Automating your Microsoft security suite with D3 XGEN SOAR
This blog post is part of the Microsoft Intelligent Security Association guest blog series. Learn more about MISA.
There are certain pain points in the average security operations center (SOC) that, no matter what else changes in the security landscape, stay among the most entrenched problems. You can probably name them off the top of your head: an overwhelming amount of security alerts; the ongoing shortage of skilled cybersecurity professionals; the inability to detect and respond to increasingly sophisticated attacks; and the proliferation of tools (76 in the average enterprise SOC) that do not always work well together.1 But these challenges have something else in common other than being the primary causes of headaches among security pros: they are all alleviated by security orchestration, automation, and response—better known as SOAR.2 Learn how D3 Security’s XGEN SOAR integrates with Microsoft Sentinel and hundreds of other tools to help customers overcome SOC Analyst fatigue and disparate toolsets in this blog post.
What is SOAR?
Let’s start with the basics. SOAR is a category of powerful tools that integrate with other security systems, such as security information and event management (SIEM), endpoint detection and response (EDR), and firewalls, to ingest alerts, enrich them with contextual intelligence, and orchestrate remediation actions across the environment. SOAR tools use playbooks to automate and codify workflows to accelerate mean time to respond (MTTR) and standardize responses to common incident types.
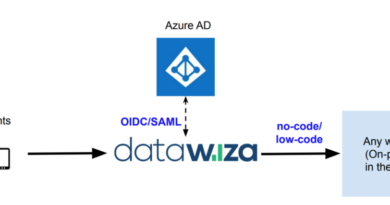
D3 XGEN SOAR is a fully vendor-agnostic SOAR solution, which means it can maintain dozens of deep integrations with Microsoft tools—including Sentinel—and bring automation to security workflows in any environment.
How Microsoft Sentinel customers use D3’s Event Pipeline to stay focused on real threats
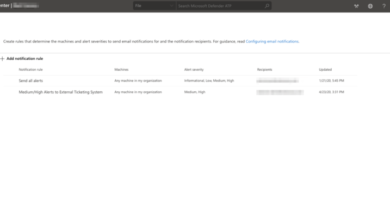
What does integrating D3 XGEN SOAR with Microsoft tools mean for customers? Let’s take one narrow example and look at how D3’s Event Pipeline—a unique offering among SOAR platforms—acts on Microsoft Sentinel events to make the lives of security analysts much easier.3
D3 ingests Microsoft Sentinel events for investigation and response. But as any SIEM operator knows, it is a delicate balance to configure your SIEM, and other alert-generating tools, so that you are capturing all the important incidents without an overwhelming amount of noise. That’s where D3’s Event Pipeline comes in.

When a Microsoft Sentinel event comes into D3, it goes through the Event Pipeline, a global automated playbook that acts on every incoming event or alert from a detection tool. The Event Pipeline works in three stages:
- First, the data from the incoming event is normalized. The artifacts, such as IP addresses, user IDs, and URLs, are extracted, and metadata tagging is performed.
- Next is the triage stage. The event is deduplicated and correlated against other events. The artifacts are checked against integrated threat intelligence sources to determine risk, and MITRE ATT&CK tactic, technique, and procedure (TTP) labels are applied.
- In the final stage, the Microsoft Sentinel event is either dismissed as a false positive or escalated and assigned to an analyst. Dismissal and escalation rules are set by the user, based on criteria such as the risk scores from threat intelligence enrichment or the presence of key assets in the artifacts.
The result of adding D3’s Event Pipeline to Microsoft Sentinel incident investigations is that 90 percent or more of Microsoft Sentinel events can be safely filtered out before they reach a human analyst, allowing the genuine threats to be properly investigated.
Key Microsoft integrations
D3’s integration with Microsoft Sentinel is just one of 33 integrations between D3 XGEN SOAR and Microsoft tools. Twenty-two of those integrations are from the Azure suite. Some of the key integrations for common security operations use cases include Microsoft Defender for Endpoint, Microsoft 365, and Azure Active Directory (Azure AD).
Microsoft Defender for Endpoint
Microsoft Defender users can orchestrate 26 different actions from D3, including fetching events, enriching incidents with endpoint data, and quarantining infected hosts. This creates an automation-powered process for any endpoint security incident that acts quickly and conclusively before threats get out of control.
Microsoft 365
Phishing is still the entry point for most cyberattacks, which makes email a critical part of cybersecurity incident response. When a potential phishing email is detected, D3 can retrieve the email and attachments, parse out the artifacts, check the reputations of the artifacts against threat intelligence and past incidents, and determine if the email is a genuine threat. If it is, D3 can then find other instances of the email across the company’s inboxes and delete them.
Azure Active Directory
You may have heard it said that “identity is the new perimeter,” which underscores the importance of being able to act quickly in Azure AD during a security incident. Companies using Azure AD (and on-premises AD) can enrich D3 incidents with user and group information, manage users and groups from D3, and quickly orchestrate remediation actions like forcing a password reset or revoking a sign-in session.
Security orchestration for MSSPs
Managed security service providers (MSSPs) get similar benefits from D3 and Microsoft’s joint solutions as SOCs do, but at a greater scale.4 At D3, they have found that MSSPs are not always given direct access to all their clients’ tools, or they may not want to become experts in every single tool their clients use if all they’re doing with those tools is managing alerts. Instead, clients give their MSSP access to D3, from which they can manage the alerts from all their detection tools from a single interface.
This makes D3 a useful operations hub for MSSPs with clients that rely on Azure systems or other Microsoft tools. The MSSP can leverage D3’s integrations with Microsoft Sentinel, Microsoft Defender for Endpoint, Microsoft 365, and others, to handle alerts and even orchestrate response actions—without needing full access to their clients’ tools.5 The Event Pipeline is also a valuable tool in this scenario, allowing MSSPs to handle a much higher volume of alerts, without adding resources.
Better together: Use cases for Microsoft and D3 XGEN SOAR
Use case 1: Investigation and orchestration across hybrid environments

More companies are moving their systems and servers to cloud services like Microsoft Azure, but many retain a hybrid environment, with some systems still hosted on-premises. This hybrid model creates an issue around security because the company is left managing two sets of security tools—one in the cloud and one on-premises.
D3 can integrate with Microsoft Sentinel, 21 other tools in the Azure stack, and hundreds of on-premise tools to create a single security operations (SecOps) interface for the entire hybrid environment. Joint users of Microsoft Sentinel and D3 can enrich alerts with threat intelligence, identify MITRE ATT&CK techniques, run automation-powered playbooks to respond to incidents, and much more—across cloud and on-premise systems simultaneously.
For example, in a phishing attack that resulted in a potentially infected endpoint, an analyst using D3 could disable the user’s access in Azure AD, query Microsoft Sentinel for additional data, search across Microsoft 365 mailboxes for more instances of the phishing email and quarantine the affected endpoint using Microsoft Defender for Endpoint.6
Having D3 SOAR integrated with both your Azure tools and your on-premise tools can reduce your work—and your risk—by half. Because of the ability to monitor and act across your entire hybrid environment, you will not lose sight of incidents that move between environments, and you will always be able to execute your entire response without having to switch between tools.
Use case 2: Compromised credentials

When an employee’s credentials are compromised, hacked, or leaked, they can turn up on lists provided by threat intelligence platforms. Security teams need ways to streamline their ability to learn of compromised credentials, match the credentials to the employee’s other information, determine which machines the credentials could be used on, and take action to prevent unauthorized access. D3 integrates with AD (Azure or on-premise), threat intelligence platforms, and other tools, to orchestrate this process.
D3 can ingest lists of leaked credentials from integrated threat intelligence platforms. When an employee’s credentials are included in a list, D3 can query Active Directory to match the credentials to other information related to the employee, including the list of machines to which they have access. D3 can get the user’s login history from Active Directory to look for unusual activity, temporarily deactivate the user if necessary, and orchestrate a password change.
The sky’s the limit
These are just a couple of the use cases that D3 users can orchestrate across their Microsoft tools and systems. With more than 30 integrations and hundreds of commands, there is an extremely high ceiling on what sophisticated users can accomplish with D3 and Microsoft’s combined capabilities. Don’t let that intimidate you though. With codeless, out-of-the-box playbooks for common incident types, even less technical users can immediately realize the benefits of the joint solutions.
About D3 Security
D3 Security’s XGEN SOAR platform combines automation and orchestration across more than 500 integrated tools with an automated event pipeline that reduces event volume by 90 percent or more.2 D3’s codeless playbooks automate enrichment and remediation tasks while making it easy for anyone to build, modify, and scale workflows for security operations, incident response, and threat hunting.
With more than 30 Microsoft integrations, D3 Security has been a Microsoft Intelligent Security Association (MISA) member since 2020. Visit the Azure Marketplace page here. You can learn more about how D3 works with Microsoft on D3’s technology partners page.5
Learn more
To learn more about MISA, visit our MISA website where you can learn about the MISA program, product integrations, and find MISA members. Visit the video playlist to learn about the strength of member integrations with Microsoft products.
To learn more about Microsoft Security solutions, visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
1 Security leaders are still in the dark with asset visibility while a lack of insight is driving control failures, Panaseer. 2022.
2 XGEN SOAR platform, D3 Security.
3 XGEN SOAR Event Pipeline, D3 Security.
4 Security Automation and Orchestration for MSSPs, D3 Security.
5 Microsoft Azure Sentinel Integration, D3 Security.
6 D3 XGEN SOAR for Phishing Attacks, D3 Security.
READ MORE HERE