Becoming resilient by understanding cybersecurity risks: Part 4—navigating current threats
In part three of this blog series on aligning security with business objectives and risk, we explored what it takes for security leaders to shift from looking at their mission as purely defending against technical attacks, to one that focuses on protecting valuable business assets, data, and applications.
As businesses begin reimagining their future in a post-pandemic world, most are pivoting to a digital-first approach to take full advantage of technological innovation (much of which was adopted in haste). The pandemic has accelerated three existing trends and the tension between them: how to remain relevant against a backdrop of consumer and market demands, how to react and respond to evolving cyber threats, and how to do this reliably while reducing complexity and cost.
Becoming a resilient organization requires collaboration between business and security leaders and a lifecycle approach to continuous improvement.
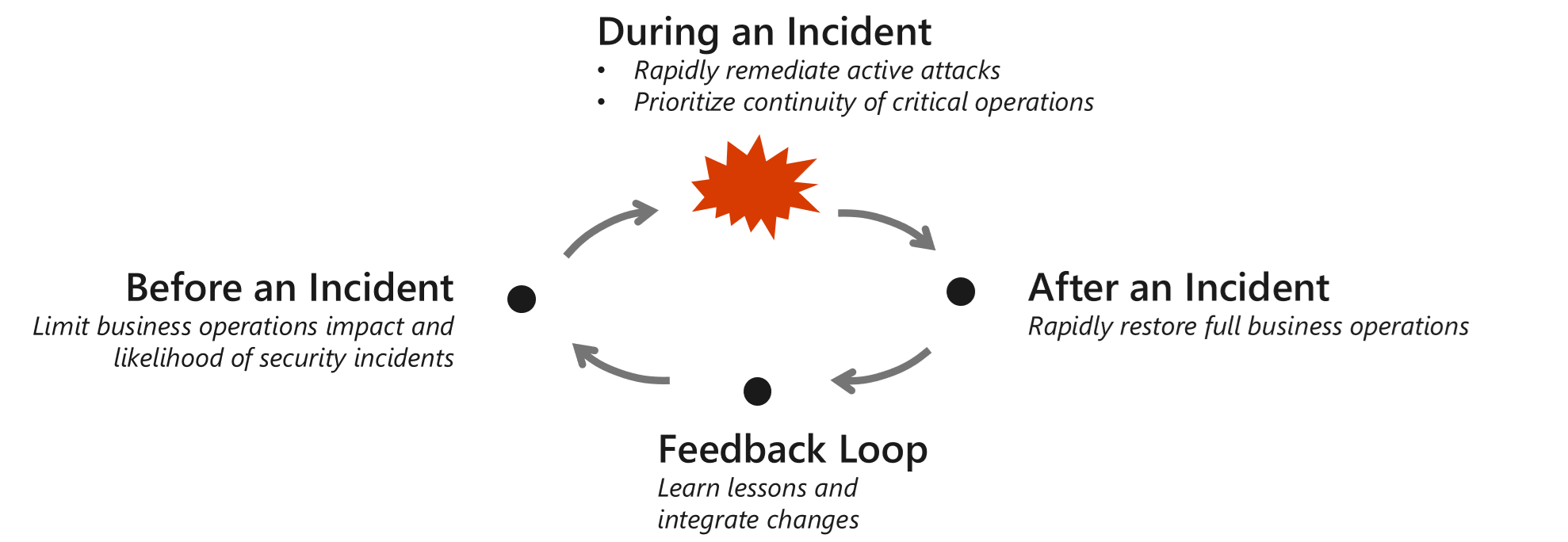
Figure 1. The cyclical stages of an incident.
In this blog, we delve deeper into specific themes in recent cyberattack trends—how and why they work so effectively—and strategies to mitigate them.
On-premises vs. cloud security
As we’ve seen from the progression of headline-grabbing attacks over the course of this blog series, today’s attackers have choices. They can remain on-premises and have a better chance of lingering unseen in the complexity of multiple generations of legacy technology, or they can elevate privileges and move to the cloud, where there’s a higher risk of detection. In the most recent nation-state attack, HAFNIUM took the path of least resistance and targeted organizations through on-premises Microsoft Exchange Servers, leveraging a zero-day exploit to gain backdoor access to data centers. After Microsoft released critical out-of-band updates, attackers were quick to seek out and compromise unpatched servers in a race to take advantage of the situation before those doors were closed.
The Exchange attack illustrates challenges faced by companies in managing a complex hybrid of on-premises and cloud that spans many generations of technology. For many organizations, it can be a costly operation to upgrade systems; so, security teams are often asked to protect both old and new technology at the same time. Organizations need to simplify the management of this complex mix because attackers are always looking for vulnerabilities. The good news is that cloud security is no longer just for cloud resources; it’s extending to cover on-premises resources, up to and including the 50 to 100-year-old operational technology (OT) equipment that’s controlled by computer technology retrofitted 30 to 50 years ago.
Your security team can reduce risk by prioritizing the cloud as the preferred source of security technology. This will simplify adoption, reduce maintenance overhead, ensure the latest innovations and capabilities, and provide unified visibility and control across multiple generations of technology. No longer are we just referring to cloud security, but rather security delivered from the cloud.
Ransomware
Criminal organizations are increasingly relying on cybercrime as a high-reward, low-risk (illicit) line of business. However, it’s the evolution of human-operated ransomware that’s now driving the business need to address longstanding security hygiene and maintenance issues. Ransomware’s evolution can be traced to WannaCry and NotPetya malware, which fused large-scale compromise techniques with an encryption payload that demanded ransom payments in exchange for a decryption key. Sometime around June 2019, the new generation of human-operated ransomware started infecting systems, expanding into an enterprise-scale operation that blends targeted attacks and extortion.
What makes human-operated ransomware so dangerous? Unlike most cyber threats, these are not preprogrammed attacks. Human attackers know the weaknesses in your networks and how to exploit them. Attacks are multistage and opportunistic—they might gain access via remote desktop protocol (RDP) brute force or through banking trojans, then decide which networks are most profitable. Like nation-state attacks, these breaches can have dwell times lasting from minutes to months. Human operators may also deliver other malicious payloads, steal credentials, or exfiltrate data. Some known human-operated ransomware campaigns that Microsoft actively monitors include REvil, Samas, Bitpaymer, and Ryuk.
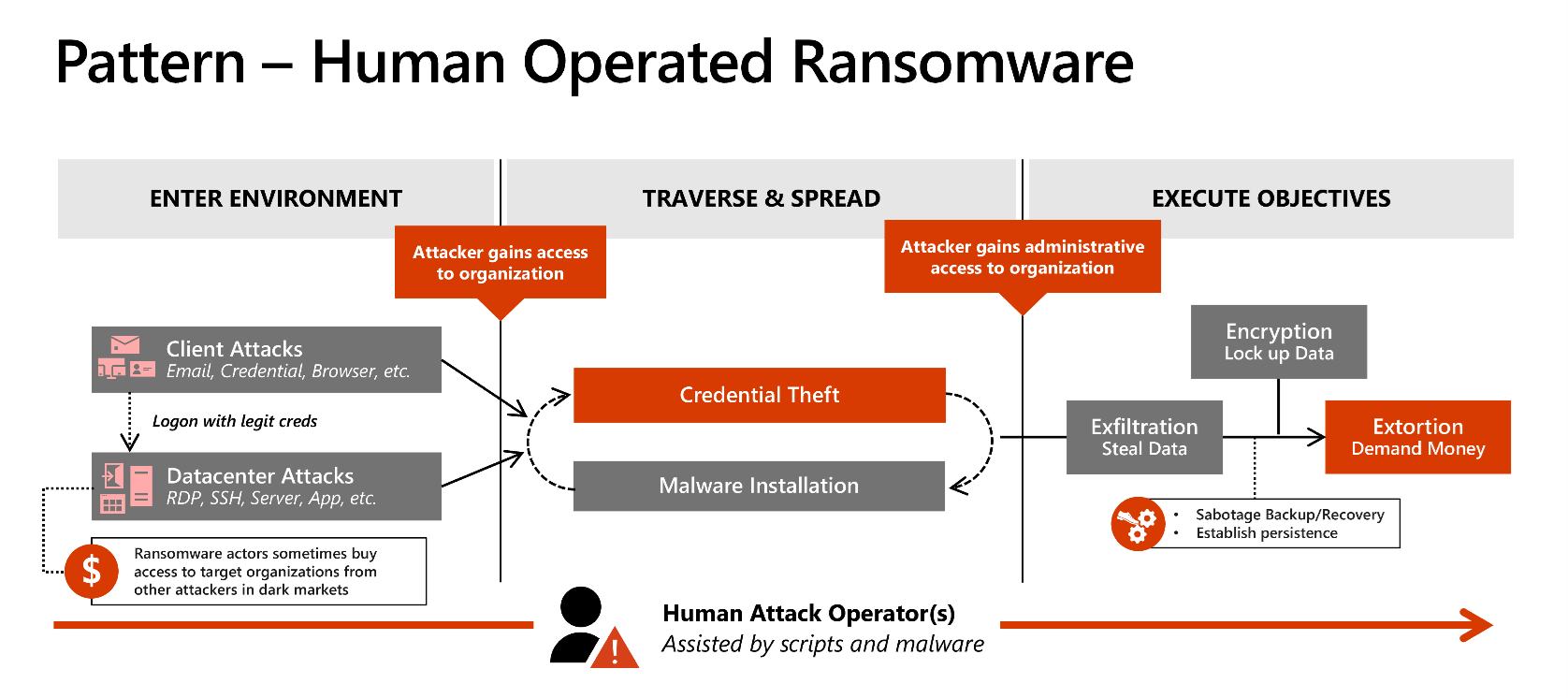
Figure 2: Human-operated ransomware—attack paths.
Human-operated ransomware is an extortion model that can use any one of multiple attack vectors. These attacks are often highly damaging and disruptive to an organization because of the combination of:
- Broad access to business-critical assets: Attackers rapidly gain broad enterprise access and control through credential theft.
- Disrupt business operations: The extortion business model requires inflicting the maximum pain on the organization (while still allowing recovery) in order to make paying the ransom attractive.
By denying access to business-critical data and systems across the enterprise, the attackers are more likely to profit, and organizations are more likely to suffer significant or material impact.
In the same way COVID-19 has shifted industry perceptions regarding bring-your-own-device (BYOD) policies and remote work, human-operated ransomware is poised to trigger seismic shifts in cybersecurity. Organizations who fail to prepare for these evolving threats face the prospect of performing mass restores of systems and data or paying the ransom (not recommended).
This is particularly true if they have any of these commonly held (and dangerous) false beliefs:
- Attackers aren’t interested in us because we’re just: a small organization, don’t have secrets, not a government, or other seemingly relevant characteristics.
- We are safe because we have firewalls.
- A password is good enough for admins; so multifactor authentication (MFA) can be deferred.
- Attackers won’t find unpatched VPNs and operating systems; so, maintenance can be deferred.
- We don’t apply security updates to internal systems like domain controllers to avoid impacting availability and performance.
- Security operations (SecOps) can manually write every alert and respond using a SIEM and a firewall; so, modernization with high-quality XDR detections and SOAR can be deferred.
If your organization is targeted, we strongly discourage paying any ransom, since this will incentivize future attacks. Also, there’s no guarantee that payment will get you the promised decryption key, or even that the attackers won’t sell your data on the dark web anyway. For a specific plan of how to address ransomware, see our downloadable Ransomware recommendations PowerPoint.
On the upside, having a business continuity and disaster recovery (BCDR) solution can provide a crucial safety net. Datto’s Global Ransomware Report 2020 indicates that three-out-of-four managed service providers (MSPs) report that clients with BCDR solutions recovered from a ransomware attack within 24 hours. However, just having a BCDR plan is not enough; you need an immutable backup that cannot be corrupted or deleted as attackers try to corrupt these backups.
This control needs to be implemented effectively across all generations of technology, including on-premises and in the cloud. Information protection and file encryption can also make data unreadable, even if exfiltrated.
Insider threats
Many data leaks can be attributed to accidents by insiders, but the risk posed by deliberate internal threats is on the rise as well—68 percent of organizations feel “moderately to extremely vulnerable” to all kinds of insider attacks. The same percentage confirms that insider attacks are becoming more frequent. Anyone who has access to an organization’s confidential data, IT, or network resources is a potential risk, whether they intend to do harm or not. This could include employees, consultants, vendors, former employees, business partners, or even a board member.
Recent examples include a former Amazon finance manager charged in a $1.4 million insider trading scheme, a Shopify data breach carried out by two employees, and an insider attack at Stradis Healthcare carried out by the former vice president of finance that “disrupted the delivery of personal protective equipment in the middle of a global pandemic.” Deliberate insider threats straddle both the physical and digital workspace, but organizations can protect themselves by looking for signs, including:
Digital warning signs
- Accessing data not associated with their job function.
- Using unauthorized storage devices.
- Network crawling and searches for sensitive data.
- Data hoarding or copying sensitive files.
- Emailing sensitive data outside the organization.
Behavioral warning signs
- Attempts to bypass security.
- Frequently in the office during off-hours.
- Displays disgruntled behavior.
- Violates corporate policies.
- Discusses resigning or new opportunities.
The key to preventing insider threats is to detect a violation before it happens. This means being empathetic to your organization’s changing environment and managing potential stressors that could lead to aberrant behavior. Being cognizant of employee wellbeing is not only in the best interests of your staff, it also drastically reduces the occurrence of insider threats for your organization. Microsoft invests in mitigating both accidental and deliberate insider threats with insider risk management, policy tips, and more.
Overcoming analyst fatigue
As the dust settles after the double-impact of the Nobelium and Hafnium attacks, we’re returning to a “normal baseline” of steadily increasing impact, volume, and sophistication of attacks. This lack of relief hits security professionals hardest, particularly analysts in security operations responding to these incidents.
The talented security professionals who silently bear the burden of attackers’ profit models often experience a high likelihood of burnout. According to PsyberResilience, the list of reasons for burnout among security professionals is long: fear of letting the organization down by missing that one threat amongst thousands every day; exhausting work schedules; fatigue from trying to keep up with new threats and technologies; the emotional toll of facing down criminals and witnessing their lack of morality.
Security teams need real help, and they need to feel supported and connected to the mission. Here are a few tips that can go a long way:
- Show your appreciation: The first minimum step for business leaders is to thank these hardworking people and get a basic understanding of what it’s like to experience these attacks from the ground level. Just as CEOs and business leaders should take time out to meet the people who make business operations work (like factory workers, truck drivers, nurses, doctors, cooks, engineers, and scientists), they should also do the same with security operations personnel to show the importance of the work to keep the organization safe every day.
- Enable automation and orchestration: This is critical to removing redundant, repetitive workflows or steps that burn up work hours and burn out employees. Azure Sentinel and Microsoft 365 Defender automate investigation and remediation tasks for many incidents, reducing the burden of repetitive work on analysts. Different security solutions in your enterprise need to see and share threat intelligence, driving a unified response across on-premises and multi-cloud environments.
- Bring in help: Many companies find it difficult to recruit and retain security professionals, especially organizations that have a smaller security team. Supplementing your team with experts from service providers can help you bring in top talent for the limited times you need them or help scale the experts you have by shifting high-volume frontline analyst work to the service provider.
- Take a collaborative approach: Reach out to peers in other industries to learn about their challenges. How do hospitals secure their patient data? How is cybersecurity done in retail operations, airlines, or government offices? Looking into different verticals might offer some new ideas and inspiration. An army of interconnected defenders provides more clarity and oversight than any single organization can maintain. For more technical information about how this works, learn about the community-based approach to information security.
Augmented intelligence and deepfakes
Using machine learning and automation has proven to be an incredible tool for defenders to detect and respond to threats faster. However, attackers also have access to similar technology and are leveraging this to their advantage. In another example of the cyber and physical worlds coming together, cybercriminals were able to create a near-perfect impersonation of a chief executive’s voice using deepfake technology—tricking the company into transferring $243,000 to their bank account. Attackers combined machine learning and AI with social engineering to convince people to move the money.
While still rare, AI and machine learning attacks like this are becoming more common. Attackers can make deepfake using public recordings of their target from earnings calls, interviews, and speeches, mimicking their mannerisms and using the technology as a kind of mask. Despite the advanced technology required for one of these attacks, the defense may be refreshingly straightforward and non-technical—if in doubt, call the person back. Using a secondary authentication for high-value transactions can also provide an additional secure step in the approval process, making it difficult for attackers to anticipate and fake out all of the channels at once.
With the use of AI and machine learning becoming more prolific in the defender’s kit bag, cybercriminals have also taken to attacking and poisoning the algorithms that are used to detect anomalies; often flooding the algorithm with data to skew results or generate false positives. In short, the human intelligence layer remains critical to providing contextual awareness and understanding of new cyber threats, helping to decipher the evolving tactics and techniques designed to evade detection.
Stay tuned
The next post in this series will focus on how your organization can pull all these concepts together into a security strategy that integrates with your business priorities, risk frameworks, and processes.
If you want to read ahead, you can check out the secure methodology in the cloud adoption framework.
Learn more
Read the previous blogs in this series:
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE