Detect active network reconnaissance with Microsoft Defender for Endpoint
The Microsoft Compromise Recovery Security Practice has observed how the security industry has evolved over the last few years as consumers, businesses, and industry professionals continue to adapt to the changing landscape. We have seen the emergence of new frameworks, such as the Cybersecurity Framework by the National Institute of Standards and Technology (NIST), which can empower us to build scalable programs and accelerate the transition to a Zero Trust workplace. We have also witnessed the rise and prominence of human-operated ransomware, which continues to subvert traditional security defenses and assert control over our information assets.1
Many of our customers have placed their trust in Microsoft Defender for Endpoint in order to help them protect, detect, and respond to threats that have emerged throughout this period of change. It is a diverse landscape that forces us to reconsider how we protect our most prized assets from borderless threat actors in IT environments that can no longer remain exclusively protected behind a network perimeter.
Threat actor tactics and techniques
With the current levels of diversity and the continued evolution of IT services, it is important to take a moment and consider how attackers might think in terms of the tactics and techniques required to successfully target and infiltrate a network. For example, HAFNIUM performed active reconnaissance before choosing to exploit a zero-day vulnerability within Microsoft Exchange Server to assert control over their chosen target’s information systems.

The objective was to develop a network map or diagram of possible endpoints which could be successfully exploited as part of a targeted campaign. This highlights the significance of reconnaissance and demonstrates the critical role it plays in assisting threat actors in achieving their goals and objectives, such as active directory domain dominance.
Spending quality time on reconnaissance is guaranteed to pay dividends at subsequent stages of the cybersecurity kill chain and is a crucial indicator from which to detect malicious activity at the earliest possible stages of an attack. Unfortunately, it is also a focus area that is overlooked by security professionals in favor of exotic phases of an attack such as weaponization, delivery, and exploitation. This is because it can be notoriously difficult to detect reconnaissance attacks—as they are often passive—executed in the public domain and external to the victim’s network. Job postings, domain registrars, and financial reporting are great resources to gain context on a target, but due to their nature, it can be a challenge to even seasoned security operations teams to detect and investigate this type of attack. Fortunately, there is a certain point where passive activities can have diminishing returns as the data points produced can be too broad to act upon. This can drive an attacker to consider the use of active reconnaissance which has dependencies on the endpoint or human interaction. For defenders, this is good news as it increases the likelihood that security services will be able to capture indicators of attack (IOA) in event logs, providing intelligence that can be analyzed and used to execute an informed response. For the remainder of the blog post, we will look more directly at active network reconnaissance using a well-known utility.
Active network reconnaissance
Active network reconnaissance is an art form and a somewhat divisive topic. A typical approach is to perform network scanning against a network address range or host IP address to elicit information about the target under evaluation. A wide variety of utilities can scan and enumerate data from a network, but for many Nmap (Network Mapper) remains the premier choice in developing time-sensitive network intelligence. Originally released 24 years ago, Nmap has been actively maintained and is available for Microsoft Windows, Linux, and macOS making it accessible to network auditors and security professionals regardless of their preferred choice of operating system.

At its heart, the utility enumerates critical information about the target. It does this by sending specially crafted network probes to elicit a response from a scanned host. These responses are analyzed and provide data points about the ports, services, and operating system versions which exist on the target under evaluation. This information is valuable to a threat actor, as it defines how to approach the weaponization, delivery, and exploitation phases of the attack lifecycle, providing insight into critical areas of interest, such as determining what types of vulnerabilities can be exploited to gain entry. Equally, this can be of significant interest to a defender as it can be used to identify weaknesses in the attack surface which require further investigation to protect—often considered a pivotal component of threat and vulnerability management programs. The utility can also quickly determine which hosts may be active at any given time, ensuring that deeper analysis is performed directly on responding endpoints.
Knowing which hosts are online facilitates this narrowing of reconnaissance investigation effort to specific endpoints where more time and care can be taken to determine the most effective path to exploitation. Gaining intelligence on which hosts are online enables the development of a structured attack strategy, which significantly increases the chance of success and ensures energy is concentrated exclusively on these endpoints—leading to interesting information about their status and configuration. Let’s illustrate this in a real-world scan using Nmap in a controlled environment.
Nmap scan use case
In our lab environment, Nmap has been configured to send probes to an individual IP address from an unauthenticated client. The results, albeit constrained to a specific scan type, return a plethora of information that can aid an attacker in building a profile about a discovered host. An example scan can be seen in the screenshot below, which includes data points on:
- The online status of a scanned endpoint.
- The role or services, which are found to be running on the endpoint.
- The possible version of the operating system installed on the endpoint.

This type of information is vital as it will help to steer an attacker towards further research on the specific vulnerabilities which can be exploited to successfully compromise the version of the operating system or combination of windows services running on the scanned endpoint.
The valuable point to take away is that whilst this information is of interest to a threat actor, the scan has a dependence on endpoint interaction which can leave behind breadcrumbs within security services such as Windows Defender Firewall with Advanced Security which can be reviewed for anomalous network traffic.
Defend against active network reconnaissance with Windows Defender Firewall
Windows Defender Firewall with Advanced Security is a service that is built directly into Windows and, given its proximity to the host, can detect active network reconnaissance attacks against an active network interface in real-time. Unfortunately for Microsoft’s Compromise Security Recovery Practice, the service is often found to be in a disabled state because of perceived complexity or operational overhead, but it is a proven solution that is effective in both the detection and prevention of active reconnaissance attacks and should not be overlooked as part of any defense-in-depth security strategy.
Returning to our lab, NMAP had been used to target an endpoint where the Windows Defender Firewall with Advanced Security service was active allowing for the capture of network events within localized log files. This file can be parsed to identify anomalies in network communications such as those of a singular IP being linked to a port scan against numerous TCP ports in a short time span. The Windows Defender Firewall with Advanced Security logfile confirms that the scan came from a host that is resident on the same network segment as the target endpoint.

This is important as whilst enterprise firewalls provide visibility of threats at the outermost boundary of a company network environment, they are not always positioned to detect threats within the same network segment. In this case, it is possible that security operations will not be able to identify and act upon these types of threats. By ensuring that Defender for Endpoint with Advanced Security is enabled and capable of collecting network security events, you will be able to perform effective host-based investigations, confirm the presence of active network reconnaissance, and take appropriate action to disrupt an attack at the start of the kill chain.
Enterprise-wide visibility with Microsoft Defender for Endpoint
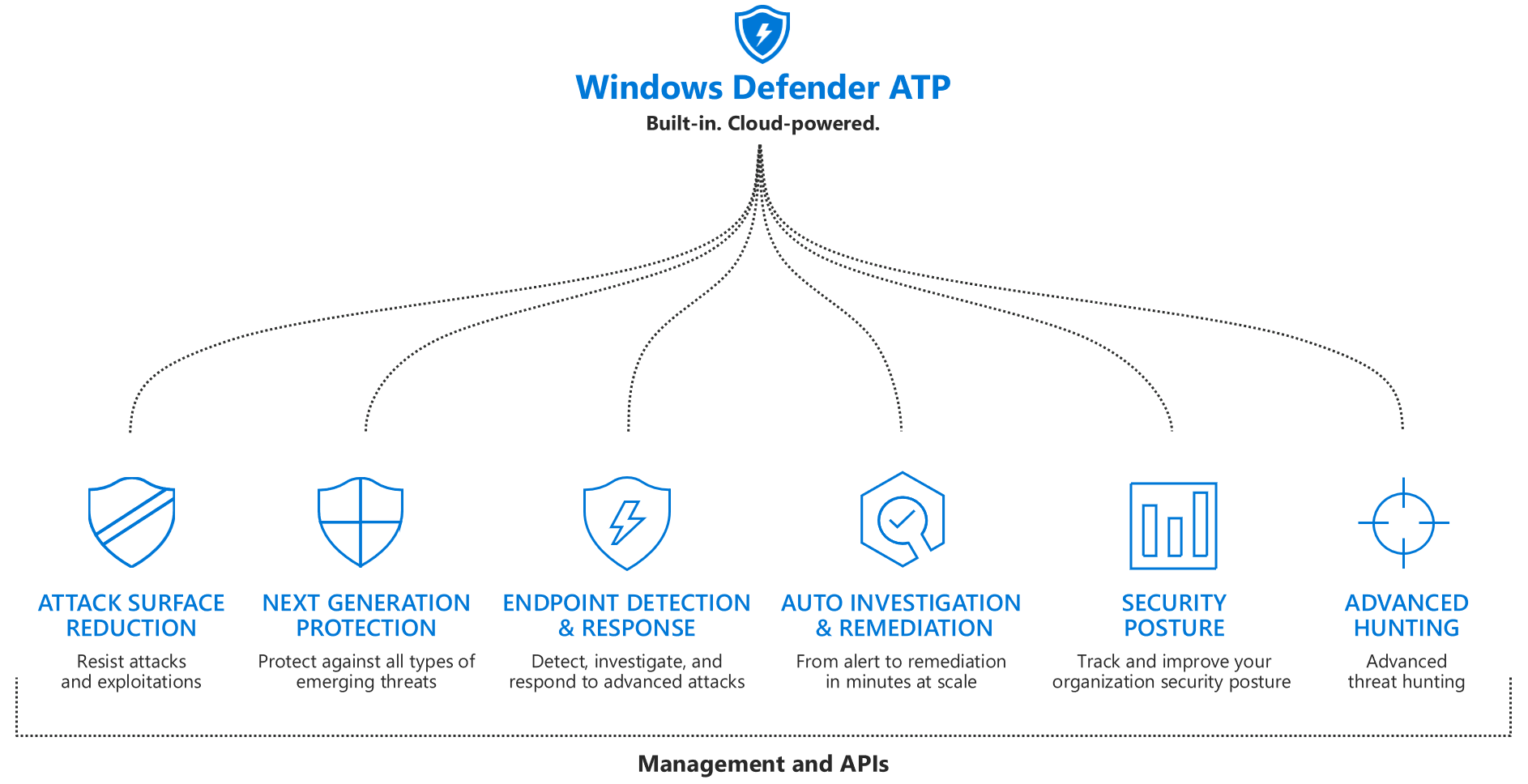
Microsoft Defender for Endpoint is a market-leading platform on the market that offers vulnerability management, endpoint protection, endpoint detection and response (EDR), and mobile threat defense service. It is a true game-changer in the security services industry and one that provides visibility in a uniform and centralized reporting platform. Defender for Endpoint can be quickly scaled on-demand across heterogeneous network environments and to begin collating telemetry data directly from managed endpoints for true enterprise-wide visibility.
While we had highlighted the value of parsing Windows Defender Firewall with Advanced Security log files on an endpoint, the approach provides a somewhat limited view of the overall threat landscape. Microsoft Defender for Endpoint can overcome these constraints as it continuously collects a wide variety of telemetry data from all managed endpoints. A security operations analyst can use this telemetry data to create detailed custom reports which can scale across the enterprise, empowering the team to perform rapid and effective isolation of malicious hosts in the network.
Advanced threat hunting with Defender for Endpoint
The Microsoft Defender for Endpoint advanced threat hunting feature can be used to detect network reconnaissance by searching for common characteristics of a scan such as those of time, source address, destination address, TCP/IP port, and network type. For example, we can check whether a single IP address is attempting to connect to a wide range of ports on a specific host in a short period of time in much the same way as found within Windows Defender Firewall with Advanced Security—except we now have enterprise-wide coverage within an instant. It is an extremely flexible solution that can be tailored to support almost any use case.
If we look closely at the results, we can see that an endpoint is attempting to connect to endpoints on TCP/IP ports which are representative of a default Nmap scan. This type of detection method is useful when the attacker is using a workstation that is not managed within Microsoft Defender for Endpoint but resident on the network.

In a situation where all hosts have been onboarded into Defender for Endpoint, you could detect the same threat using an alternative method such as running an advanced threat hunting query to detect all instances where the Nmap process has been invoked from the command line. In our example, the query references the DeviceProcessEvents table to generate a tabular report which can detect the invocation of nmap.exe from a parent process such as cmd.exe. The core value is that you customize advanced threat hunting queries within Defender for Endpoint to fit your threat scenario, truly ensuring that no stone is left unturned during your investigations.
As shown, the results table provides us with clear attribution towards suspicious endpoints without the need to drill down into the data to filter out legitimate versus malicious network traffic. The information provided accurately illustrates what type of scan <-sS, -T4> has been executed but provides a clear indicator of the targets of the attack such as the 172.16.0.0/24 subnet. This level of detail can be critical when looking to make an informed decision on how best to isolate, eradicate and recover from this type of attack scenario.

The results table provides us with clear attribution towards a suspicious endpoint which minimizes the need for further analysis. The information provided accurately illustrates what type of scan <-sS, -T4> has been executed by the suspicious workstation but also helps us concentrate our investigation on exposed targets of the attack <172.16.0.0/24>. This level of detail can be critical when looking to make an informed decision on how best to respond to the attack.

As shown in our lab examples, advanced threat hunting is a versatile and effective means to quickly detect active network reconnaissance attacks such as those performed using Nmap, and a great focus area to develop and mature your security operations capabilities. The queries can be tailored for almost any use case and can help us investigate an issue from multiple perspectives, allowing for a custom-specific target response to an attack. Defender for Endpoint includes a great number of useful queries to help you get started in the built-in repository but many more can be sourced from online communities or public repositories such as those from GitHub. These can act as great references that can help you to accelerate your development of the native Kusto Query Language (KQL) and are a fantastic point from which to start your journey in being able to detect and respond to advanced persistent threats.
Proactively seek out active reconnaissance
Back in 2020, it was reported that it can take up to 228 days to identify a breach. This is an incredible time period and one we all must aim to reduce to an absolute minimum to ensure the threat is contained at the earliest possible stages of the kill chain. Security operations teams must consider this when aiming to improve their operational performance along with adopting an assume breach mindset. To minimize the time-to-detect, one must place a greater emphasis on the detection of reconnaissance attacks through the adoption and use of continuous monitoring solutions like Defender for Endpoint. This means taking the initiative to proactively seek out active reconnaissance in all its forms, on the broadest possible scale, with the best tools available. It is, therefore, imperative to enable key log sources, like those found within Windows Defender Firewall to gain greater visibility into localized IOA for deep analysis while embracing Defender for Endpoint to scale on-demand and secure a complete horizontal view of the threats to your managed environment.
Microsoft Compromise Recovery Security Practice uses Defender for Endpoint every day as a part of our proactive and reactive investigations. It has proven to be critical to the fast and successful recovery of service for our customers and a significant contributor to our goal to assist our customers in accelerating transformation programs and achieving the desired target of a secure modern workplace.

Through this experience, we encourage our customers to act first, act fast, and prevent an attack at the earliest possible phases of the kill chain.
We believe that Microsoft Defender For Endpoint is a great place to start and one which could prove to be the difference between disrupting an attacker from performing active network reconnaissance and being the victim of a malicious zero-day targeted attack.
Learn more
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1 Human-operated ransomware, January 11, 2022
READ MORE HERE