Becoming resilient by understanding cybersecurity risks: Part 1
All risks have to be viewed through the lens of the business or organization. While information on cybersecurity risks is plentiful, you can’t prioritize or manage any risk until the impact (and likelihood) to your organization is understood and quantified.
This rule of thumb on who should be accountable for risk helps illustrate this relationship:
The person who owns (and accepts) the risk is the one who will stand in front of the news cameras and explain to the world why the worst case scenario happened.
This is the first in a series of blogs exploring how to manage challenges associated with keeping an organization resilient against cyberattacks and data breaches. This series will examine both the business and security perspectives and then look at the powerful trends shaping the future.
This blog series is unabashedly trying to help you build a stronger bridge between cybersecurity and your organizational leadership.
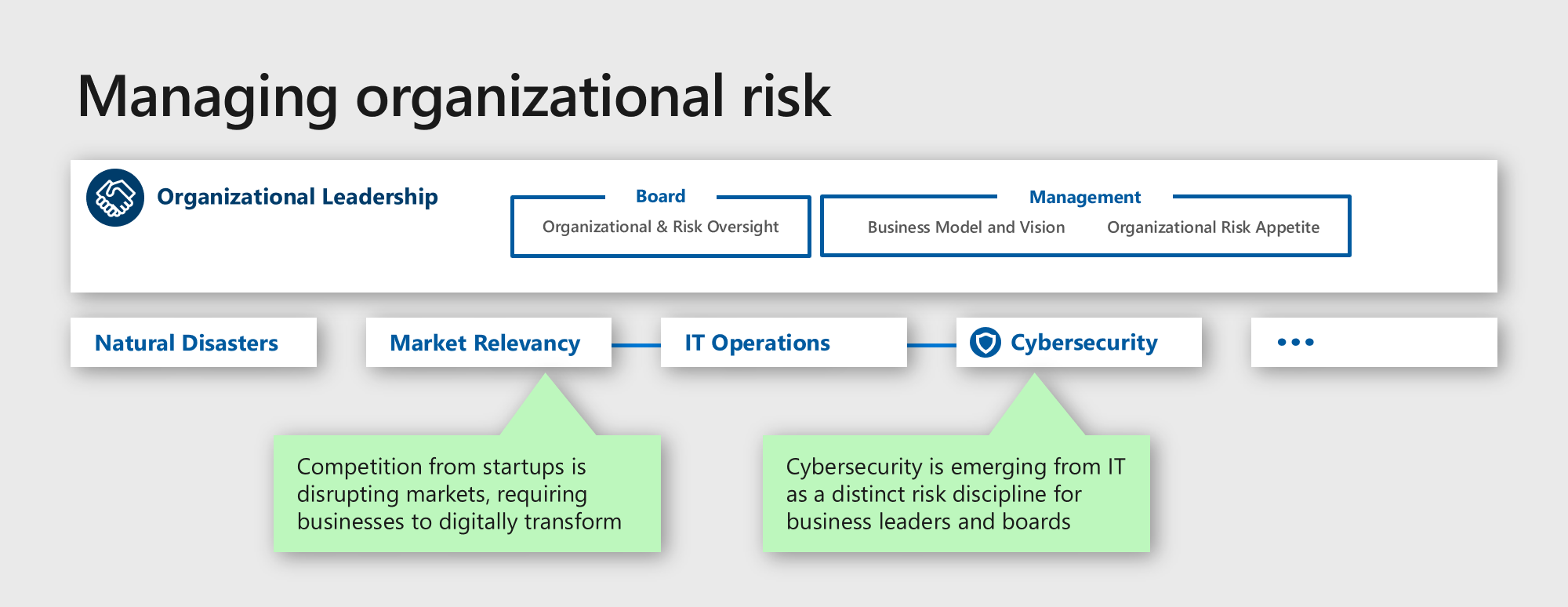
Organizations face two major trends driving both opportunity and risk:
- Digital disruption: We are living through the fourth industrial revolution, characterized by the fusion of the physical, biological, and digital worlds. This is having a profound impact on all of us as much as the use of steam and electricity changed the lives of farmers and factory owners during early industrialization.
Tech-disruptors like Netflix and Uber are obvious examples of using the digital revolution to disrupt existing industries, which spurred many industries to adopt digital innovation strategies of their own to stay relevant. Most organizations are rethinking their products, customer engagement, and business processes to stay current with a changing market. - Cybersecurity: Organizations face a constant threat to revenue and reputation from organized crime, rogue nations, and freelance attackers who all have their eyes on your organization’s technology and data, which is being compounded by an evolving set of insider risks.
Organizations that understand and manage risk without constraining their digital transformation will gain a competitive edge over their industry peers.
Cybersecurity is both old and new
As your organization pulls cybersecurity into your existing risk framework and portfolio, it is critical to keep in mind that:
- Cybersecurity is still relatively new: Unlike responding to natural disasters or economic downturns with decades of historical data and analysis, cybersecurity is an emerging and rapidly evolving discipline. Our understanding of the risks and how to manage them must evolve with every innovation in technology and every shift in attacker techniques.
- Cybersecurity is about human conflict: While managing cyber threats may be relatively new, human conflict has been around as long as there have been humans. Much can be learned by adapting existing knowledge on war, crime, economics, psychology, and sociology. Cybersecurity is also tied to the global economic, social, and political environments and can’t be separated from those.
- Cybersecurity evolves fast (and has no boundaries): Once a technology infrastructure is in place, there are few limits on the velocity of scaling an idea or software into a global presence (whether helpful or malicious), mirroring the history of rail and road infrastructures. While infrastructure enables commerce and productivity, it also enables criminal or malicious elements to leverage the same scale and speed in their actions. These bad actors don’t face the many constraints of legitimate useage, including regulations, legality, or morality in the pursuit of their illicit goals. These low barriers to entry on the internet help to increase the volume, speed, and sophistication of cyberattack techniques soon after they are conceived and proven. This puts us in the position of continuously playing catch up to their latest ideas.
- Cybersecurity requires asset maintenance: The most important and overlooked aspect of cybersecurity is the need to invest in ‘hygiene’ tasks to ensure consistent application of critically important practices.
One aspect that surprises many people is that software ‘ages’ differently than other assets and equipment, silently accumulating security issues with time. Like a brittle metal, these silent issues suddenly become massive failures when attackers find them. This makes it critical for proactive business leadership to proactively support ongoing technology maintenance (despite no previous visible signs of failure).
Stay pragmatic
In an interconnected world, a certain amount of playing catch-up is inevitable, but we should minimize the impact and probabilities of business impact events with a proactive stance.
Organizations should build and adapt their risk and resilience strategy, including:
- Keeping threats in perspective: Ensuring stakeholders are thinking holistically in the context of business priorities, realistic threat scenarios, and reasonable evaluation of potential impact.
- Building trust and relationships: We’ve learned that the most important cybersecurity approach for organizations is to think and act symbiotically—working in unison with a shared vision and goal.
Like any other critical resource, trust and relationships can be strained in a crisis. It’s critical to invest in building strong and collaborative relationships between security and business stakeholders who have to make difficult decisions in a complex environment with incomplete information that is continuously changing. - Modernizing security to protect business operations wherever they are: This approach is often referred to as Zero Trust and helps security enable the business, particularly digital transformation initiatives (including remote work during COVID-19) versus the traditional role as an inflexible quality function.
One organization, one vision
As organizations become digital, they effectively become technology companies and inherit both the natural advantages (customer engagement, rapid scale) and difficulties (maintenance and patching, cyberattack). We must accept this and learn to manage this risk as a team, sharing the challenges and adapting to the continuous evolution.
In the coming blogs, we will explore these topics from the perspective of business leaders and from cybersecurity leaders, sharing lessons learned on framing, prioritizing, and managing risk to stay resilient against cyberattacks.
To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
READ MORE HERE