Cyber-Attacks: How to Stop a Multibillion-Dollar Problem

By Ed Cabrera, Chief Cybersecurity Officer for Trend Micro and Martin Bally, Vice President & Chief Security Officer for Diebold Nixdorf
Where there’s money, there has always been crime. Traditional bank robbery and physical assaults on ATMs are still a challenge, and now a new breed of cyber-enabled theft—using ATMs as the endpoint for cash-outs— has become a multibillion-dollar problem. One recent raid saw $13.5m stolen from India’s Cosmos Bank. Although the FBI issued a warning about an impending “ATM cash-out” operation, it was too late; the bank was attacked just one day after the warning. So what can financial institutions do about a decade-long threat showing no signs of abating?
Cashing in on cash-outs
The FBI claimed that ATM cash-outs are often targeted against smaller banks which might not have the same budget to spend on cybersecurity as their larger counterparts. In the case of the Cosmos attack, and in Carbanak and Anunak cyberattacks, international gangs phish their way into back-end systems, exploiting network access to install malware that removes fraud controls such as maximum withdrawal amounts, transfer funds to other banks and increases customer balances. Dispersed gangs of mules then use cloned magstripe cards to withdraw the funds. In other cyber-attacks, such as ATM jackpotting, the software of the ATM itself is altered. The variety of approaches used by cyber-criminals reinforces the necessity of building a holistic, layered approach to security, which is inclusive of both the endpoint (ATM) and a bank’s entire internal software stack.
In the end, the FBI’s warning did nothing to help Pune-headquartered Cosmos Bank, as accomplices withdrew millions from ATMs in 28 countries around the world. It claimed the perpetrators had even managed to bypass internal transaction approval systems to enable the attack. But this was certainly not the first such cyber-attack: in 2013, cyber-criminals stole $45m from ATMs, and in 2016 over $12m was taken from cashpoints in Japan using cards cloned from a South African bank. That’s not to mention the activity of the infamous Carbanak gang, said to have been responsible for as much as $1bn in theft from banks around the world, using different attack methods also including the ATM as the cash-out point.
From physical to network-based attacks
These advanced network attacks differ from traditional ATM attacks which aim to either empty an ATM’s cash cassettes into the hands of waiting mules (jackpotting), or skim card details virtually or physically for later use or sale on the dark web. This meant installing secret cameras, card reader slots and PIN overlay pads to record/’skim’ lucrative card information, or opening up the ATM case to install malware manually via USB or CD-ROM. That malware is designed to send commands to the ATM via its XFS middleware, to dispense cash — the whole process perhaps taking as little as 10 minutes. Malware families such as Skimer, GreenDispenser, Ploutus, and Alice illustrate the continued popularity of onsite malware attacks.
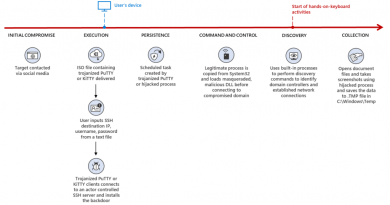
However, back in 2016 Trend Micro and Europol documented another category of attacks gaining in popularity, leveraging the network as the entry point. Although these require a greater investment of time and resources up front, they’re less likely to raise suspicion as there’s no interference with the physical ATM itself. Instead, hackers infiltrate the bank’s network via malware-laden phishing emails, steal admin credentials and move laterally inside until they gain remote access to the ATMs. Multiple machines can be commanded to issue cash at the same time and some malware can even delete itself, making forensics harder. Ripper malware was the first of its kind spotted in these kind of network attacks.
Protecting your ATM network
ATM attacks continue to reap financial rewards for their perpetrators, which means we should not expect them to let up. In fact, the U.S. saw its first jackpotting attacks this year, and the FBI said of ATM cash-outs that it “expects the ubiquity of this activity to continue or possibly increase in the near future.”
Skimming alone is thought to be a $2bn+ industry-wide problem. Over the years, criminals have made skimmers smaller, smarter and virtually undetectable. And even as EMV compliance makes its way across the U.S. and around the globe, skimming remains one of the financial industry’s most costly problems.
So what can financial institutions do to protect funds and cardholder data? ATM attackers take advantage of many classic security lapses, such as credulous end users, lax password control, poor network segmentation and unpatched systems. A best practice approach should therefore include:
Regular updates to underlying OS and relevant software (eg. XFS).
Physical security for ATMs including tamper alarms on high risk machines; 2FA access control for technicians; regular service checks; anti-skimming modules.
Intrusion prevention and hard disk encryption to protect ATMs during operation.
Improved user education in how to spot phishing emails.
Network segmentation to make lateral movement harder inside the bank network.
Application control/whitelisting to further reduce risk of malware infection.
Continuous network monitoring to raise the alarm if there is a network intrusion.
As long as there is money to be had behind that metal casing, criminal gangs will always be looking for innovative ways to get to it. To stop them cashing in by cashing out at the ATM, we need to understand the risks and take time to plug in multi-layered defenses.
To find out more, read our report, co-authored with Europol: Cashing in on ATM Malware.
Read More HERE