Business email compromise campaign targets wide range of orgs with gift card scam
Cybercriminals continue to target businesses to trick recipients into approving payments, transferring funds, or, in this case, purchasing gift cards. This kind of email attack is called business email compromise (BEC)—a damaging form of phishing designed to gain access to critical business information or extract money through email-based fraud.
In this blog, we want to share our investigation of a BEC campaign that used attacker-created email infrastructure to facilitate gift card theft. In this campaign, we found that attackers targeted organizations in the consumer goods, process manufacturing and agriculture, real estate, discrete manufacturing, and professional services sectors using typo-squatted domains to make the emails appear as if they were originating from valid senders.
BEC emails are intentionally designed to look like ordinary emails, appearing to come from someone the targeted recipient already knows, but these campaigns are more complex than they appear. They require behind-the-scenes operations, preparation, and staging. Advanced email solutions like Microsoft Defender for Office 365 detect and block these elusive threats. Defender for Office 365 safeguards organizations against the threat posed by emails and URLs associated with BEC campaigns.
In our blog titled Business email compromise: How Microsoft is combating this costly threat, we wrote about the process of orchestrating BEC attacks and discussed Microsoft strategies to combat these threats. Additionally, Microsoft released a three-part blog series on BEC scams titled Business Email: Uncompromised, which offers an in-depth look into the evolution of BEC attacks and how Microsoft Defender for Office 365 employs multiple native capabilities to help customers defend against them.
Understanding the BEC gift card scam
Imagine this work-from-home scenario for an executive assistant (EA):
It’s a typical day at work for you as a remote EA. You prepare your to-do list for the day and check your CEO’s calendar for their scheduled meetings, all while communicating with other EAs via email and chat. You categorize your emails and prioritize your tasks—nothing out of the ordinary.
In the middle of the workday, you get an email appearing to come from your boss, requesting that you purchase gift cards to give to the team as an incentive for their hard work during the pandemic.
The request seems a little strange, you think. Maybe it was a spur-of-the-moment initiative. But you’re a rock star assistant and decide to go ahead and purchase the gift cards using department funds.
You reply to your boss’s email with the gift card codes. After a while of not hearing back, you finally ping them on chat to make sure they received them. Your boss expresses their confusion in response to your chat message–they never requested gift cards for the team.
This is a classic business email compromise (BEC) scenario.
Defining BEC attacks
BEC is a type of phishing attack that targets organizations, with the goal of stealing money or critical information. Our blog post Business Email: Uncompromised – Part One provides examples of real-world BEC attacks and how to identify key visual cues for spotting attacks.
The emails used in BEC attacks appear simple, but there is a wide level of complexity behind them—from reconnaissance and targeting, social engineering, to the delivery infrastructure.
If you’re wondering why these complex threats are crafted for a seemingly insignificant payout, think again. BEC continuously poses a serious area of concern, with attacks totaling approximately $1.8 billion in victim losses in 2020, according to the FBI’s Internet Crime Compliant Center (IC3). While attacks similar to the BEC gift card scenario we described earlier can add up to a hefty sum, many BEC attackers are known to target significantly larger transactions, such as intercepting and redirecting wire transfers, ultimately making BEC scams a highly profitable cybercriminal operation.
Conducting reconnaissance, social engineering for BEC attacks
For BEC actors to know who to target and who to impersonate, they frequently conduct reconnaissance prior to launching attacks. Social media sites, “about us” pages on a company’s website, or news articles about a targeted company may all give actors the information they need to craft a specific, believable message intended for a chosen victim. In our blog post, Business Email: Uncompromised – Part Two, we discuss the multiple stages of a BEC attack, from identifying target organizations to the attackers setting up transaction details.
BEC gift card campaign seen targeting various organizations
In this campaign, attackers targeted a variety of companies in the consumer goods, process manufacturing and agriculture, real estate, discrete manufacturing, and professional services sectors.
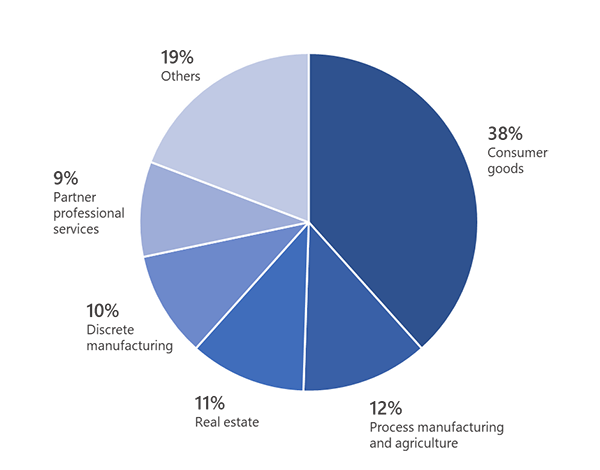
Figure 1. Breakdown of email volume sent to the top targeted industries we observed in this BEC campaign
This specific campaign started with an extremely vague request, such as “I need you to do a task for me” or “Let me know if you’re available.” The message body contained a few details related to the target to make the email seem legitimate.
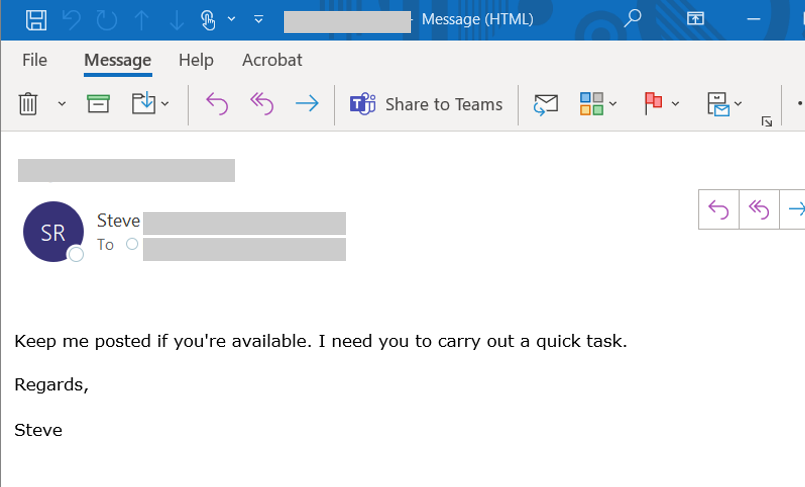
Figure 2. A sample BEC email impersonating an executive
In the Figure 2 screenshot, the attacker signed the email as “Steve,” which is the name of an executive at this targeted organization. Additionally, the email was addressed to someone who worked with the impersonated executive while the subject line contained the recipient’s first name.
If the recipient replied to the email, the attacker responded with a more specific demand for a gift card. In other cases, attackers skipped the generic email altogether and jumped directly to the gift card demand, using a method of generating fake replies to add legitimacy to the email. We discussed the anatomy of BEC attacks in this blog post and detailed telltale signs of common phishing techniques.
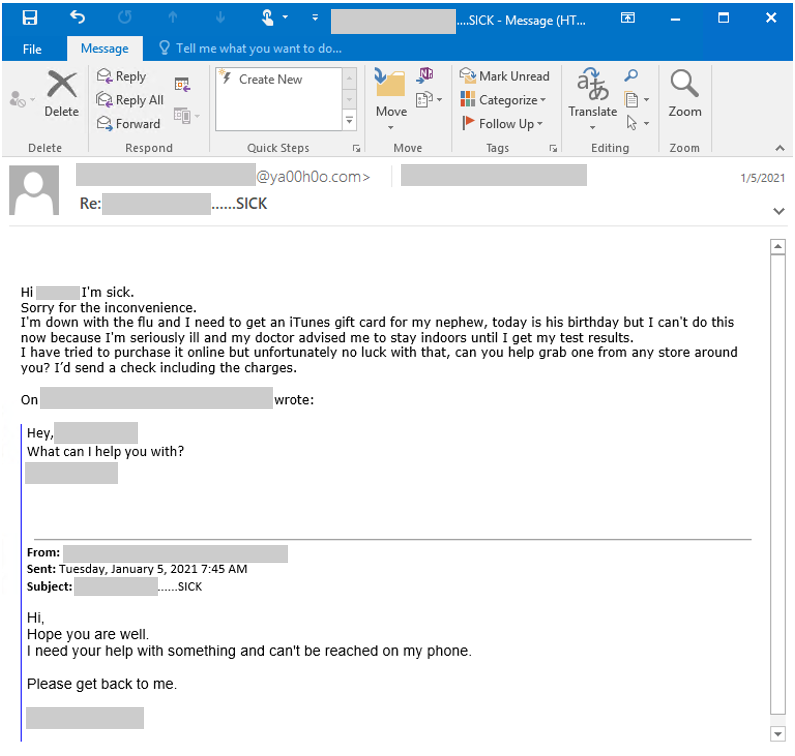
Figure 3. A sample BEC email targeting the education sector demanding a gift card purchase
In this case, the attacker pretended to be a teacher at a K-12 institution and claimed that they were unable to leave their house to buy a gift card. In addition, the email subject contained the name of the purported teacher followed by “SICK” in the subject line.
The email body included a message requesting the recipient to purchase a physical gift card for them. According to our past BEC research, attackers frequently used the stolen gift card codes for websites that allow them to redeem and convert gift cards to cryptocurrency or other foreign currencies. The funds generated from cashing out gift cards can then be transferred to attacker-owned accounts untraceably.
In this campaign, we noticed that the email also contained a fake reply, wherein the threat actor included what appeared to be an original message in the email body, with the subject line starting with “Re:”. The ‘From’ email address in the crafted original message used yahoo.com, but the ‘From address of the actual email was a typo-squatted domain spoofing yahoo.com, hinting that the email reply was indeed fake.
Figure 4. The attacker used a typo-squatted domain that spoofed a Yahoo account
Upon closer examination, the actors had taken the extra step of faking the In-Reply-To and References headers, which added an extra air of legitimacy to the email. An email’s In-Reply-To header contains the unique Message ID of the previous message in the reply thread, and the References header contains the unique Message IDs from all previous messages in the reply thread. In a typical email that is not a reply, these two header fields would be blank.
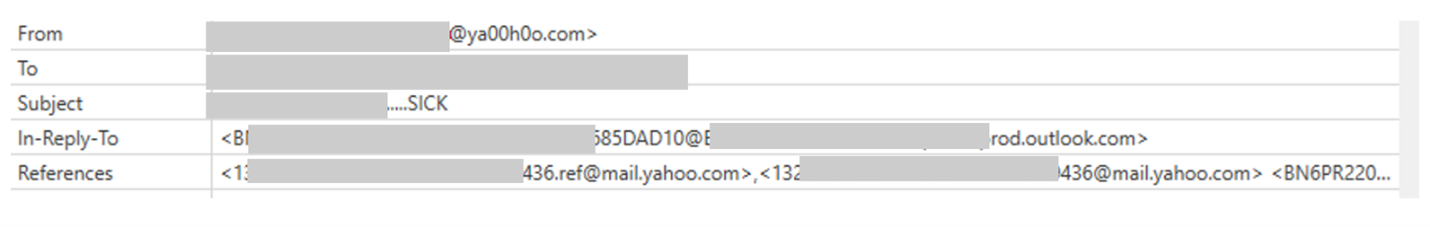
Figure 5. Spoofed fields for the In-Reply-To and References headers
As shown in Figure 5, both the In-Reply-To and References headers are populated with Message IDs associated with legitimate email providers, including yahoo.com, which this campaign spoofed. We can see that these headers were manually added by the attacker as made apparent by the ya00h0o.com sender. In addition, the email’s HTML contents show that the message was manually typed to appear as though it’s a reply.
Filling these headers in made the email appear legitimate and that the attacker was simply replying to the existing email thread between the Yahoo and Outlook user. This characteristic sets this campaign apart from most BEC campaigns, where attackers simply include a real or specially crafted fake email, adding the sender, recipient, and subject, in the new email body, making appear as though the new email was a reply to the previous email.
Delivery infrastructure
For this campaign, attackers registered typo-squatted domains for over 120 different organizations to impersonate actual businesses. We observed patterns in using the correct domain name but an incorrect TLD, or slightly spelling the company name wrong. These domains were registered just days before this email campaign began.
We noted that these domains did not have domain privacy enabled, nor were they under the EU’s GDPR protections. Each domain used a unique registrant name and email. The registrant names appeared to be autogenerated random first names and last names, and the registrant contact email used a free email service such as Gmail or mail.com with accounts that were often simply <first name>.<last name>@gmail.com or similar. Each name was used to register just one domain used in the campaign, which made pivoting to related domains more challenging.
Another observation about this campaign is that the registered domains did not always align with the organization being impersonated in the email. This could have been a mistake on the actor’s part, as BEC domains are typically designed to closely mimic the impersonated organization. For example, an actor may register microsoft.xyz or micrrosoft.com, both of which would normally be used to send emails pretending to originate from Microsoft. In this campaign, those types of homoglyphed and typo-squatted domains were used to send emails pretending to originate from a variety of organizations.
Our in-depth research into this campaign’s delivery infrastructure directly informed the protection Microsoft provides against this BEC threat.
How Microsoft security solutions combat BEC campaigns
Microsoft Defender for Office 365 defends organizations against malicious threats posed by this BEC campaign.
For a better understanding on how Defender for Office 365 protects against BEC attacks, you can refer to our blog post about detecting user and domain impersonation at scale in a fast-evolving attack landscape. Email authentication in Defender for Office 365 allows you to verify whether email messages from a sender are legitimate and come from expected sources for that email domain. Email standards like SPF, DKIM, and DMARC are evaluated by Office 365 to prevent domain spoofing. Our spoof intelligence technology uses advanced algorithms to observe the sending patterns of domains and flag anomalies.
You can strengthen your security posture further by empowering employees through user awareness tools in Defender for Office 365 that are integrated into products like Outlook and Office 365 apps. For instance, attack simulation training in Defender for Office 365 allows you to craft and run realistic BEC-like attack scenarios in your organization.
As these threats are always changing and evolving, Microsoft has dedicated research teams who constantly stay abreast of the changing threat landscape and combine that knowledge with our extensive customer telemetry data to stay current on BEC and other attacks.
Microsoft’s portfolio of security products processes trillions of signals every day. This signal base drives constant improvements to the artificial intelligence layers backing our protection and detection systems. Microsoft threat analysts leverage these signals to track actors, infrastructure, and techniques used in phishing and BEC attacks to ensure Defender for Office 365 stays ahead of current and future threats.
Defender for Office 365 equips security operations teams with automated threat investigation and response capabilities to understand, simulate, and prevent email-related threats. Defender for Office 365 enables you to define threat protection policies to set up the appropriate level of protection for your organization, while allowing you to view and monitor real-time reports. Learn more about Microsoft Defender for Office 365.
Microsoft 365 Defender Threat Intelligence Team
READ MORE HERE