Behavioral blocking and containment: Transforming optics into protection
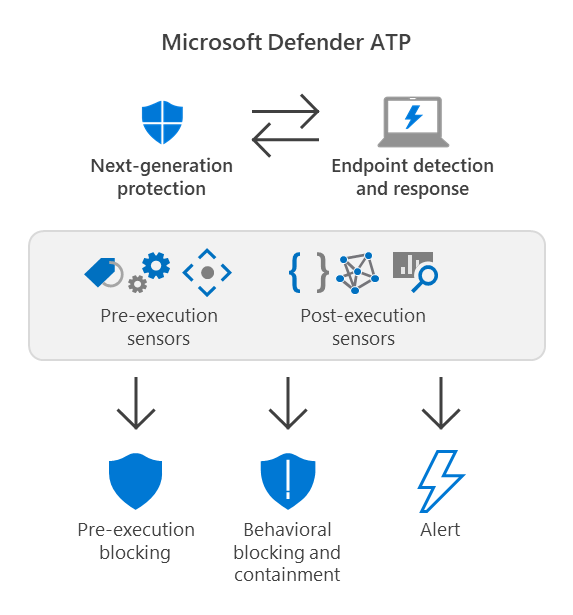
In today’s threat landscape—overrun by fileless malware that live off the land, highly polymorphic threats that mutate faster than traditional solutions can keep up with, human-operated attacks that adapt to what adversaries find on compromised machines, and other sophisticated threats—behavioral blocking and containment capabilities are a critical component of the unified endpoint protection delivered by Microsoft Defender Advanced Threat Protection (Microsoft Defender ATP).
Behavioral blocking and containment capabilities leverage multiple Microsoft Defender ATP components and features to immediately stop attacks before they can progress. For example, next-generation protection uses engines that specialize in detecting threats by analyzing behavior, stopping threats after they have started running.
In continuing to diminish the chances of sophisticated threats slipping through defenses, we have expanded behavioral blocking and containment capabilities to get even broader visibility into malicious behavior by using a rapid protection loop engine that leverages endpoint and detection response (EDR) sensors.
Microsoft Defender ATP’s EDR is informed by massive amounts of security signals on network, endpoint, and kernel behavior. As a component of Microsoft Threat Protection, Microsoft Defender ATP also has optics on other surfaces, including identities, email and data, and apps. Microsoft Defender ATP processes and correlates these signals to raise detection alerts that empower security operations (SecOps) teams to respond to attacks. Notably, unlike traditional behavior monitoring components on a device that provides discrete signals from that device, the aggregation of threat intelligence sources provides Microsoft Defender ATP with continuous signals on events that span across machines and surfaces.
With expanded behavioral blocking and containment capabilities, even more threats could be prevented, or blocked if they somehow manage to start running. In this blog, we’ll share several case studies of real-world attacks stopped by behavior-based blocking and containment capabilities informed by EDR alerts.
Stopping the spread of new malware in an organization and beyond
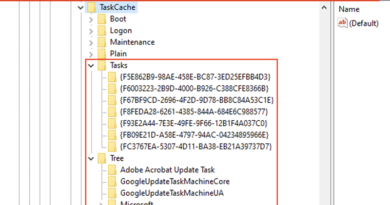
When Microsoft Defender ATP raises an alert on an observed suspicious behavior, information about the process, associated file, process tree, and various such signals that span across devices are sent to multiple classifiers. The rapid protection loop engine inspects and correlates the info with other signals to arrive at a decision whether to block a file.
This results in the rapid blocking of confirmed malware on a machine where EDR capabilities detected suspicious behaviors. This decision is then used to drive protection across the entire ecosystem through rapid blocking and containment. Such a detection could stop an attack on the machine, on other machines in the organization, and other organizations as an attack attempts to broaden its foothold.
For example, on January 10, 2020, Microsoft Defender ATP detected a privilege escalation activity on a machine in a certain organization and raised the alert “Possible privilege escalation using NTLM relay”.
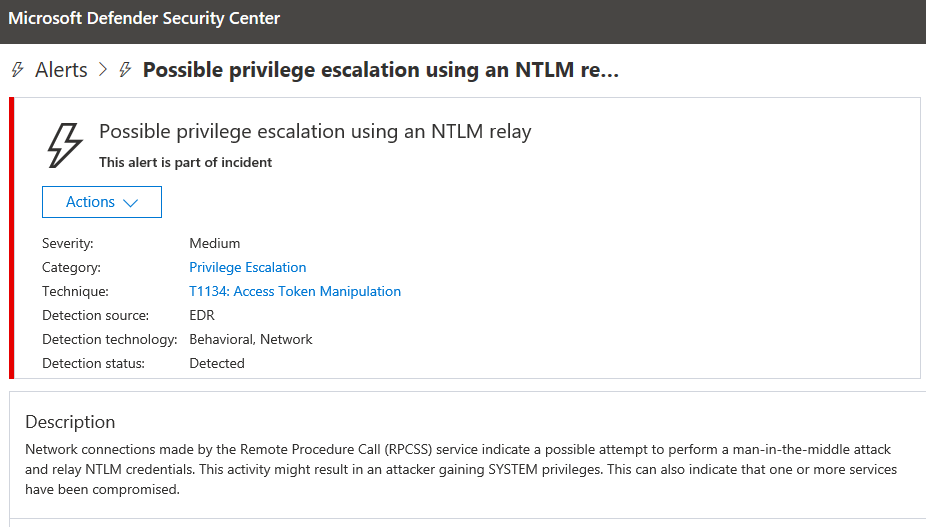
The malware is a new, first-seen variant of the notorious hacking tool Juicy Potato, which attackers use for privilege escalation, a critical step in attacks.
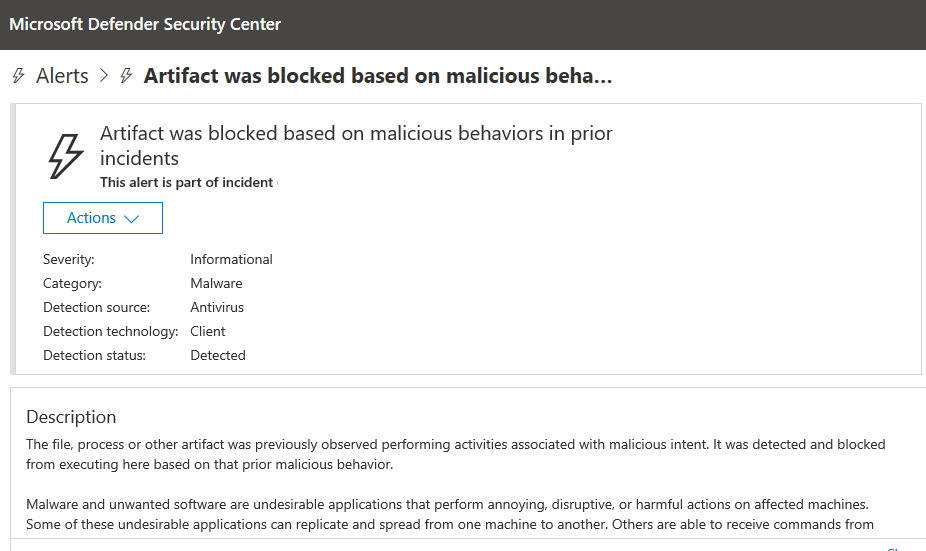
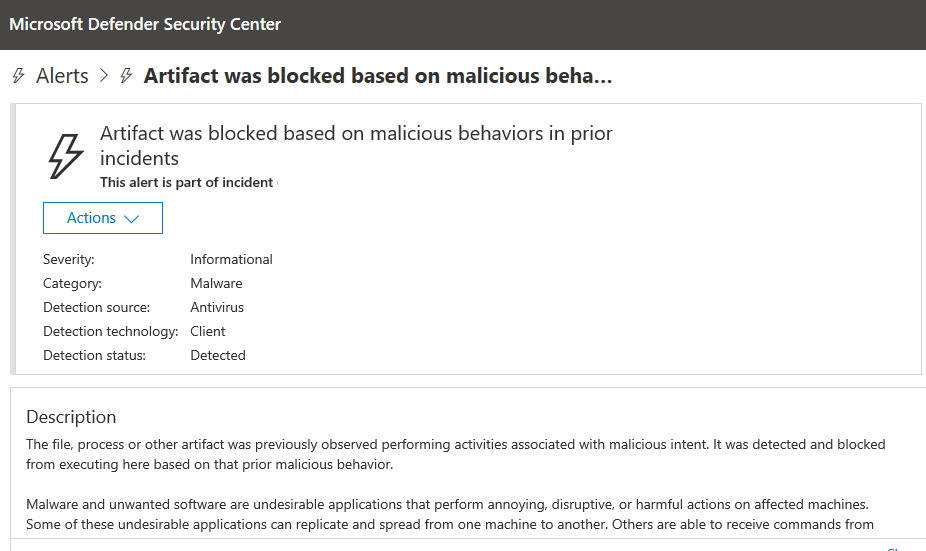
In a matter of a few minutes, using information from the alert, the rapid protection loop engine’s classifiers automatically analyzed the file that exhibited the behavior (SHA-256: ec00ffadffb20954b3809e61d01a965ab1210ce10b5f4b7431bb2a458e31686f) and confirmed it was malicious, stopping and blocking the process. The malware was detected as EUS:Win32/Graphez!cl, and the alert “Artifact was blocked based on malicious behavior in prior incidents” was raised in Microsoft Defender Security Center.
In the next few minutes, multiple instances of the same file were blocked on the same machine, indicating multiple attempts by attackers or another malware to deploy the file on the machine. With behavioral blocking and containment capabilities, not only do SecOps get alerted on compromise attempts; Microsoft Defender ATP also automatically contains the incident while the SecOps performs a thorough investigation to understand and remediate the root cause.
Adding to multiple layers of protection
A defense in depth strategy requires multiple layers of protection. Multiple security components inspect Microsoft Defender ATP alerts for various actions. Auto-investigation and response capabilities kick in to automatically remediate threats. Cloud-based machine learning models in next-generation protection engines also run multiple classifiers to determine whether a file is confirmed malicious and should be blocked. The expanded behavioral blocking and containment adds another layer of protection that helps ensure there are multiple points at which an attack can be stopped.
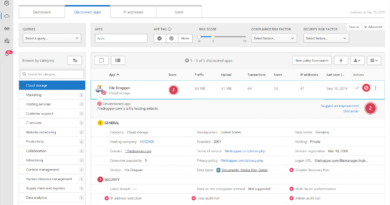
On January 13, a file named DowloadX.exe (SHA-256: 971bc7eb2be734262a573ca7dc086c334f3a40ae874af90e7f380ec1a6221d7c) triggered the Microsoft Defender ATP alert “A suspicious file was observed” on a machine in one organization. The file was attempting to connect to certain domains to download files.
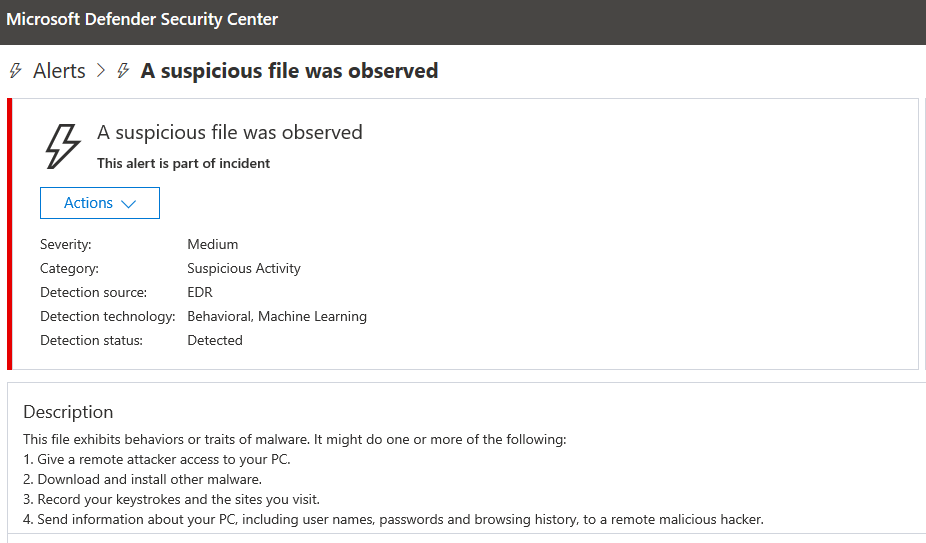
The file is a downloader Trojan used in a widespread campaign that aimed to deploy various malware payloads, including information stealers, cryptocurrency miners, and ransomware.
Within a few moments of observing the file, machine learning models operating on the EDR data, which come with richer granular details, determined the file to be malware, raised an alert, and provided feedback to the rapid protection loop engine. This insight led to the immediate blocking of the file on subsequent machines.
As the campaign progressed, the file was blocked on thousands of machines that same day, with multiple Microsoft Defender ATP technologies providing several layers of protection. By detecting and stopping the downloader using multiple detection technologies, Microsoft Defender ATP protected thousands of machines from more dangerous malware payloads.
Amplifying Microsoft Threat Protection
Through Microsoft Threat Protection, behavioral blocking and containment and other solutions that are informed by Microsoft Defender ATP’s EDR alerts also benefit from the signal-sharing across Microsoft security services. This broadens defense in depth even further, demonstrating how signals from multiple points in the attack chain allow Microsoft Threat Protection to deliver unparalleled comprehensive protection.
For example, on January 14, 2019, Microsoft Defender ATP’s EDR raised an alert on a new malicious Java Archive (JAR) file (SHA-256: 0d646ac10665f629adde73f1e3bb1afcc69e12a6f286d516c579c6ce0b22e892) based on information from Office 365 ATP. The alert, “A malicious file was detected based on indication provided by Office 365”, means that the malware had previously been observed and blocked in an organization protected by Office 365 ATP. Using information from Office 365 ATP, Microsoft Defender ATP EDR instantly raised an alert when it encountered the file in other organizations, while cloud-based protections blocked the file in these organizations.
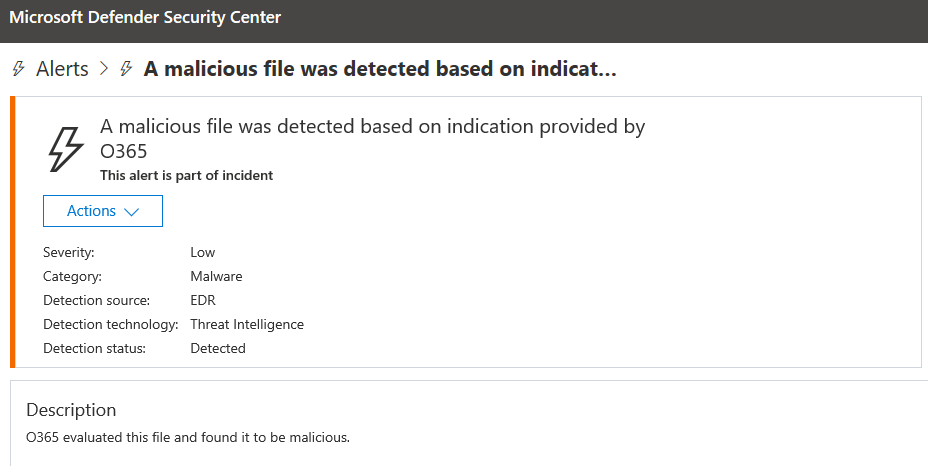
This case demonstrates how various protection components provide multiple layers of protection, enrich each other through signal-sharing, and result in overall better protection for customers. For example, even if the threat arrived outside the context of email, Microsoft Defender ATP would still block the file based on information from Office 365 ATP.
In total, on the first day of the campaign, Microsoft Defender ATP blocked the file on hundreds of machines, indicating an attack that was more targeted in nature, not a massive campaign. The attack appeared to end the next day, only to be revived and blocked on even more machines two days later. The campaign would drag on for the next couple of days.
Further analysis identified the malware as a variant of QRat, a family of remote access Trojans (RATs) also known as JRat or Adwind. If not blocked, it connects to a command-and-control server and attempts to disable antivirus software and security analysis tools. A remote attacker can command the malware to downloaded and run files, access the command line, and steal information by logging keystrokes, taking screenshots, or recording through the webcam or microphone.
Conclusion: Security signals actualized
Microsoft Defender ATP’s industry-leading visibility into threats enable security teams to detect, investigate, and respond to attacks. To continue empowering organizations to defend their organizations efficiently and confidently, we build new and richer security operations tools. Another important way that we further help security operations teams is to block and stop threats when there are enough signals for engines to accurately make a classification on a file.
Behavioral-based detection enables the blocking of new and unknown malware when suspicious behavior is observed, helping curb further malware activities on compromised machines and, as we saw in the case studies on this blog, blocking the spread of malware to other machines within the organization and beyond.
The threat landscape relentlessly serves increasingly complex threats intent on evading detection. In line with the wide-ranging innovations across Microsoft security technologies, we won’t stop improving behavioral blocking and containment capabilities to cover more scenarios and protect more customers.
Jeong Mun and Eric Avena
Microsoft Defender ATP Research Team
READ MORE HERE