Detecting malicious key extractions by compromised identities for Azure Cosmos DB

Azure Cosmos DB is a fully managed NoSQL cloud database service for modern app development. It offers a variety of advanced built-in features, such as automatic worldwide data replication, lightning-fast response types, and a variety of APIs. In this blog post, we describe security practices for securing access to Azure Cosmos DB and show how monitoring relevant control plane operations, when performed by Microsoft Defender for Azure Cosmos DB, can help detect potentially compromised identities.
Authentication and authorization
Operating Azure Cosmos DB databases requires valid credentials to be provided for each request. The main type of credentials is a pair of access keys, known as primary and secondary, which are generated as part of the Azure Cosmos DB account creation and can be retrieved through management API using the ListKeys operation. These keys provide full control over the account, including configuration of databases, deployment of server-side logic, and common read and write data transactions. The keys are generated as a pair to enable continuous availability during key rotations. When the primary key is in use, the secondary key is being rotated, and vice versa.
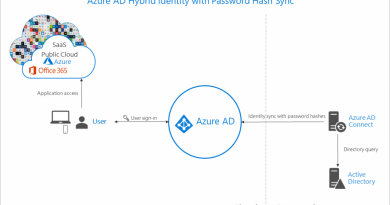
Another type of authentication and access control supported by Azure Cosmos DB is the role-based access control (RBAC) mechanism based on Microsoft Azure Active Directory (Azure AD).1 Principals authenticated in Azure AD can be assigned distinct roles that grant specific permissions to the databases and various objects in the Cosmos DB account. The roles can be chosen from several built-in alternatives or customized by the account owner.
Secured architecture controls
When an application design contains a database there are access control security practices that should be applied to improve the security posture. These practices are well known in database security and should be implemented through the built-in capabilities of Azure Cosmos DB. Here are two examples:
- Employ three-tier architecture to restrict access to databases only by application servers but not directly by clients. Implementation of such a design can be achieved by properly configuring the Cosmos DB firewall to provide access only to specific IP addresses or subnets.
- Assign least privileged access to the entities that communicate with the databases. By using RBAC authorization, as mentioned previously, it is possible to set a strict access model to Azure Cosmos DB and minimize its attack surface. Application servers that perform data transactions should be authorized to perform those, but not environment configuration activities such as deleting collections or uploading stored procedures. On the other hand, authorization to deployment operations can be given to engineering teams and continuous integration and continuous delivery (CI/CD) systems. When all the entities are configured with proper roles and access, it is advised to disable the access keys to mitigate a leaked key threat.
Cloud-based attack vector
With all the aforementioned security controls in place, there is another attack vector that needs to be addressed when securing a cloud application. The potential threat can be realized through authorized control plane access to Azure Resource Manager (ARM), which is responsible for resource provisioning and their configuration. In the context of Azure Cosmos DB, ARM can be queried to retrieve Cosmos DB access keys, as well as handle requests for changes in the database firewall rules. Bypassing the access control of the management interface is a high barrier for threat actors, so their widely adopted tactic is to get credentials through attacks on the users. Therefore, a supplemental layer of security against compromised customer accounts is achieved by continuous monitoring of authorized operations.
If the access keys are disabled according to security practices, then the key leakage scenario is not valid. An interesting point to note is that in these cases there are no entities that should perform the ListKeys operation. Thus, if it is monitored by a security service it serves as a detection of a potential compromise of the acting identity.
Monitoring suspicious key extractions
Data traffic of your Azure Cosmos DB accounts—including any attempts to access, read, or change the stored data—is monitored by Microsoft Defender for Azure Cosmos DB. Defender contains a growing collection of detections that cover various security scenarios. For example, signals are triggered when the account is accessed from an anomalous or suspicious location, an abnormally high amount of data is extracted, or a potentially malicious query is executed. In case a significantly suspicious pattern is detected, a security alert is sent to the account’s security administrator, with descriptive information and suggested steps to mitigate the detected threats and prevent future attacks. Securing and monitoring access to Azure Cosmos DB content is important and should be augmented with monitoring of control plane operations. In modern databases, such as Cosmos DB, authentication is provided using shared keys. If keys are leaked or compromised, their use by malicious actors blends among legitimate usage—as no individual user profile is visible in the data plane logs. Additionally, in case of attacks (such as data exfiltration for theft and data encryption for ransomware), early detection increases the effectiveness of incident response and reduces the damage.
Control plane monitoring enables the analyses of management activities of resources (such as changing access policies, and listing and setting access keys) and allows mapping them to authorized users. It is important to monitor management operations that are relevant for security scenarios. For example, accessing data in Azure Cosmos DB requires getting access keys, which appear as ListKeys operation in the control plane log. Other examples of operations include encryption and changing access policies or keys.
These operations are important, but in most cases they are normal and legitimate. However, if the operation is significantly anomalous (performed from an unexpected IP address, by a seldomly seen user, or using weak authentication, for example), it might indicate a malicious attempt to access the account and should be investigated by the resource owner. Alternatively, massive execution of such operations could indicate a breach even if no anomalous pattern exists.
We recommend flagging suspicious important management operations based on several types of indicators:
- New anomalous entity, such as previously unseen and unexpected source IP, application, and authentication type. In case the set of known entities is small enough, and no new entities are routinely appearing, any new entity is deemed unexpected. Thus, it might indicate either addition of a legitimate entity or the appearance of a malicious actor, and should be investigated.
- Anomalous pairing indicates an anomalous connection between two existing variables. For example, an important operation performed by a known user who previously never worked on a related resource group might indicate something like a compromised identity, or a connection between the source device and target resource that have never communicated before. This can be detected by modeling the probability of similarity of connection between meaningful pairs of variables.
- Suspicious indicators, such as source IPs flagged with threat intelligence signals, operation patterns resembling known penetration testing, or attack tool usage. Additional secondary indicators that increase the likelihood of potential misuse should be monitored as well. Examples include operations performed using weak authentication (no multifactor authentication) and suspicious errors (indicating potential reconnaissance efforts). These indicators are commonly derived from security research of known vulnerabilities and attack patterns.
- Mass operation: Even in case no anomalous indicators exist, a sufficiently high amount of successful or failed operations should be investigated due to potential high impact. Such an event can indicate enumerating or gaining access to resources en masse. Even though a substantial number of failed operations is a weaker signal, it is important, since it can be an early indication of an attack that employs blind scanning.
Various indicators can be integrated into cumulative anomaly scores for individual operations or a batch, depending on the scenario. Since the monitored operations are important, high anomaly scores may indicate a malicious access attempt and need to be investigated promptly. In the case of a true positive, real damage can be prevented before a malicious payload is executed. In the case of a false positive, the item can be quickly dismissed by the resource owner after steps for future prevention of such cases are considered.
Detect security threats with Microsoft Defender for Azure Cosmos DB
Microsoft Defender for Azure Cosmos DB is a part of Microsoft Defender for Cloud. It covers alerts on both the data plane and the control plane, detecting potential SQL injections, known bad actors based on Microsoft threat intelligence, suspicious access patterns, and potential exploitation of databases by compromised identities or malicious insiders. Read Overview of Defender for Azure Cosmos DB to learn about its capabilities and detections.
Microsoft encourages you to develop a security strategy for your deployments in the cloud and protect Cosmos DB instances with the proposed detection solution.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1Early RBAC capabilities are also provided by a legacy authentication method based on resource token, but it is largely obsolete now.
READ MORE HERE