain access to millions of customers by publishing a solution and selling with us.
Securing the future with Zero Trust
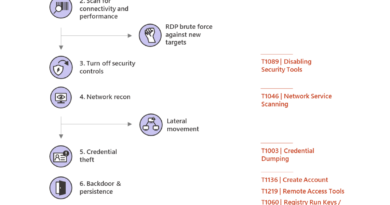
The recent string of disastrous ransomware attacks has shown all too clearly that traditional perimeter-based security can’t keep up with the complexity of today’s decentralized workplace.1 Shadow IT, hybrid work, and the proliferation of endpoints across IoT leave security teams stretched thin. Zero-day vulnerabilities, also known as unknown weaknesses in a network or software, have been implicated in recent attacks where threat actors breached organizations without being detected, giving them ample time to map internal networks, exfiltrate data, and locate additional attack vectors. At least 66 zero-day attacks have been found this year—almost twice the total of the previous year.2
Zero Trust is the essential security strategy for today’s reality. In 2020, the global pandemic compelled nearly every organization to embrace a Zero Trust strategy as employees went remote, virtual private networks (VPNs) were breached or overwhelmed, and digital transformation became critical to organizational sustainability Even the government and businesses worldwide recognized this imperative. In keeping with Section 3 of Executive Order 14028, Microsoft adheres to federal standards for Zero Trust as developed by the National Institute of Standards and Technology (NIST):
- All resource authentications are dynamic and strictly enforced before allowing access.
- Trust is evaluated before access is granted, and then only with the least privilege needed to complete the task.
- Assets should always act as if an attacker is present on the enterprise network.
At Microsoft, we’ve distilled these tenets into three Zero Trust principles: verify explicitly, use least privileged access, and assume breach. These principles form our strategic guidance toward customers, software development, and our global security posture.

Learn more
To assess your organization’s progress in the Zero Trust journey, use our Zero Trust Assessment tool. If you’d like to learn from our experience, Chief Information Security Officer Bret Arsenault and his team share insights from Microsoft’s Zero Trust journey over at Microsoft Inside Track. Finally, to understand how ISVs can integrate with Microsoft products to create Zero Trust solutions, see our Zero Trust integration guidance.
To learn more about MISA and other new developments, you can view a list of the Microsoft Ignite on-demand sessions here.
To learn more about upcoming big announcements, visit our latest blog posts:
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1What’s Driving the Surge in Ransomware Attacks? Matt Stieb, Intelligencer. 7 September 2021.
22021 has broken the record for zero-day hacking attacks, Patrick Howell O’Neill, MIT Technology Review. 23 September 2021.
READ MORE HERE