BlueVoyant optimizes customer security with Microsoft security services
This blog post is part of the Microsoft Intelligent Security Association (MISA) guest blog series. Learn more about MISA.
What a year it has been.
The rapid and unexpected transition to work from home is one of the biggest issues affecting companies of all sizes and industries in 2020. As companies now take a brief pause after the mad rush during the first half of the year, they must take an honest look at their security posture to ensure that their intellectual property, employee and customer data, applications, and infrastructure are all being protected and that plans are in place to continue doing so in the future, given many companies will operate very differently going forward.
Security teams are facing challenges they have never experienced before
The exponential growth in remote users, combined with accelerated digital transformation efforts involving migration of applications and data to the cloud, has changed and expanded the attack surface for today’s organizations. Attacks and breaches have continued to be a danger to companies throughout the pandemic. Security teams are challenged to piece together solutions to detect and eradicate threats across multiple types of environments with solutions made up of technologies from multiple vendors, many of which were only designed to operate in legacy environments preceding the cloud era. Integration complexities, a lack of qualified security resources, and an unrelenting wave of attacks from cybercriminals make securing the organization a seemingly unattainable goal.
Today’s security reality is less than ideal in many cases
BlueVoyant speaks with a lot of companies about their security technology deployment. One of the main trends found is that they have accumulated a bunch of hardware and software over the years and are trying to make use of it somehow, but at the end of the day, they struggle to get it all to work together properly. Research has shown that this situation (commonly known as “tech sprawl”) can oftentimes result in a company being more exposed to attack than it realizes, as failing to correctly integrate various pieces of hardware and software can create gaps that allow cyber attackers to get in.
In addition to dealing with tech sprawl, IT and security teams are being asked to participate in digital transformation initiatives at their companies. These initiatives almost always involve moving large amounts of applications and data to the cloud to reap the benefits of lower infrastructure costs, greater flexibility, and on-demand scalability. Legacy security technologies simply don’t work in these new cloud environments.
How do you solve this problem?
What is the solution to eliminating the pain associated with tech sprawl while also providing the security your company needs in a cloud-first world? We believe that a cloud-native, fully integrated security solution is what companies need to operate safely in today’s dangerous cyber environment. To bring our vision to life, we are adopting Microsoft security technologies to build managed solutions that extend detection and threat eradication capabilities across a customer’s entire ecosystem, leveraging tools and integrations already included with a customer’s Microsoft 365 license. Our Managed Microsoft Security Services combine the design, deployment, 24x7x365 threat detection, and over 500 proprietary detection rules—designed and built on Microsoft-powered security technology—to provide the business and technology outcomes needed by our customers.
How does integrated Microsoft security technology work?
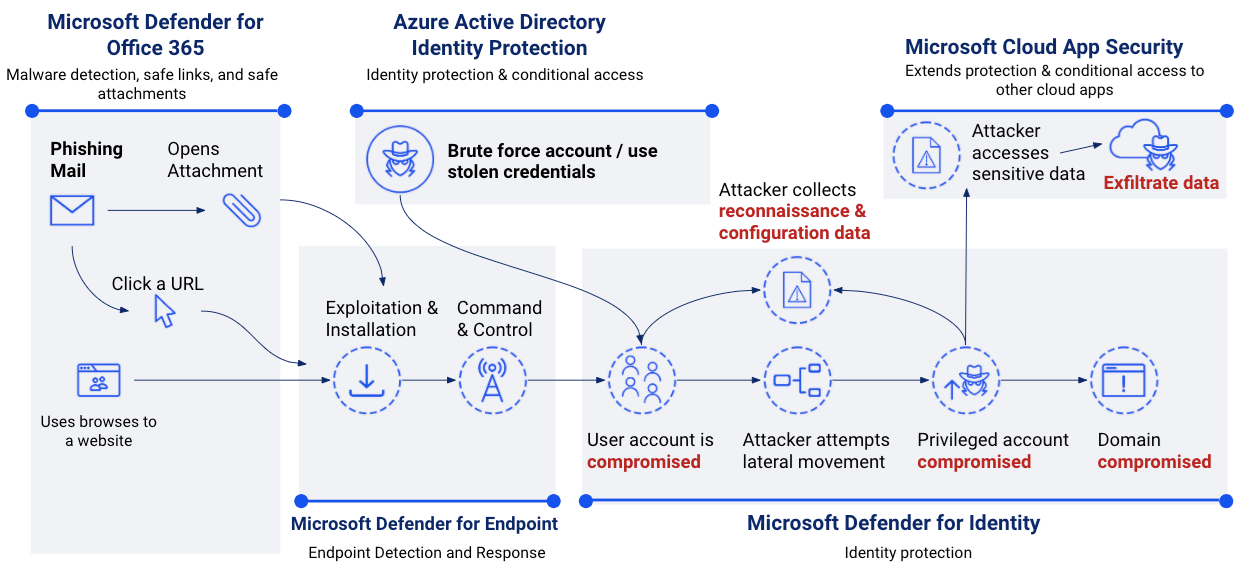
Here is an example of the integrated Microsoft security technology working together to successfully detect and eradicate a cyber threat:
- A phishing email is received by a user on a managed endpoint.
- Office 365 Security and Compliance Center provides visibility into the phishing attempt, and Defender for Office 365 Safe Links evaluates the link at the time-of-delivery to search for malicious or suspicious content. It finds nothing out of the ordinary and allows the message to be delivered to the user’s inbox. The end user opens the email and clicks the link. Defender for Office 365 again scans the link using Safe Links and finds a malicious file on the page that is linked. The user is presented with a webpage, warning them that the site may be malicious.
- Since the user believes the email came from someone they know, they bypass the warning message and visit the link where malware gets downloaded to their machine in the background, causing a compromise that allows for elevated access on the endpoint.
- Defender for Endpoint detects this and quarantines the file based on zero-day and runtime detections. It surfaces alerts that include insights into the threat and detailed information about events happening on the machine to the security team in the security operations center (SOC) dashboards.
- Azure Active Directory Identity Protection sends additional compromise/threat escalation data to Microsoft Cloud App Security. Threat aggregation is calculated against machine learning normalization to assess threat severity.
- Azure Sentinel conducts additional correlation analysis and follows a remediation playbook based on severity and aggregated threat calculation.
- Remediation workflows revoke the user’s multi-factor authentication (MFA) token, triggering unified endpoint management (UEM) device compliance failure to revoke access grants in Conditional Access.
- SOC analysts and end user compute staff confirm remediations before restoring access.
Who is BlueVoyant
BlueVoyant was co-founded in 2017 and is led by several former Fortune 500 executives and government intelligence leaders. We recruit and retain top talent from the FBI, NSA, Unit 8200, GCHQ, and from leading private sector security firms. While we’re still a young company, our expertise in delivering Managed Microsoft Security Services to our customers is already well established. For example, in the recent “Forrester Wave: Midsize Managed Security Services Providers, Q3 2020” report, we were the only company highlighted for our experience in working with Azure Sentinel.
In addition to the existing portfolio of security services we offer today, we are always on the lookout for new ways to provide increased value to our customers who prefer Microsoft-powered security services. We are excited to announce that we acquired Managed Sentinel, a company specializing in Azure Sentinel and Microsoft 365 Defender deployments. By acquiring Managed Sentinel, BlueVoyant strengthens its ability to serve Microsoft customers globally. This allows Managed Sentinel to leverage BlueVoyant’s threat intelligence and managed detection and response (MDR) capabilities, enabling both BlueVoyant and Managed Sentinel to deliver full-service offerings for Microsoft security technologies from customized deployments, ongoing maintenance, to 24/7 security operations.
According to Mandana Javaheri, Director of Business Strategy, CSG Business Development, Microsoft, “The Managed Sentinel acquisition by BlueVoyant further expands their cybersecurity services capabilities to provide customers the consultative, advisory, and implementation expertise needed to fully maximize the value and adoption of Microsoft’s security product portfolio.”
BlueVoyant is an MSSP pilot member of the Microsoft Intelligent Security Association. For more information about our extensive consulting portfolio, implementation, and managed security services, please visit our website.
Learn more
To learn more about the Microsoft Intelligent Security Association (MISA), visit our website, where you can learn about the MISA program, product integrations and find MISA members. Visit the video playlist to learn about the strength of member integrations with Microsoft products.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE