Cisco fortifies and simplifies its security portfolio with eye toward cloud, zero trust

Simplifying security options for enterprise customers is a daunting task, and it can be even harder in the current pandemic-driven workforce environment. But Cisco is taking steps to both streamline and bolster its security menu, according to news out of its virtual Partner Summit conference.
For starters, Cisco is eliminating 50 product names and simplifying its offerings within the renamed Cisco Secure portfolio. Cisco is also reinforcing its key platforms, including its SecureX and zero trust packages. (See related story, Cisco software upgrades to simplify hybrid-cloud management, operations)
“As we move to the next normal, we see an acceleration in new ways of working that require organizations to evolve their cybersecurity approach so people can securely connect from anywhere, anytime, and on any device,” said Gee Rittenhouse, SVP and GM of Cisco’s Security Business Group.
Cisco pointed to its own recent research about the security impact of COVID-19: 61% of respondents worldwide stated that their organizations experienced a jump of 25% or more in cyber threats or alerts since the start of the pandemic as malicious actors tried to exploit potential security gaps and more users accessed the corporate network and cloud applications remotely.
“Secure access, defined as the ability to securely enable access to the enterprise network and applications for any user, from any device, at any time, is the top cybersecurity challenge faced by the largest proportion of organizations (62%) when supporting remote workers,” Cisco stated in its report. “Other concerns raised by organizations globally include data privacy (55%), which has implications for the overall security posture, and maintaining control and enforcing policies (50%).”
Cisco is adjusting its security portfolio to address remote security changes and needs.
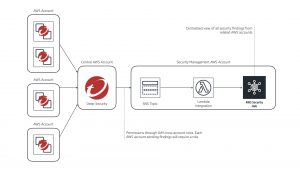
For example, at the virtual event this week, it upgraded its Cisco SecureX platform. The platform, which has some 11,000 customers since its June launch, is an open, cloud-native system that integrates Cisco security wares and third-party tools to let IT security teams automate security management across enterprise cloud, network, applications and end points from a single interface.
Cisco has added the ability for customers to use pre-built or customizable workflows to automate routine security tasks. Customers can use existing workflows aligned to common use cases, or build custom workflows with a drag-and-drop interface that requires no special skills to use, according to Cisco.
A new SecureX interface called SecureX ribbon is designed to improve security, networking, and IT group collaboration.
“The ribbon allows for the saving and sharing of information across teams and tools, and stays with you when you pivot to other applications to maintain context around certain events,” Cisco stated. “It provides a single location for various team members to get answers and take actions without having to continuously switch back and forth between consoles.”
Cisco has also engineered tighter integration between SecureX and its Secure Cloud Analytics program so that SecOps teams can monitor for behavior that may be indicative of threats or misconfigurations in the cloud. “They can then easily share this information with DevOps, the group ultimately responsible for addressing gaps in cloud security,” Cisco stated. “These new features are designed to encourage more transparency to help safeguard sensitive workloads in the public cloud.”
Like other companies such as VMware, Cisco says it will extend SecureX to include support for Extended Detection and Response (XDR), which offers a unified approach to security incident detection and response that can let customers correlate threat intelligence and signals across multiple security offerings.
Research firm Enterprise Strategy Group (ESG) says XDR is “an integrated suite of security products spanning hybrid IT architectures, designed to interoperate and coordinate on threat prevention, detection and response. XDR unifies control points, security telemetry, analytics, and operations into one enterprise system.”
In the zero-trust realm, Cisco has released the 3.0 version of its Identity Services Engine (ISE), which is the company’s security policy management system that lets customers control and see users and devices across wired, wireless, and VPN connections to the corporate network.
The new release of ISE includes support for agentless implementations to ensure all devices are identified, and remain in compliance, without having to install anything on the device or endpoint, Cisco stated. The new version also lets customers identify a variety of IoT endpoints to enforce consistent policies from the cloud, according to Cisco.
Another component of Cisco’s zero-trust offerings, Duo, has been upgraded to include a Trust Monitor that uses machine learning to detect suspicious logins and alerts security operations via API integrations with platforms such as SecureX.
Cisco bought Duo in 2018 for its zero-trust security model that authorizes secure connections to all applications based on the trustworthiness of users and devices. Duo’s cloud-delivered technology lets IT professionals set and enforce risk-based, adaptive access policies and get enhanced visibility into users’ devices and activities.
Zero-trust initiatives are growing in response to the pandemic, experts say.
COVID-19 has prompted 60% of enterprises to accelerate their zero-trust networking strategies, according to Shamus McGillicuddy, vice president of research networking at Enterprise Management Associates. (See related story: Zero trust benefits remote work during pandemic)
Zero trust typically has a dynamic policy engine that evaluates the legitimacy of network communications even inside the network perimeter. Changes in location, device state, security state, behavior, as well as other factors can initiate a reauthentication process, McGillicuddy stated. Zero trust network-access solutions can scale and secure network connections for people who are working from home. Zero trust segmentation can also granularly control what information assets remote users can access when they connect to the network, according to McGillicuddy.
READ MORE HERE