Automated incident response in Office 365 ATP now generally available
Security teams responsible for investigating and responding to incidents often deal with a massive number of signals from widely disparate sources. As a result, rapid and efficient incident response continues to be the biggest challenge facing security teams today. The sheer volume of these signals, combined with an ever-growing digital estate of organizations, means that a lot of critical alerts miss getting the timely attention they deserve. Security teams need help to scale better, be more efficient, focus on the right issues, and deal with incidents in a timely manner.
This is why I’m excited to announce the general availability of Automated Incident Response in Office 365 Advanced Threat Protection (ATP). Applying these powerful automation capabilities to investigation and response workflows can dramatically improve the effectiveness and efficiency of your organization’s security teams.
A day in the life of a security analyst
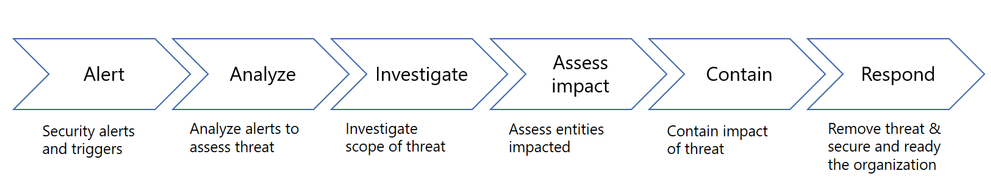
To give you an idea of the complexity that security teams deal with in the absence of automation, consider the following typical workflow that these teams go through when investigating alerts:
And as they go through this flow for every single alert—potentially hundreds in a week—it can quickly become overwhelming. In addition, the analysis and investigation often require correlating signals across multiple different systems. This can make effective and timely response very difficult and costly. There are just too many alerts to investigate and signals to correlate for today’s lean security teams.
To address these challenges, earlier this year we announced the preview of powerful automation capabilities to help improve the efficiency of security teams significantly. The security playbooks we introduced address some of the most common threats that security teams investigate in their day-to-day jobs and are modeled on their typical workflows.
This story from Ithaca College reflects some of the feedback we received from customers of the preview of these capabilities, including:
“The incident detection and response capabilities we get with Office 365 ATP give us far more coverage than we’ve had before. This is a really big deal for us.”
—Jason Youngers, Director and Information Security Officer, Ithaca College
Two categories of automation now generally available
Today, we’re announcing the general availability of two categories of automation—automatic and manually triggered investigations:
- Automatic investigations that are triggered when alerts are raised—Alerts and related playbooks for the following scenarios are now available:
- User-reported phishing emails—When a user reports what they believe to be a phishing email, an alert is raised triggering an automatic investigation.
- User clicks a malicious link with changed verdict—An alert is raised when a user clicks a URL, which is wrapped by Office 365 ATP Safe Links, and is determined to be malicious through detonation (change in verdict). Or if the user clicks through the Office 365 ATP Safe Links warning pages an alert is also raised. In both cases, the automated investigation kicks in as soon as the alert is raised.
- Malware detected post-delivery (Malware Zero-Hour Auto Purge (ZAP))—When Office 365 ATP detects and/or ZAPs an email with malware, an alert triggers an automatic investigation.
- Phish detected post-delivery (Phish ZAP)—When Office 365 ATP detects and/or ZAPs a phishing email previously delivered to a user’s mailbox, an alert triggers an automatic investigation.
- Manually triggered investigations that follow an automated playbook—Security teams can trigger automated investigations from within the Threat Explorer at any time for any email and related content (attachment or URLs).
Rich security playbooks
In each of the above cases, the automation follows rich security playbooks. These playbooks are essentially a series of carefully logged steps to comprehensively investigate an alert and offer a set of recommended actions for containment and mitigation. They correlate similar emails sent or received within the organization and any suspicious activities for relevant users. Flagged activities for users might include mail forwarding, mail delegation, Office 365 Data Loss Prevention (DLP) violations, or suspicious email sending patterns.
In addition, aligned with our Microsoft Threat Protection promise, these playbooks also integrate with signals and detections from Microsoft Cloud App Security and Microsoft Defender ATP. For instance, anomalies detected by Microsoft Cloud App Security are ingested as part of these playbooks. And the playbooks also trigger device investigations with Microsoft Defender ATP (for malware playbooks) where appropriate.
Let’s look at each of these automation scenarios in detail:
User reports a phishing email—This represents one of the most common flows investigated today. The alert is raised when a user reports a phish email using the Report message add-in in Outlook or Outlook on the web and triggers an automatic investigation using the User Reported Message playbook.
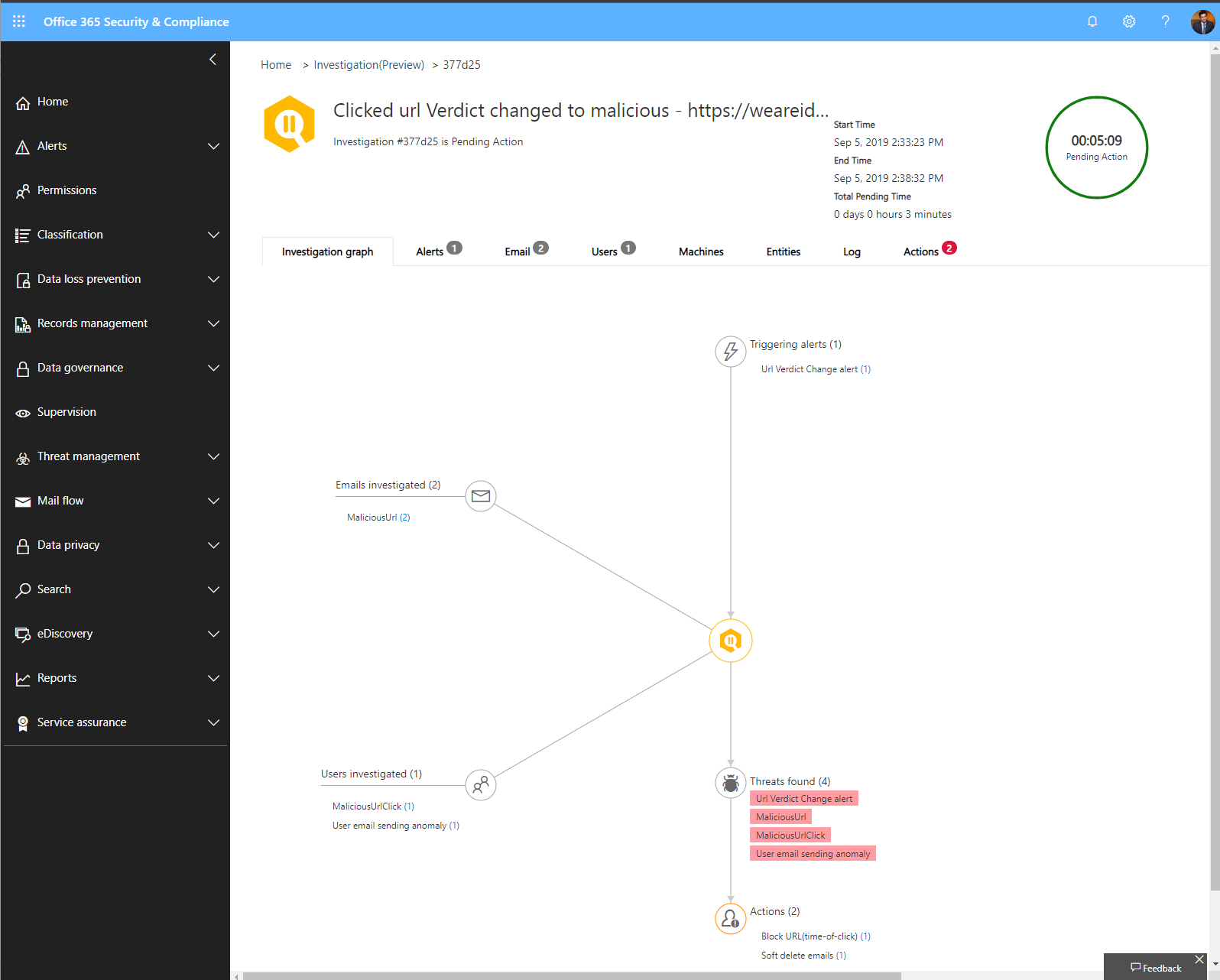
User clicks on a malicious link—A very common vector used by attackers is to weaponize a link after delivery of an email. With Office 365 ATP Safe Links protection, we can detect such attacks when links are detonated at time-of-click. A user clicking such links and/or overriding the Safe Links warning pages is at risk of compromise. The alert raised when a malicious URL is clicked triggers an automatic investigation using the URL verdict change playbook to correlate any similar emails and any suspicious activities for the relevant users across Office 365.
Email messages containing malware removed after delivery—One of the critical pillars of protection in Office 365 Exchange Online Protection (EOP) and Office 365 ATP is our capability to ZAP malicious emails. Email messages containing malware removed after delivery alert trigger an investigation into similar emails and related user actions in Office 365 for the period when the emails were present in a user’s inbox. In addition, the playbook also triggers an investigation into the relevant devices for the users by leveraging the native integration with Microsoft Defender ATP.
Email messages containing phish removed after delivery—With the rise in phishing attack vectors, Office 365 EOP and Office 365 ATP’s ability to ZAP malicious emails detected after delivery is a critical protection feature. The alert raised triggers an investigation into similar emails and related user actions in Office 365 for the period when the emails were present in a user’s inbox and also evaluates if the user clicked any of the links.
Automated investigation triggered from within the Threat Explorer—As part of existing hunting or security operations workflows, Security teams can also trigger automated investigations on emails (and related URLs and attachments) from within the Threat Explorer. This provides Security Operations (SecOps) a powerful mechanism to gain insights into any threats and related mitigations or containment recommendations from Office 365.
Try out these capabilities
Based on feedback from our public preview of these automation capabilities, we extended the Office 365 ATP events and alerts available in the Office 365 Management API to include links to these automated investigations and related artifacts. This helps security teams integrate these automation capabilities into existing security workflow solutions, such as SIEMs.
These capabilities are available as part of the following offerings. We hope you’ll give it a try.
Bringing SecOps efficiency by connecting the dots between disparate threat signals is a key promise of Microsoft Threat Protection. The integration across Microsoft Threat Protection helps bring broad and valuable insights that are critical to the incident response process. Get started with a Microsoft Threat Protection trial if you want to experience the comprehensive and integrated protection that Microsoft Threat Protection provides.
READ MORE HERE